Preface: Packet filtering are divided into two categories :
- Stateless (Packet filtering) – Stateless is the polar opposite of stateful
- Stateful (Packet filtering)
Stateless (Packet filtering): It is also known as an access control list (ACL), does not store information on the connection state. Stateless ACLs are applicable to the network and physical layers, and sometimes the transport layer to find out the source and destination port numbers. When the sender sends a packet and gets filtered through a filter, the device checks for matches to any of the ACL rules that are configured in the filter and then drops or rejects the packet accordingly.
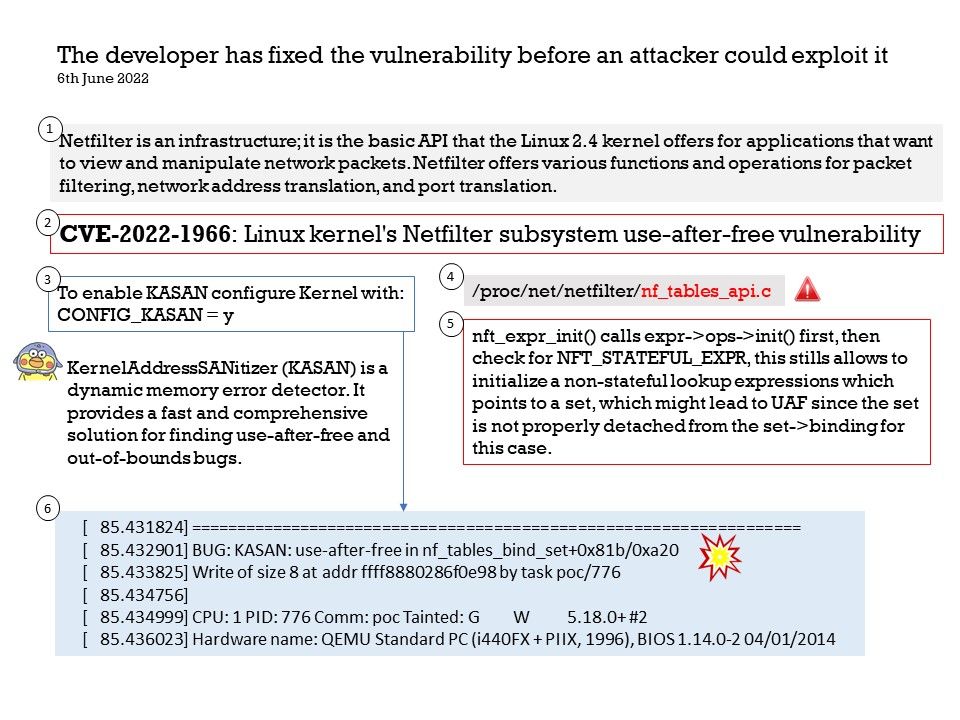
Background: Netfilter is an infrastructure; it is the basic API that the Linux 2.4 kernel offers for applications that want to view and manipulate network packets. Netfilter offers various functions and operations for packet filtering, network address translation, and port translation.
Vulnerability details: A use-after-free vulnerability was found in the Linux kernel’s Netfilter subsystem in net/netfilter/nf_tables_api[.]c. This flaw allows a local attacker with user access to cause a privilege escalation issue.
Remark: nft_expr_init() calls expr->ops->init() first, then check for NFT_STATEFUL_EXPR, this stills allows to initialize a non-stateful lookup expressions which points to a set, which might lead to UAF since the set is not properly detached from the set->binding for this case. The specific debugging method is shown in the attached drawing.
Red Hat Bugzilla – Bug 2092427
Bug 2092427 (CVE-2022-1966) – CVE-2022-1966 kernel: a use-after-free write in the netfilter subsystem can lead to privilege escalation to root
Please refer to the link for details – https://bugzilla.redhat.com/show_bug.cgi?id=2092427