
Enterprise firm execute data classification to protect corporate important data. Follow the code of practise, confidential data contained high level of sensitivity label requires encryption. The whistleblower Edward Snowden alerts the people in the world on 2013. But you might have question to ask till now, what sort of personal data we need to protect. Seems end user computing mostly ignore by users. The traditional idea is that we enforce the preventive control from server end. As times go by, mobile phone twisted the IT world. IT Renaissance, literally reborn. The usage of computer not limit to location and time zone. We can execute the remittance or payment on mobile phone. You do a backup or synchronize mobile data when go home. Sure you can upload everything on cloud.
In regards of global surveillance program by US government
It looks that surveillance program is a never ending story! Why? From official perspective domestic surveillance program can effectively monitoring terrorist attacks and criminal activities. NSA web page slogan have the following statement.
“Defending our nation. Securing the citizens.”
We have no objection that collection of internet data, mobile phone voice and data exchange as a weapon fright againts crime. To be honest we don’t have rights! But question raised how to identify the usage of this data?We are not the perpetrator, logically we might not afraid of this control?
Highlight the NSA data collection methoglogy:
- Real-Time Yahoo Email Scanning
- Domestic Intercept Stations
- Bulk Collection of U.S. Citizens’ Phone Records
- The PRISM Program: Source of Raw Intelligence
- Google Cloud Exploitation
- Cellphone Tracking
- Spying Toolbox: Servers, routers, firewall devices, computers, USB, keyboard, wireless LAN, cell phone network & mobile phone
- FBI Aviation Surveillance Operations (FBI Hawk Owl Project)
- XKeyscore: Our Real-Time Internet Monitoring Capability
Above details not a confidential data, you can easy find this information. Please take a visit to NSA front page, for more details please see below:
https://nsa.gov1.info/surveillance/
US Government with high visibility statement let’s the citizens know they are under surveillance. A open method of NSA is use a tool so called “XKEYSCORE”. When an US speaker logs into a Yahoo email address, XKEYSCORE will store “mail/yahoo/login” as the associated appID. This stream of traffic will match the “mail/english” fingerprint (denoting language settings). When a browser visits a site that uses Yield Manager, a cookie will be set. This cookie is used to identify whether the browser has loaded an advert and when and where it loaded it (which detects Yahoo browser cookies). Yield Manager also collects information such as:
– the date and time of your visit to the website.
– IP address.
– the type of browser you are using.
– the web page address you are visiting.
XKEYSCORE appIDs and fingerprints lists several revealing examples. Windows Update requests appear to fall under the “update_service/windows” appID, and normal web requests fall under the “http/get” appID. XKEYSCORE can automatically detect Airblue travel itineraries with the “travel/airblue” fingerprint, and iPhone web browser traffic with the “browser/cellphone/iphone” fingerprint.
XKEYSCORE features highlight:
- Tracking Bridge Users
- Tracking Tor Directory Authorities
- Tracking Torproject.org Visits
See below part of the XKEYSCORE sourcecode can bring you an idea XKEYSCORE focus on TOR routers.
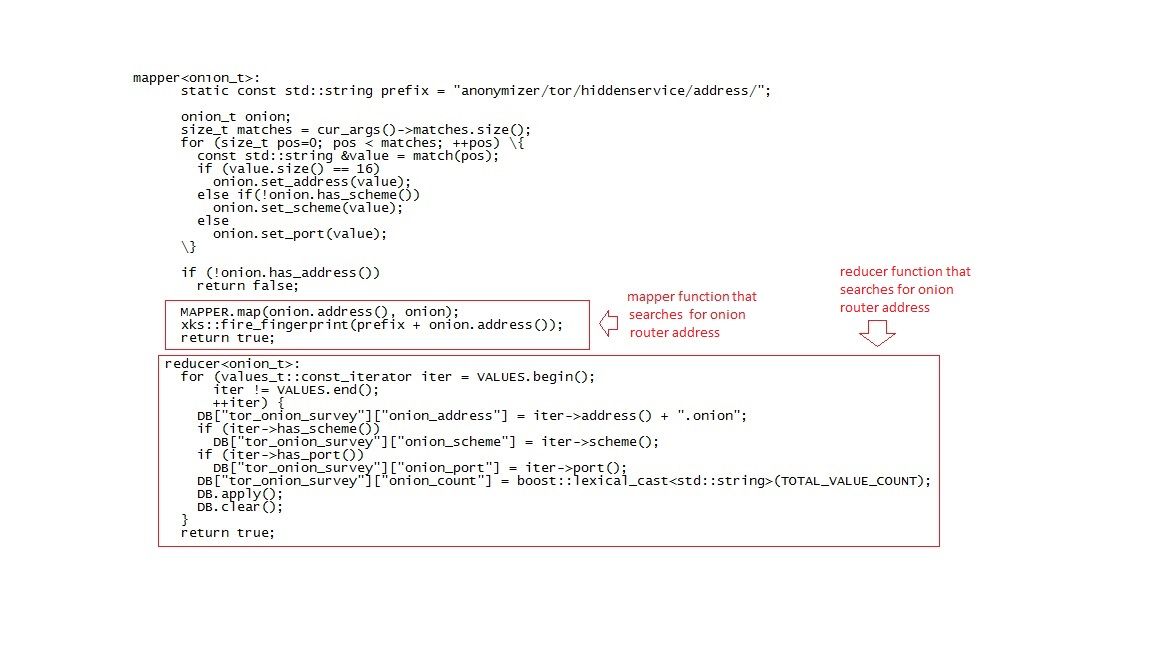
Traffic flows into an XKEYSCORE cluster, the system tests the intercepted data against each of these rules and stores whether the traffic matches the pattern.
