Microsoft Patch Tue transform to weekly routine security process. As far as I know, IT technical experts are busy for change management control schedule (time window) weekly. For the evaluation of each vulnerability most likely will be do a quick walk-through. As a matter of fact, engage the patch updating exercise looks time consuming. IT Dept will be do the patch management out of office hour, earlier morning or Sunday morning. But think it over, our existing business world seems operate in 24 hours. Another new round of patch announcement will be held on coming Tue. And therefore implement managed security services become a significant pathway.
Remark: We are all under demanding competitions environment!
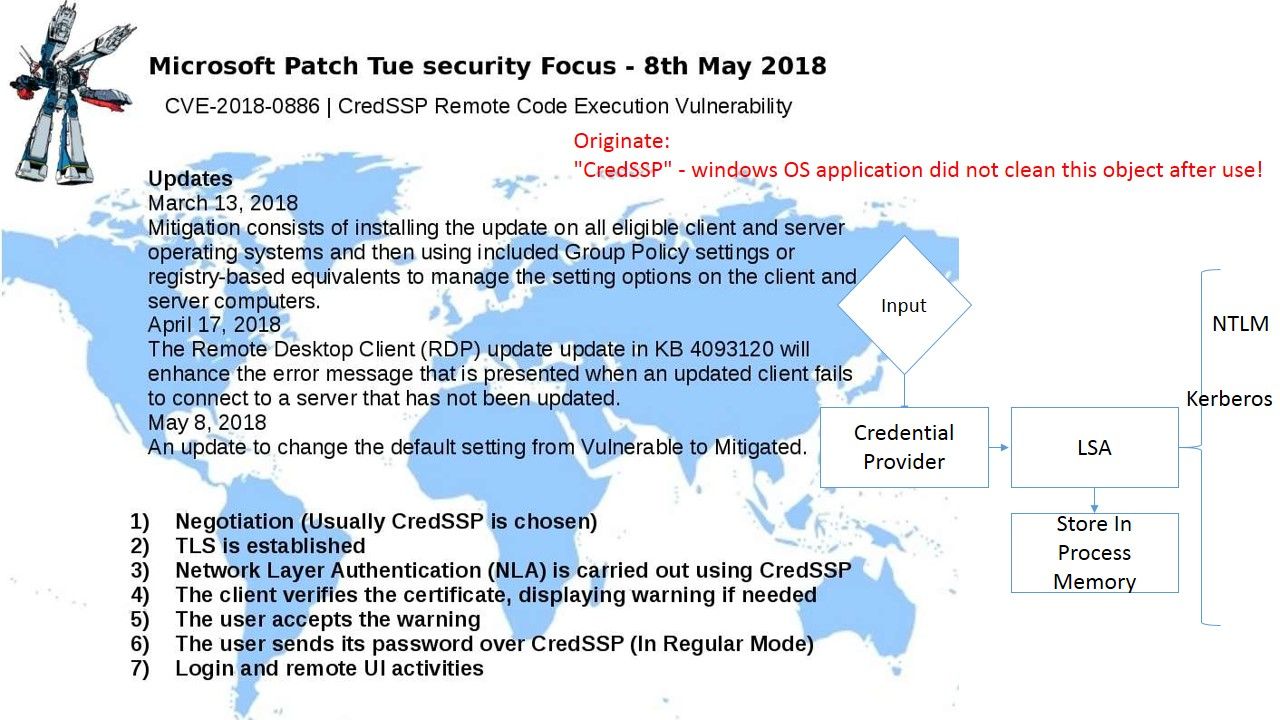
CredSSP updates for CVE-2018-0886
My security focus for Microsoft Patch Tue this week will be observe the vulnerability of Credential Security Support Provider protocol. Regarding to my observation, vendor doing 3 times of security enhancement last 3 months. For details, please refer to diagram above.
The spectra and meltdown vulnerabilities found this year bring the people focus to CPU design architecture. As a matter of fact, memory management looks critical today because of APT attack. Heterogeneous systems that integrate a multicore CPU and a GPU on the same die are ubiquitous. On these systems, both the CPU and GPU share the same physical memory as opposed to using separate memory dies.
In order to avoid Credential Theft , what is the Secure practice?
- Prevent network logon for local accounts
- Prevent credentials from remaining in-memory when connecting remotely (out of IT operation control)
- Prevent access to in-memory credentials (Control by application developers)
- Leverage protected users and control privileged users
In short, please refer to Microsoft official announcement for reference.
https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2018-0886