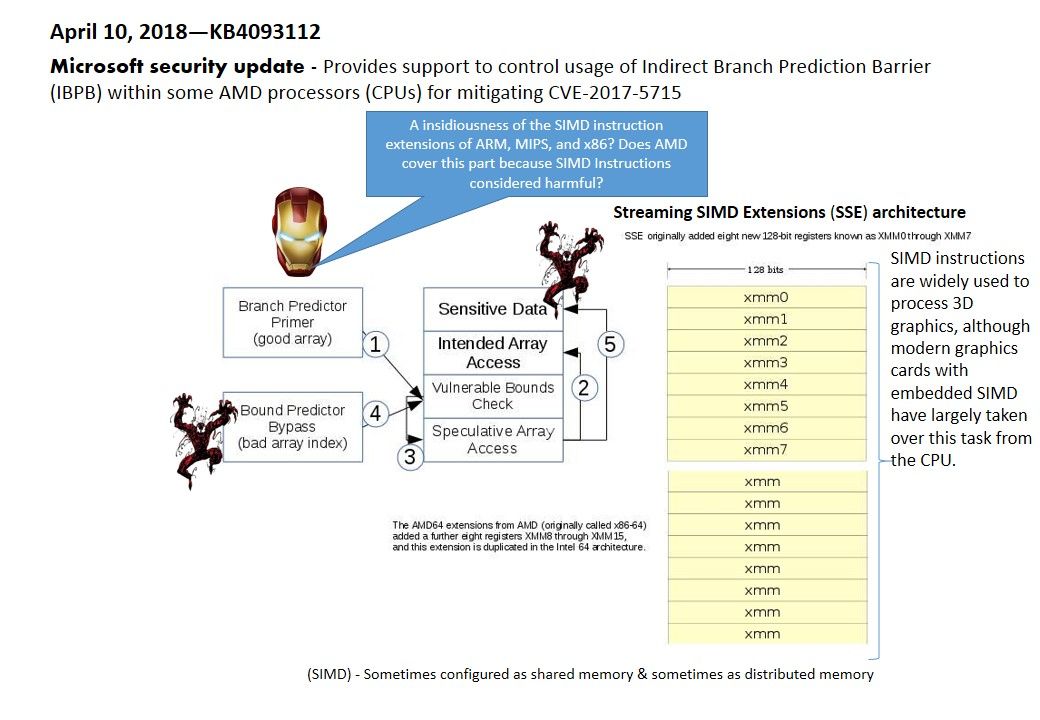
The security update of Microsoft this week included provides support to control usage of Indirect Branch Prediction Barrier (IBPB) within some AMD processors (CPUs) for mitigating CVE-2017-5715. Apart from that it also provides Windows Client Guidance for IT Pros to protect against speculative execution side-channel vulnerabilities. However I was wondering the mitigation plan coverage provided by AMD?
A insidiousness of the SIMD instruction extensions of ARM, MIPS, and x86? Does AMD cover this part because SIMD Instructions considered harmful?Any advice or we just ignore it?
For more details about the security update, please refer below url for references.
Windows Client Guidance for IT Pros to protect against speculative execution side-channel vulnerabilities – https://support.microsoft.com/en-hk/help/4073119/protect-against-speculative-execution-side-channel-vulnerabilities-in
KB4093112 – https://www.catalog.update.microsoft.com/Search.aspx?q=KB4093112
Hi All im noob here. Good post! Thx! Thx!