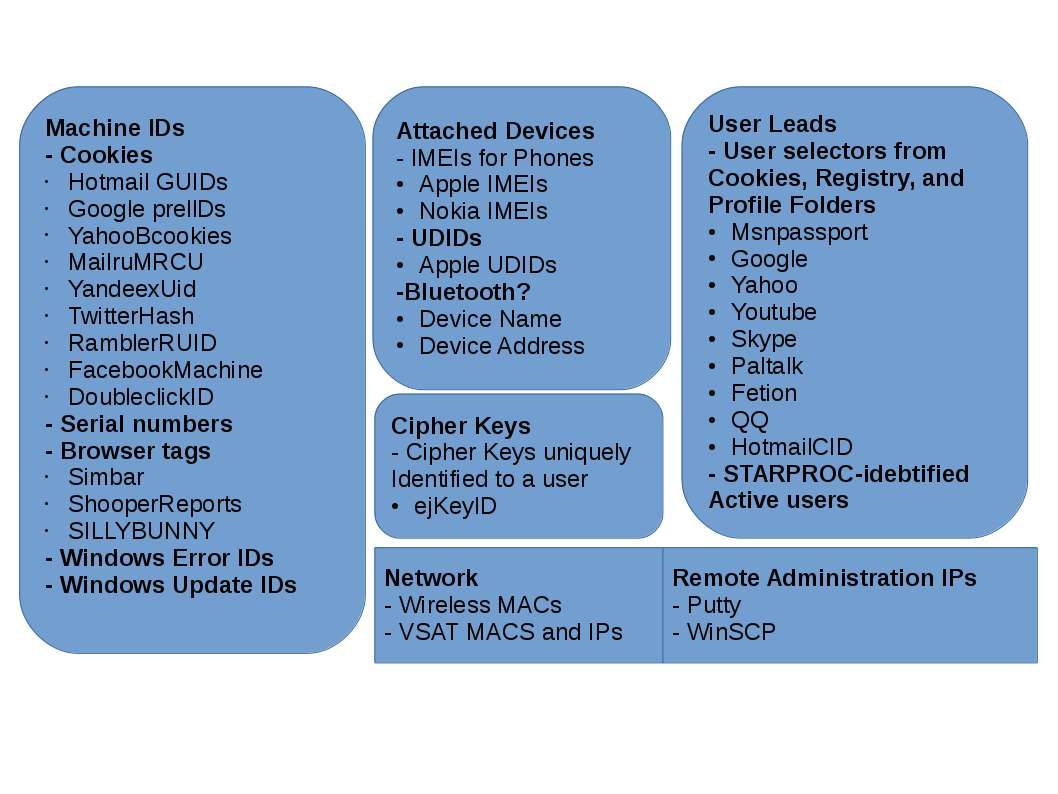
But how about the hackers? Hacker also have interest of these data which NSA does. I believed that below checklist details lure hacker interest.
Internet application coding create a loophole make this cyber games become a never ending story.
Example:
- Email accounts or passwords using session cookies
- A common use for XSS is stealing cookies to hijack sessions and gain access to restrictedweb content
- When cookie doesn’t have Secure flag set, then it can be sent over insecure HTTP (provided that HSTS is not used; HSTS is described in the next section). When this is a case, the attacker controlling the communication channel between a browser and a server can read this cookie. If the cookie stores session ID, then disclosure of this cookie over insecure HTTP leads to user impersonation.
- When a cookie doesn’t have HttpOnly flag set, then JavaScript can read a value of this cookie. That’s why XSS attack leads to user impersonation if there is no HttpOnly flag set for a cookie with session ID. When a cookie has HttpOnly flag set, then attacker can’t read a value of the cookie in case of XSS attack. The problem is that access permissions are not clearly specified in RFC 6265. It turns out, that cookie with HttpOnly flag can be overwritten in Safari 8.
Short term conclusion:
No way because we are living on earth!
Would you be all for exchanging hyperlinks?
I just want to tell you that I am beginner to blogging and site-building and seriously enjoyed you’re website. Almost certainly I’m going to bookmark your blog . You surely have fabulous well written articles. Thanks for sharing with us your web site.
You made some decent points there. I did a search on the subject matter and found most guys will go along with with your site.
Hi my loved one! I wish to say that this post is amazing, nice written and include approximately all vital infos. I would like to look extra posts like this .
