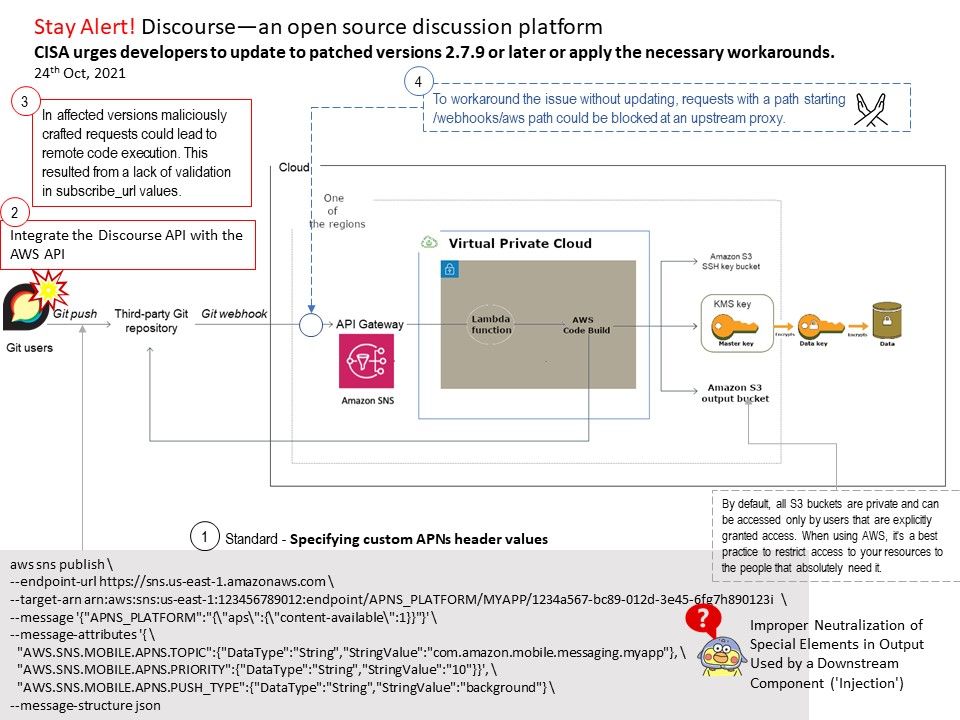
Preface: If you have already integrated the Discourse API with the AWS API, you should be vigilant about this.
Background: Amazon Simple Notification Service (Amazon SNS) is a managed service that provides message delivery from publishers to subscribers (also known as producers and consumers). Publishers communicate asynchronously with subscribers by sending messages to a topic, which is a logical access point and communication channel. Clients can subscribe to the SNS topic and receive published messages using a supported endpoint type, such as Amazon Kinesis Data Firehose, Amazon SQS, AWS Lambda, HTTP, email, mobile push notifications, and mobile text messages (SMS).
Discourse is the open source discussion platform built for Internet usage . Use it as a mailing list, discussion forum, long-form chat room, and more! Discourse supports the latest, stable releases of all major browsers and platforms:Microsoft Edge, Google Chrome, Mozilla Firefox & Apple Safari.
Vulnerability details: In affected versions maliciously crafted requests could lead to remote code execution. This resulted from a lack of validation in subscribe_url values. But what is the exact consequence, it is unknown in the moment. But the risk level of this vulnerability will be based on the adjacent component. For example: AWS Lambda is a serverless compute service that runs your code in response to events and automatically manages the underlying compute resources for you. So if there is design limitation on Lambda. This remote code execution power will be boosted. See whether the information displayed in attached diagram will awaken your thinking of this vulnerability?
Workaround: To workaround the issue without updating, requests with a path starting [/]webhooks[/]aws path could be blocked at an upstream proxy.
Official announcement: Vendor has released a security advisory to address a critical remote code execution (RCE) vulnerability (CVE-2021-41163) in Discourse versions 2.7.8 and earlier. —https://github.com/discourse/discourse/security/advisories/GHSA-jcjx-pvpc-qgwq