A reverse proxy is not totally transparent to the application on the backend. When the application on the backend returns content including self-referential URLs using its own backend address and port, the client will usually not be able to use these URLs.
Deploy Apache Tomcat Connector (mod_jk) can easy to solve these technical problem. It supports the load balancing of HTTP calls to a set of Servlet containers, while maintaining sticky sessions and communicating over AJP.
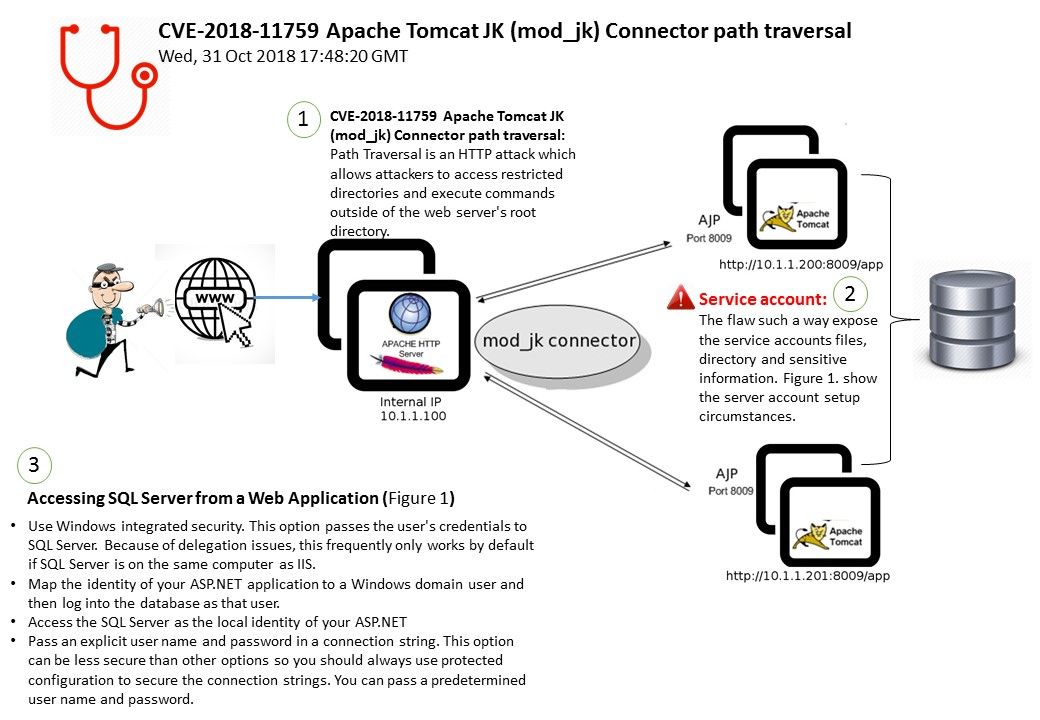
Regarding to vulnerability detail of CVE-2018-11759, it shown that Apache Tomcat JK (mod_jk) Connector design flaw contains path traversal vulnerability.
My speculation is that such vulnerability will be effected SME firm web application server. If the vulnerability occurs, it provides a way let’s attacker trace the target destination especially the location services account file.
For more details, please refer below url for reference.