Terrific work! This is the kind of information that are supposed to be shared around the internet. Shame on the search engines for now not positioning this post higher! Come on over and visit my site . Thanks =)
Wow, awesome weblog structure! How lengthy have you ever been blogging for? you make running a blog glance easy. The total glance of your website is excellent, let alone the content!
I do accept as true with all of the concepts you have introduced in your post. They’re very convincing and will definitely work. Still, the posts are very short for newbies. Could you please lengthen them a little from next time? Thank you for the post.
Excellent blog here! Also your web site loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my site loaded up as fast as yours lol
I needed to send you this little bit of remark just to give thanks once again for the exceptional things you’ve shared on this site. This is so remarkably open-handed with people like you to deliver without restraint all that a lot of folks could have offered for an e-book in order to make some bucks for themselves, especially considering that you could have done it if you considered necessary. The creative ideas likewise worked as a great way to be sure that many people have a similar fervor the same as my very own to see good deal more related to this matter. I am sure there are many more pleasurable situations in the future for individuals who scan through your website.
Just want to say your article is as astounding. The clarity in your post is simply excellent and i could assume you’re an expert on this subject. Fine with your permission allow me to grab your feed to keep up to date with forthcoming post. Thanks a million and please keep up the enjoyable work.
whoah this weblog is fantastic i love studying your posts. Keep up the good paintings! You understand, many individuals are looking around for this information, you could aid them greatly.
A person essentially assist to make severely articles I’d state. That is the very first time I frequented your website page and thus far? I surprised with the analysis you made to create this particular post amazing. Fantastic process!
I appreciate, result in I discovered exactly what I was taking a look for. You have ended my 4 day long hunt! God Bless you man. Have a nice day. Bye
Hello my friend! I wish to say that this article is awesome, great written and include approximately all vital infos. I would like to peer extra posts like this .
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research about this. We got a grab a book from our local library but I think I learned more clear from this post. I’m very glad to see such fantastic info being shared freely out there.
hello!,I like your writing very much! proportion we communicate extra approximately your post on AOL? I require an expert in this house to solve my problem. May be that’s you! Having a look ahead to look you.
fantastic put up, very informative. I’m wondering why the other experts of this sector don’t understand this. You should proceed your writing. I am sure, you have a great readers’ base already!
I think this is among the most significant information for me. And i’m glad reading your article. But wanna remark on some general things, The website style is wonderful, the articles is really nice : D. Good job, cheers
Someone necessarily assist to make significantly articles I’d state. This is the very first time I frequented your website page and to this point? I amazed with the analysis you made to create this particular post incredible. Fantastic job!
Fantastic beat ! I would like to apprentice while you amend your web site, how could i subscribe for a blog web site? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear concept
You are a very capable individual!
As a Newbie, I am permanently searching online for articles that can benefit me. Thank you
You really make it seem so easy with your presentation but I find this matter to be really something that I think I would never understand. It seems too complex and extremely broad for me. I am looking forward for your next post, I’ll try to get the hang of it!
I’m still learning from you, as I’m trying to reach my goals. I certainly enjoy reading everything that is written on your website.Keep the stories coming. I liked it!
Good write-up, I am normal visitor of one¡¦s web site, maintain up the excellent operate, and It is going to be a regular visitor for a lengthy time.
hello!,I like your writing so so much! proportion we keep in touch more about your article on AOL? I require an expert on this area to resolve my problem. May be that is you! Looking forward to look you.
Excellent web site. Lots of useful information here. I am sending it to a few pals ans additionally sharing in delicious. And obviously, thank you to your sweat!
You actually make it seem so easy with your presentation but I find this topic to be really something which I think I would never understand. It seems too complicated and very broad for me. I am looking forward for your next post, I will try to get the hang of it!
Simply desire to say your article is as amazing. The clearness in your post is just excellent and i can assume you are an expert on this subject. Fine with your permission allow me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the enjoyable work.
I loved as much as you will receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get got an shakiness over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly very often inside case you shield this increase.
Hey, you used to write excellent, but the last several posts have been kinda boring¡K I miss your super writings. Past several posts are just a little out of track! come on!
You completed several good points there. I did a search on the issue and found mainly people will go along with with your blog.
Thank you for the sensible critique. Me & my neighbor were just preparing to do some research about this. We got a grab a book from our local library but I think I learned more clear from this post. I’m very glad to see such excellent information being shared freely out there.
Undeniably believe that which you stated. Your favorite justification seemed to be on the internet the easiest thing to be aware of. I say to you, I certainly get irked while people consider worries that they plainly don’t know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side-effects , people can take a signal. Will probably be back to get more. Thanks
Hello, Neat post. There’s an issue with your web site in internet explorer, could check this¡K IE nonetheless is the marketplace leader and a good component of other folks will omit your magnificent writing due to this problem.
My brother recommended I might like this blog. He was entirely right. This post actually made my day. You can not imagine simply how much time I had spent for this information! Thanks!
