Preface: This design weakness was released 30th Jan 2023. However, this vulnerability is known as CVE-2022-42292 since 10/03/2022. But it already been fixed.
Background: The GeForce Experience features a host of performance and configuration tweaks for games, automatic driver updates for your GPU, Nvidia Shadowplay for live streaming, integrated game filters (like Instagram filters but for your PC games), and many more powerful options.
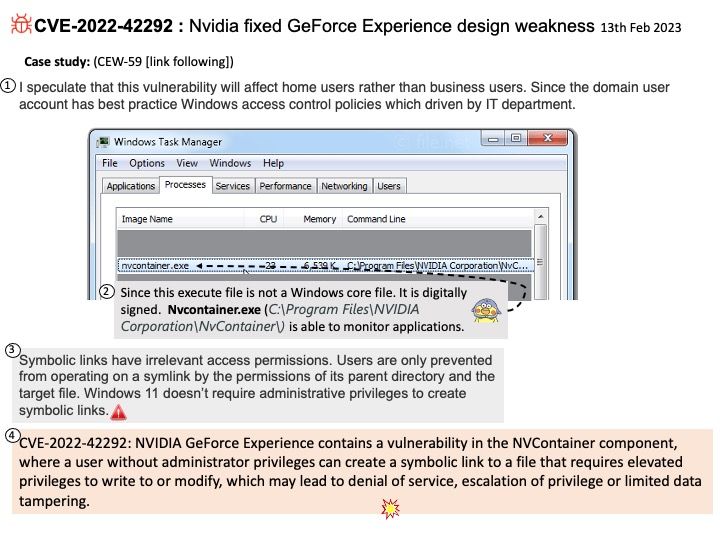
Vulnerability details: NVIDIA GeForce Experience contains a vulnerability in the NVContainer component, where a user without administrator privileges can create a symbolic link to a file that requires elevated privileges to write to or modify, which may lead to denial of service, escalation of privilege or limited data tampering.
Official announcement: For details, see the link – https://nvidia.custhelp.com/app/answers/detail/a_id/5384/kw/cve-2022-42292
My observation:
I speculate that this vulnerability will affect home users rather than business users. Since the domain user account has best practice Windows access control policies which driven by IT department.
For your reference:
Symbolic links have irrelevant access permissions. Users are only prevented from operating on a symlink by the permissions of its parent directory and the target file. Windows 11 doesn’t require administrative privileges to create symbolic links.
Apart from above concern. Actually, it’s easy to setup access restrictions for home user. You can do it yourself.
Enable Administrator account on Windows 11 from Command Prompt
1. Open Start on Windows 11.
2. Run “Command Prompt”, right-click the top result, and select the Run as administrator option.
3. Type the following command to enable the Windows 11 Administrator account and press Enter: net user “Administrator” /active:yes.