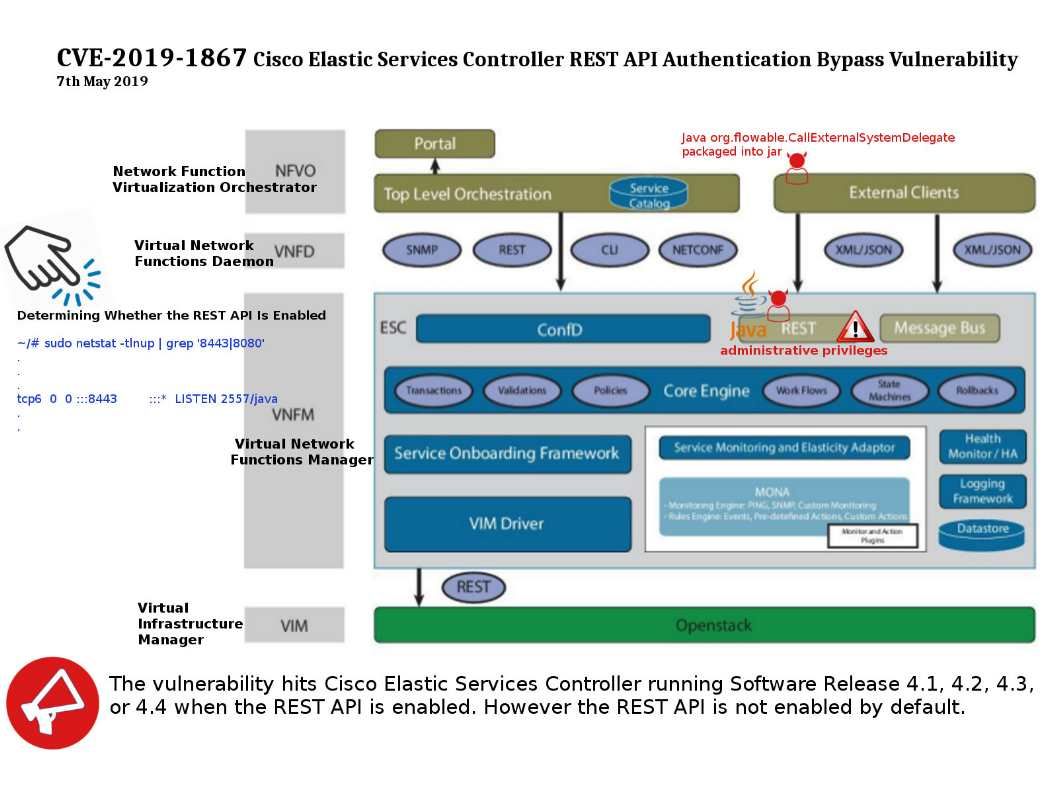
Preface: A vulnerability in the REST API of Cisco Elastic Services Controller (ESC) could allow an unauthenticated, remote attacker to bypass authentication on the REST API.
About Rest API: The attacker could be at the client side, sometimes it compromise of your REST API and, where the victim is the REST API server, so the attacker can creates a rogue, malicious app. This is exact what Cisco is going to address.
Speculation: Hacker can exploit this way, java org.flowable.CallExternalSystemDelegate package to jar .
Affected Products : Software Release 4.1, 4.2, 4.3, or 4.4 when the REST API is enabled.
Remark: The REST API is not enabled by default.
Official announcement: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190507-esc-authbypass
My coder is trying to convince me to move to .net from PHP. I have always disliked the idea because of the expenses. But he’s tryiong none the less. I’ve been using WordPress on numerous websites for about a year and am nervous about switching to another platform. I have heard fantastic things about blogengine.net. Is there a way I can transfer all my wordpress content into it? Any kind of help would be greatly appreciated!|
Howdy! I simply wish to offer you a big thumbs up for the great information you have right here on this post. I’ll be returning to your web site for more soon.|
Ahaa, its fastidious conversation regarding this paragraph here at this web site, I have read all that, so at this time me also commenting here.|
It’s actually a nice and helpful piece of information. I am happy that you simply shared this useful information with us. Please keep us up to date like this. Thank you for sharing.|