Thank you for any other magnificent post. The place else may anybody get that kind of info in such an ideal means of writing? I’ve a presentation next week, and I’m at the look for such info.
I precisely wanted to thank you so much yet again. I do not know what I would have handled in the absence of the entire solutions documented by you concerning this area of interest. It became a fearsome scenario for me personally, however , understanding this well-written style you resolved that made me to weep for fulfillment. I’m thankful for the assistance as well as believe you recognize what a powerful job you’re getting into teaching the others by way of a blog. Probably you haven’t got to know any of us.
We are a group of volunteers and opening a new scheme in our community. Your site offered us with valuable info to work on. You’ve done an impressive job and our whole community will be thankful to you.
Heya i’m for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and aid others like you helped me.
I delight in, cause I discovered just what I used to be looking for. You’ve ended my 4 day lengthy hunt! God Bless you man. Have a nice day. Bye
Definitely, what a magnificent site and revealing posts, I surely will bookmark your website.All the Best!
I’m not sure where you are getting your info, but great topic. I needs to spend some time learning more or understanding more. Thanks for great info I was looking for this information for my mission.
Hello, Neat post. There is an issue together with your website in internet explorer, may check this¡K IE nonetheless is the marketplace leader and a big element of other folks will leave out your magnificent writing due to this problem.
I was just searching for this information for a while. After 6 hours of continuous Googleing, at last I got it in your site. I wonder what’s the lack of Google strategy that don’t rank this type of informative web sites in top of the list. Generally the top sites are full of garbage.
Wow, fantastic blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is magnificent, let alone the content!
Wonderful beat ! I would like to apprentice while you amend your web site, how could i subscribe for a blog site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear idea
I have been surfing online greater than three hours lately, yet I by no means discovered any interesting article like yours. It is lovely price sufficient for me. In my view, if all web owners and bloggers made just right content as you probably did, the internet will probably be much more helpful than ever before.
You actually make it appear so easy together with your presentation however I in finding this matter to be actually one thing that I believe I would by no means understand. It seems too complicated and very vast for me. I’m looking forward to your next publish, I will try to get the hang of it!
Thank you for sharing excellent informations. Your website is very cool. I’m impressed by the details that you have on this web site. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found simply the information I already searched all over the place and simply couldn’t come across. What an ideal site.
I was suggested this blog by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my difficulty. You’re amazing! Thanks!
Great write-up, I am normal visitor of one¡¦s web site, maintain up the excellent operate, and It is going to be a regular visitor for a long time.
Awsome website! I am loving it!! Will be back later to read some more. I am taking your feeds also
As I web-site possessor I believe the content material here is rattling wonderful , appreciate it for your efforts. You should keep it up forever! Best of luck.
I have been absent for some time, but now I remember why I used to love this blog. Thanks , I will try and check back more often. How frequently you update your website?
Excellent blog here! Also your site loads up very fast! What web host are you using? Can I get your affiliate link to your host? I wish my site loaded up as fast as yours lol
It¡¦s really a great and useful piece of info. I¡¦m glad that you simply shared this helpful information with us. Please keep us up to date like this. Thanks for sharing.
whoah this blog is wonderful i love reading your articles. Keep up the good work! You know, many people are hunting round for this information, you could help them greatly.
I like what you guys are up too. Such intelligent work and reporting! Keep up the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my website 🙂
I will immediately grab your rss as I can’t to find your e-mail subscription hyperlink or newsletter service. Do you’ve any? Kindly allow me realize in order that I may subscribe. Thanks.
I am just writing to make you understand what a magnificent discovery my cousin’s daughter found studying your webblog. She mastered a good number of issues, most notably what it is like to possess a very effective teaching heart to get other individuals quite simply fully understand specific complicated subject matter. You truly exceeded my expected results. I appreciate you for providing these warm and friendly, safe, informative and also unique tips about this topic to Sandra.
Hello my loved one! I want to say that this post is amazing, great written and include approximately all significant infos. I¡¦d like to see extra posts like this .
As I website possessor I believe the content material here is rattling wonderful , appreciate it for your efforts. You should keep it up forever! Best of luck.
My husband and i have been absolutely joyous that Louis could deal with his research via the ideas he acquired when using the weblog. It’s not at all simplistic to just be giving away information which often the others could have been trying to sell. And now we remember we have got the website owner to be grateful to because of that. All the explanations you made, the simple site menu, the relationships you can aid to promote – it’s got most awesome, and it’s really assisting our son in addition to the family understand that subject matter is amusing, and that is very vital. Many thanks for the whole lot!
I wanted to jot down a small message so as to thank you for these marvelous techniques you are sharing on this website. My long internet research has at the end of the day been recognized with high-quality ideas to talk about with my friends. I ‘d say that many of us website visitors actually are undoubtedly blessed to dwell in a fine community with very many awesome professionals with great opinions. I feel extremely grateful to have encountered your entire weblog and look forward to plenty of more entertaining times reading here. Thank you once again for all the details.
