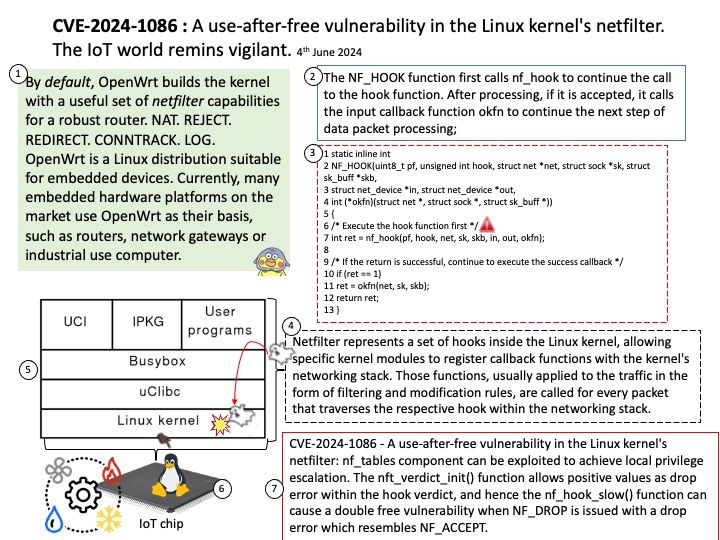
Preface: By default, OpenWrt builds the kernel with a useful set of netfilter capabilities for a robust router. NAT. REJECT. REDIRECT. CONNTRACK. LOG.
OpenWrt is a Linux distribution suitable for embedded devices. Currently, many embedded hardware platforms on the market use OpenWrt as their basis, such as routers, network gateways or industrial use computer
Background: Netfilter is a framework provided by the Linux kernel that allows various networking-related operations to be implemented in the form of customized handlers. Netfilter offers various functions and operations for packet filtering, network address translation, and port translation, which provide the functionality required for directing packets through a network and prohibiting packets from reaching sensitive locations within a network.
Netfilter represents a set of hooks inside the Linux kernel, allowing specific kernel modules to register callback functions with the kernel’s networking stack. Those functions, usually applied to the traffic in the form of filtering and modification rules, are called for every packet that traverses the respective hook within the networking stack.
Vulnerability details: CVE-2024-1086 A use-after-free vulnerability in the Linux kernel’s netfilter: nf_tables component can be exploited to achieve local privilege escalation. The nft_verdict_init() function allows positive values as drop error within the hook verdict, and hence the nf_hook_slow() function can cause a double free vulnerability when NF_DROP is issued with a drop error which resembles NF_ACCEPT. We recommend upgrading past commit f342de4e2f33e0e39165d8639387aa6c19dff660.
Official announcement: For detail, please refer to link – https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-1086