Preface: Decentralized AI is an approach to AI where the data and models are distributed across multiple devices, rather than being centralized in a single location. Such design benefits to AI infrastructure avoiding denial of service attack and let unknown technical matter occurs during this period.
Background: Internet Computing aims to extend the capabilities of the public Internet through a serverless cloud model. Serverless is a cloud computing application development and execution model that enables developers to build and run application code without provisioning or managing servers or backend infrastructure.
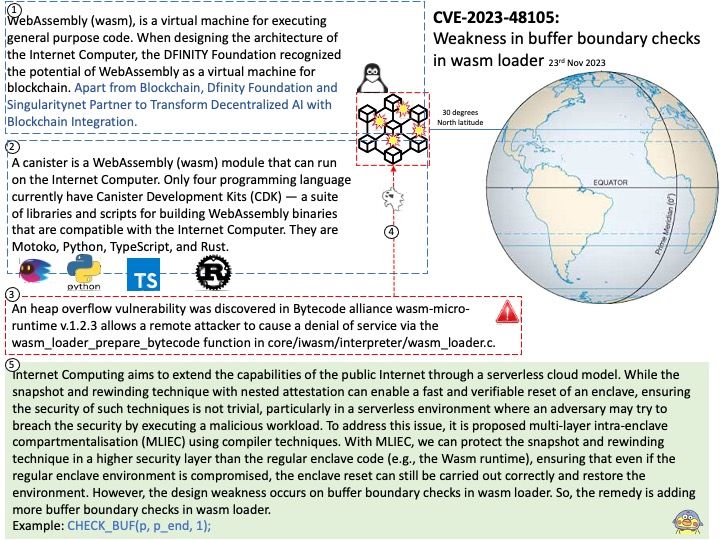
WebAssembly (wasm), is a virtual machine for executing general purpose code. When designing the architecture of the Internet Computer, the DFINITY Foundation recognized the potential of WebAssembly as a virtual machine for blockchain. Apart from Blockchain, Dfinity Foundation and Singularitynet Partner to Transform Decentralized AI with Blockchain Integration.
A canister is a WebAssembly (wasm) module that can run on the Internet Computer. Only four programming language currently have Canister Development Kits (CDK) — a suite of libraries and scripts for building WebAssembly binaries that are compatible with the Internet Computer. They are Motoko, Python, TypeScript, and Rust.
Note: As shown above, it shows the future sustainability of Python. There is no doubt that Python can be expanded into the world of artificial intelligence.
Vulnerability details: An heap overflow vulnerability was discovered in Bytecode alliance wasm-micro-runtime v.1.2.3 allows a remote attacker to cause a denial of service via the wasm_loader_prepare_bytecode function in core/iwasm/interpreter/wasm_loader[.]c.
Additional: Internet Computing aims to extend the capabilities of the public Internet through a serverless cloud model. While the snapshot and rewinding technique with nested attestation can enable a fast and verifiable reset of an enclave, ensuring the security of such techniques is not trivial, particularly in a serverless environment where an adversary may try to breach the security by executing a malicious workload. To address this issue, it is proposed multi-layer intra-enclave compartmentalisation (MLIEC) using compiler techniques. With MLIEC, we can protect the snapshot and rewinding technique in a higher security layer than the regular enclave code (e.g., the Wasm runtime), ensuring that even if the regular enclave environment is compromised, the enclave reset can still be carried out correctly and restore the environment. However the design weakness occurs on buffer boundary checks in wasm loader. So, the remedy is adding more buffer boundary checks in wasm loader. Example: CHECK_BUF(p, p_end, 1);
Official announcement: Please refer to the link for details – https://nvd.nist.gov/vuln/detail/CVE-2023-48105