I have been surfing online greater than three hours as of late, yet I by no means discovered any attention-grabbing article like yours. It¡¦s pretty worth enough for me. Personally, if all webmasters and bloggers made good content material as you probably did, the net might be a lot more helpful than ever before.
Thanks so much for giving everyone such a spectacular possiblity to read articles and blog posts from this blog. It’s usually so pleasurable and packed with fun for me personally and my office acquaintances to search your website particularly 3 times per week to read the latest things you will have. Not to mention, I’m just at all times happy concerning the cool methods you serve. Certain 2 points on this page are really the simplest we have ever had.
naturally like your web-site but you have to take a look at the spelling on several of your posts. Several of them are rife with spelling issues and I in finding it very troublesome to inform the truth however I will definitely come again again.
You made certain good points there. I did a search on the issue and found a good number of people will consent with your blog.
Very nice article and right to the point. I don’t know if this is truly the best place to ask but do you folks have any ideea where to get some professional writers? Thanks in advance 🙂
I and also my buddies appeared to be looking at the great things from the blog then quickly I had an awful suspicion I never thanked the web site owner for them. My women became as a result thrilled to read all of them and have now in actuality been using these things. Appreciation for indeed being simply kind and for making a choice on some superb issues most people are really wanting to discover. My very own sincere apologies for not expressing gratitude to you sooner.
I cling on to listening to the newscast lecture about getting free online grant applications so I have been looking around for the finest site to get one. Could you tell me please, where could i get some?
I do believe all of the ideas you’ve introduced for your post. They’re very convincing and will certainly work. Nonetheless, the posts are very short for novices. May just you please extend them a little from subsequent time? Thank you for the post.
I’m still learning from you, as I’m trying to achieve my goals. I certainly love reading all that is posted on your site.Keep the posts coming. I loved it!
You could certainly see your skills in the work you write. The sector hopes for more passionate writers such as you who aren’t afraid to mention how they believe. Always follow your heart.
This is really interesting, You are a very skilled blogger. I’ve joined your feed and look forward to seeking more of your excellent post. Also, I have shared your site in my social networks!
Of course, what a fantastic site and revealing posts, I surely will bookmark your site.All the Best!
Pretty section of content. I just stumbled upon your website and in accession capital to assert that I get in fact enjoyed account your blog posts. Anyway I will be subscribing to your augment and even I achievement you access consistently quickly.
I was more than happy to discover this website. I wanted to thank you for your time for this particularly fantastic read!! I definitely loved every bit of it and I have you book marked to see new stuff in your blog.
It is the best day to produce some schedules for the extended term. I’ve digested this document and if I would, I wish to suggest to you you handful useful suggestions.
Pretty alluring suggestions you’ll have remarked, say thanks a lot for posting.
Good day here, just turned out to be alert to your wordpress bog through Bing and yahoo, and found that it’s pretty entertaining. I will like if you decide to continue on such.
I merely hope to reveal to you that I am new to putting up a blog and really admired your page. Likely I am most likely to bookmark your blog post . You definitely have amazing article material. Appreciate it for swapping with us your own internet site information
I am not sure where you are getting your information, but good topic. I needs to spend some time learning much more or understanding more. Thanks for fantastic information I was looking for this information for my mission.
Thank you for some other wonderful article. The place else may just anyone get that type of info in such a perfect manner of writing? I have a presentation next week, and I am at the look for such information.
Awsome site! I am loving it!! Will come back again. I am taking your feeds also
Attractive section of content. I just stumbled upon your weblog and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I will be subscribing to your augment and even I achievement you access consistently quickly.
Magnificent goods from you, man. I have understand your stuff previous to and you’re just extremely fantastic. I really like what you’ve acquired here, certainly like what you are saying and the way in which you say it. You make it entertaining and you still care for to keep it sensible. I cant wait to read much more from you. This is actually a terrific website.
I have been exploring for a bit for any high quality articles or blog posts on this sort of house . Exploring in Yahoo I ultimately stumbled upon this site. Reading this info So i¡¦m satisfied to show that I have a very good uncanny feeling I discovered exactly what I needed. I so much for sure will make certain to do not omit this site and provides it a glance regularly.
Very nice info and straight to the point. I don’t know if this is actually the best place to ask but do you guys have any thoughts on where to hire some professional writers? Thanks in advance 🙂
Hello, Neat post. There’s a problem along with your web site in internet explorer, could check this¡K IE still is the market chief and a huge part of other folks will leave out your great writing because of this problem.
Wow! Thank you! I constantly needed to write on my site something like that. Can I implement a fragment of your post to my website?
I simply couldn’t depart your web site before suggesting that I actually loved the standard info an individual supply for your visitors? Is going to be back incessantly in order to inspect new posts
I would like to thnkx for the efforts you have put in writing this site. I’m hoping the same high-grade website post from you in the upcoming as well. Actually your creative writing abilities has encouraged me to get my own site now. Really the blogging is spreading its wings fast. Your write up is a great example of it.
It¡¦s in point of fact a great and helpful piece of info. I¡¦m happy that you just shared this useful information with us. Please keep us informed like this. Thanks for sharing.
