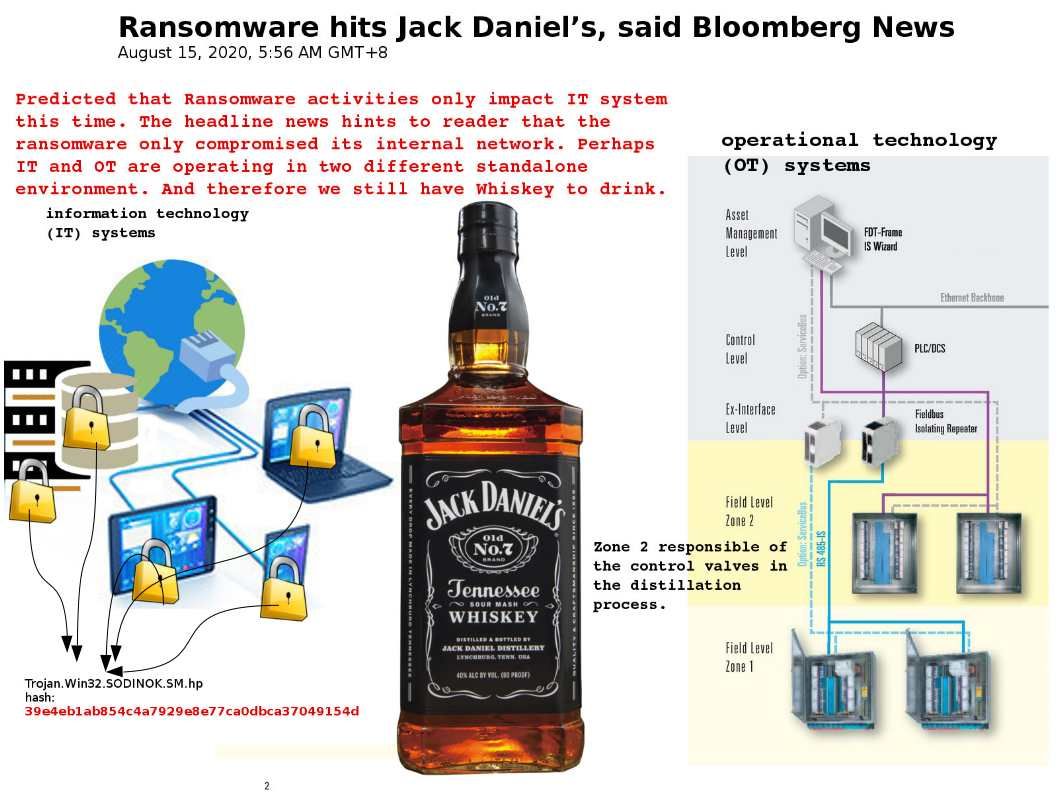
Preface: Whiskey production involves multiple procedures carried out in potentially hazardous atmospheres. LB Remote I/O System connects sensors and actuators to the DCS via PROFIBUS. In terms of application, DCS is suitable for whisky production and complex control processes.
Incident background: Brown-Forman Corp., a manufacturer of alcoholic beverages including Jack Daniel’s and Finlandia, said it was hit by a cyber-attack in which some information, including employee data, may have been impacted. Please refer to the link for more details – https://www.bloomberg.com/news/articles/2020-08-14/brown-forman-was-target-of-apparent-ransomware-attack
Technical details of ransomware: A message sent anonymously to Bloomberg claimed to have hacked Brown-Forman and compromised its internal network. Ransomware aka REvil. The infection mechanism of this ransomware relies Microsoft design weakness (CVE-2018-8453).
As usual, ransomware will copy the data then write data to the registry. The ransomware process will destroy all shadow volumes of the victim machine and disable the protection of the recovery boot. Finally, it encrypts files in all logical units and network shares, and displays the ransom notice on the screen.
Recommendation: In order to avoid ransomware attack. We should follow the patch management by vendor. And maintain update of antivirus program.
.jpg?width=1920&height=1080&fit=bounds)
.jpg?width=1920&height=1080&fit=bounds)