Preface: Our daily life is relies on Cloud computing system. Smart City, GPRS, mapping & spatial analytics technology their backend system are located on cloud. Apart of cloud system operation and architecture. The inter network empower its life.
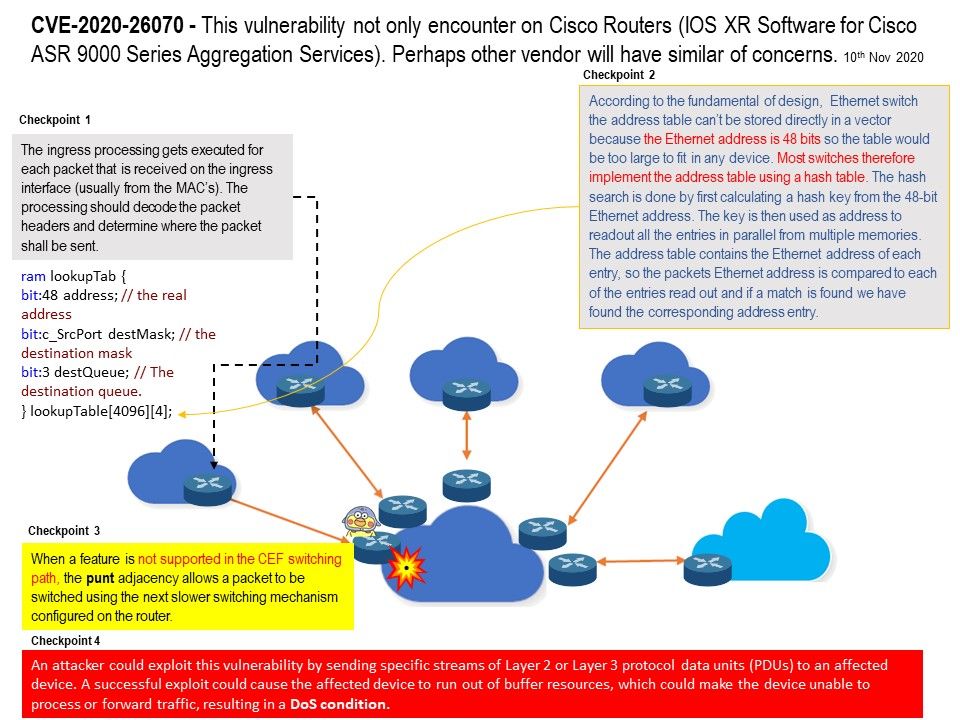
Background: In our digital world , networks packet processing functions are dynamically injected into the network. Each packet may carry the processing code that routers apply to the network when they perform forwarding functions. Furthermore, Ingress packets are temporarily stored in the internal dispatcher packet buffer until processed. When a feature is not supported in the CEF switching path, the punt adjacency allows a packet to be switched using the next slower switching mechanism configured on the router. Once packet processing is complete and the packet has been modified.The packet is copied from the internal packet buffer to the deep output packet buffer, where it awaits scheduling for output.
Technical highlights: The ingress processing gets executed for each packet that is received on the ingress interface (MAC). The processing should decode the packet headers and determine where the packet shall be sent. When a feature is not supported in the CEF switching path, the punt adjacency allows a packet to be switched using the next slower switching mechanism configured on the router.
Current known factors: A vulnerability in the ingress packet processing function of Cisco IOS XR Software for Cisco ASR 9000 Series Aggregation Services Routers could allow an unauthenticated, remote attacker to cause a denial of service (DoS) condition on an affected device. For more details. please refer to url – https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-xr-cp-dos-ej8VB9QY