I do trust all of the ideas you have presented for your post. They are really convincing and can definitely work. Still, the posts are too quick for novices. May just you please prolong them a bit from next time? Thank you for the post.
Wow! Thank you! I always needed to write on my blog something like that. Can I take a fragment of your post to my website?
I¡¦ll immediately seize your rss as I can’t to find your email subscription hyperlink or e-newsletter service. Do you have any? Please let me recognise so that I could subscribe. Thanks.
It¡¦s in point of fact a great and useful piece of information. I¡¦m satisfied that you simply shared this helpful info with us. Please stay us informed like this. Thanks for sharing.
You actually make it seem so easy with your presentation but I find this matter to be actually something that I think I would never understand. It seems too complicated and very broad for me. I am looking forward for your next post, I’ll try to get the hang of it!
I’ve been surfing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. Personally, if all site owners and bloggers made good content as you did, the internet will be a lot more useful than ever before.
You have observed very interesting points! ps decent internet site.
Definitely believe that which you stated. Your favorite justification appeared to be on the web the simplest thing to be aware of. I say to you, I definitely get annoyed while people consider worries that they plainly don’t know about. You managed to hit the nail upon the top and also defined out the whole thing without having side-effects , people could take a signal. Will likely be back to get more. Thanks
It’s amazing for me to have a web site, which is valuable in favor of my knowledge. thanks admin|
Only wanna admit that this is very useful , Thanks for taking your time to write this.
There is evidently a bundle to know about this. I suppose you made various good points in features also.
You could definitely see your enthusiasm within the work you write. The world hopes for more passionate writers like you who are not afraid to say how they believe. Always follow your heart. “He never is alone that is accompanied with noble thoughts.” by Fletcher.
I savour, cause I discovered just what I was taking a look for. You have ended my 4 day long hunt! God Bless you man. Have a nice day. Bye
Thank you for helping out, great information. “The four stages of man are infancy, childhood, adolescence, and obsolescence.” by Bruce Barton.
Very interesting subject, thanks for posting.
Hello there, You’ve done an incredible job. I’ll certainly digg it and personally recommend to my friends. I’m confident they will be benefited from this web site.
I believe you have mentioned some very interesting points , regards for the post.
Hi, Neat post. There’s a problem with your website in internet explorer, could test this¡K IE nonetheless is the marketplace leader and a good section of other folks will omit your wonderful writing because of this problem.
I am now not positive the place you’re getting your info, but good topic. I needs to spend a while learning more or figuring out more. Thanks for magnificent info I used to be looking for this info for my mission.
There is perceptibly a lot to realize about this. I believe you made various good points in features also.
I get pleasure from, cause I discovered just what I was taking a look for. You’ve ended my four day lengthy hunt! God Bless you man. Have a great day. Bye
of course like your web-site but you need to test the spelling on quite a few of your posts. Several of them are rife with spelling problems and I find it very bothersome to tell the reality then again I¡¦ll definitely come again again.
Very good written story. It will be useful to anybody who usess it, including me. Keep up the good work – can’r wait to read more posts.
I simply had to appreciate you yet again. I am not sure the things I could possibly have done in the absence of the recommendations discussed by you about this subject matter. Completely was a fearsome dilemma in my view, nevertheless being able to view the expert avenue you resolved the issue forced me to jump over joy. I will be happy for this guidance and in addition hope you find out what a powerful job that you are accomplishing educating people with the aid of your web blog. I am certain you’ve never encountered any of us.
I am continually browsing online for tips that can assist me. Thank you!
Great amazing things here. I am very glad to peer your post. Thank you a lot and i am looking forward to touch you. Will you please drop me a e-mail?
hello there and thank you for your info – I’ve definitely picked up something new from right here. I did however expertise a few technical issues using this web site, since I experienced to reload the web site lots of times previous to I could get it to load properly. I had been wondering if your hosting is OK? Not that I am complaining, but sluggish loading instances times will very frequently affect your placement in google and can damage your high-quality score if ads and marketing with Adwords. Anyway I am adding this RSS to my email and can look out for a lot more of your respective interesting content. Ensure that you update this again very soon..
whoah this weblog is magnificent i like reading your posts. Stay up the good work! You recognize, lots of persons are hunting around for this info, you could help them greatly.
I have not checked in here for some time because I thought it was getting boring, but the last several posts are good quality so I guess I¡¦ll add you back to my daily bloglist. You deserve it my friend 🙂
I wanted to draft you a tiny note to help say thank you as before on your awesome tricks you have featured on this page. This has been quite incredibly generous with people like you to offer freely what many of us might have offered as an ebook to generate some cash on their own, and in particular since you could possibly have done it if you desired. The solutions also worked to be the great way to comprehend the rest have similar eagerness like my very own to understand whole lot more in regard to this matter. Certainly there are numerous more pleasurable opportunities up front for individuals that browse through your blog.
Excellent blog here! Also your website loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as fast as yours lol
Super-Duper site! I am loving it!! Will be back later to read some more. I am bookmarking your feeds also
hello!,I really like your writing so a lot! percentage we communicate extra approximately your article on AOL? I require an expert in this area to unravel my problem. May be that’s you! Taking a look ahead to look you.
I enjoy you because of all of the hard work on this web site. Gloria really loves conducting investigation and it’s really simple to grasp why. All of us know all relating to the dynamic form you create both useful and interesting tactics on your website and therefore increase contribution from website visitors on the topic while our favorite child is in fact starting to learn a whole lot. Enjoy the remaining portion of the new year. You are always doing a really good job.
I’ve been absent for some time, but now I remember why I used to love this blog. Thanks , I will try and check back more often. How frequently you update your web site?
Thanks for sharing excellent informations. Your web site is so cool. I’m impressed by the details that you have on this website. It reveals how nicely you understand this subject. Bookmarked this website page, will come back for extra articles. You, my pal, ROCK! I found just the info I already searched all over the place and just could not come across. What a perfect web site.
I want to point out my affection for your kind-heartedness in support of women who really want help on the subject matter. Your personal commitment to passing the message all over has been extraordinarily significant and have truly encouraged employees just like me to achieve their targets. Your personal important publication can mean a great deal a person like me and somewhat more to my mates. Thanks a ton; from everyone of us.
I think other web site proprietors should take this web site as an model, very clean and fantastic user genial style and design, as well as the content. You’re an expert in this topic!
Fantastic beat ! I wish to apprentice while you amend your website, how could i subscribe for a blog web site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear idea
Bonjour ! Il n’y a pas de flux RSS ici ?
I’ll right away clutch your rss feed as I can’t in finding your email subscription hyperlink or e-newsletter service. Do you’ve any? Please allow me recognize in order that I could subscribe. Thanks.
Bonjour ! Bonne lecture ! Je le met dans mes favoris !
Hi there, You have done an incredible job. I’ll certainly digg it and personally recommend to my friends. I am sure they’ll be benefited from this website.
I just could not go away your site prior to suggesting that I actually loved the standard information a person supply on your guests? Is gonna be back ceaselessly in order to check up on new posts
Hello there, just became alert to your blog through Google, and found that it’s truly informative. I’m gonna watch out for brussels. I will be grateful if you continue this in future. Many people will be benefited from your writing. Cheers!
I’m still learning from you, while I’m improving myself. I certainly enjoy reading all that is posted on your website.Keep the stories coming. I liked it!
I have been browsing on-line greater than 3 hours nowadays, yet I by no means found any interesting article like yours. It¡¦s lovely worth enough for me. Personally, if all site owners and bloggers made good content material as you probably did, the web will likely be a lot more helpful than ever before.
Simply wish to say your article is as astounding. The clearness in your post is just great and i can assume you are an expert on this subject. Well with your permission let me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the rewarding work.
I was examining some of your articles on this website and I think this website is rattling instructive! Keep posting.
There is noticeably a bundle to know about this. I assume you made certain nice points in features also.
As soon as I detected this web site I went on reddit to share some of the love with them.
I¡¦ll immediately take hold of your rss as I can not to find your e-mail subscription link or newsletter service. Do you’ve any? Please permit me recognize in order that I may subscribe. Thanks.
It’s in point of fact a nice and useful piece of information. I am glad that you shared this useful information with us. Please keep us up to date like this. Thanks for sharing.
I’ll right away clutch your rss feed as I can not find your e-mail subscription link or newsletter service. Do you have any? Kindly permit me recognise so that I may just subscribe. Thanks.
You are a very intelligent person!
Excellent read, I just passed this onto a friend who was doing a little research on that. And he just bought me lunch since I found it for him smile Thus let me rephrase that: Thank you for lunch! “Too much sanity may be madness. And maddest of all, to see life as it is and not as it should be” by Miguel de Cervantes.
Great write-up, I am regular visitor of one¡¦s website, maintain up the excellent operate, and It’s going to be a regular visitor for a lengthy time.
I don’t even know how I ended up here, but I thought this post was good. I do not know who you are but definitely you are going to a famous blogger if you are not already 😉 Cheers!
I¡¦m not positive the place you are getting your info, however great topic. I must spend some time learning much more or working out more. Thank you for fantastic information I was looking for this info for my mission.
As a Newbie, I am always exploring online for articles that can be of assistance to me. Thank you
Excellent post. I was checking continuously this blog and I am impressed! Extremely useful information particularly the last part 🙂 I care for such info a lot. I was looking for this certain information for a very long time. Thank you and good luck.
Hi, i think that i saw you visited my web site thus i came to “return the favor”.I’m trying to find things to improve my website!I suppose its ok to use some of your ideas!!
It is usually right opportunity to put together some goals for the long run. I’ve read through this piece of writing and if I may just, I want to suggest to you you couple of entertaining tip.
I really need to reveal to you that I am new to writing a blog and totally cherished your information. More than likely I am inclined to remember your blog post . You simply have wonderful article content. Delight In it for discussing with us your favorite domain post
I just hope to tell you that I am new to having a blog and undeniably adored your site. Quite possibly I am probably to store your blog post . You really have impressive article information. Love it for discussing with us all of your blog information
Wow, superb blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your website is excellent, as well as the content!
I am not certain the place you’re getting your information, but good topic. I needs to spend some time learning more or working out more. Thank you for wonderful information I used to be on the lookout for this information for my mission.
I’m pretty pleased to discover this site. I want to to thank you for ones time for this particularly fantastic read!! I definitely really liked every part of it and i also have you bookmarked to check out new information in your site.
Truly motivating suggestions you’ll have said, say thanks a lot for writing.
It’s actually practically close to impossible to find well-qualified men or women on this niche, still, you appear like you realize what exactly you’re talking about! Thank You
This is really interesting, You are a very skilled blogger. I’ve joined your feed and look forward to seeking more of your magnificent post. Also, I’ve shared your website in my social networks!
Useful information. Lucky me I found your web site by accident, and I am surprised why this twist of fate did not happened earlier! I bookmarked it.
Very efficiently written post. It will be valuable to anyone who usess it, as well as myself. Keep doing what you are doing – i will definitely read more posts.
It is actually a great and helpful piece of info. I am satisfied that you simply shared this useful info with us. Please keep us informed like this. Thanks for sharing.
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get bought an nervousness over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly very often inside case you shield this increase.
You really make it seem really easy along with your presentation but I find this matter to be actually something that I feel I’d by no means understand. It sort of feels too complex and extremely huge for me. I am having a look forward in your subsequent publish, I¡¦ll try to get the dangle of it!
I was just looking for this info for some time. After six hours of continuous Googleing, finally I got it in your website. I wonder what’s the lack of Google strategy that do not rank this type of informative sites in top of the list. Normally the top web sites are full of garbage.
Hey, you used to write fantastic, but the last several posts have been kinda boring¡K I miss your tremendous writings. Past few posts are just a little bit out of track! come on!
Is it possible to make a spoiler button in blogger blog posts ? I don’t know javascript and know very basic html only. I’ve tried copying snippets of javascript into my posts to try but most of them doesn’t work. Some only works in the create post window but after publishing it doesn’t work anymore. Most buttons just does nothing after being clicked. Any solutions ?.
Bonjour ! merci
It is perfect time to make some plans for the future and it is time to be happy. I’ve read this post and if I could I desire to suggest you some interesting things or advice. Perhaps you could write next articles referring to this article. I want to read more things about it!
I merely desire to notify you that I am new to posting and completely liked your website. Likely I am most likely to bookmark your blog post . You truly have extraordinary article material. Appreciate it for telling with us your main website write-up
I was very pleased to find this page. I want to to thank you for ones time for this particularly wonderful read!! I definitely really liked every bit of it and i also have you saved to fav to check out new things on your website.
It is usually ideal opportunity to get some intentions for the future. I’ve go through this post and if I may, I want to encourage you number of fascinating tip.
I really wish to show you that I am new to posting and pretty much liked your page. Likely I am probably to remember your blog post . You certainly have amazing article information. Be Grateful For it for giving out with us your current blog document
Noticeably motivating points you have mentioned, warm regards for writing.
I was excited to find this site. I need to to thank you for ones time due to this wonderful read!! I definitely appreciated every little bit of it and I have you saved as a favorite to see new stuff in your site.
It really is convenient day to create some desires for the future. I have browsed this blog posting and if I have the ability to, I want to propose you couple fascinating recommendations.
Might be near unthinkable to come across well-qualified americans on this theme, still, you look like you understand whatever you’re writing on! Excellent
I merely want to advise you that I am new to posting and totally enjoyed your page. Very likely I am most likely to bookmark your blog post . You seriously have stunning article material. Love it for giving out with us your own blog page
It truly is almost extremely difficult to find well-qualified men and women on this content, regrettably you come across as like you know which you’re writing on! Thanks A Lot
Seriously compelling suggestions you have said, warm regards for writing.
I was pretty pleased to uncover this website. I want to to thank you for ones time due to this wonderful read!! I definitely savored every bit of it and I have you bookmarked to see new stuff on your website.
I simply have to tell you that I am new to online blogging and completely enjoyed your website. More than likely I am most likely to save your blog post . You really have magnificent article blog posts. Delight In it for giving out with us your very own website post
Wow, fantastic blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your web site is great, as well as the content!
Great remarkable things here. I am very happy to peer your article. Thank you a lot and i’m looking ahead to contact you. Will you please drop me a mail?
It is perfect time to make some plans for the future and it is time to be happy. I have read this post and if I could I wish to suggest you few interesting things or advice. Maybe you could write next articles referring to this article. I wish to read more things about it!
Good site! I truly love how it is easy on my eyes and the data are well written. I am wondering how I might be notified when a new post has been made. I have subscribed to your feed which must do the trick! Have a nice day!
My husband and i felt quite excited Edward could deal with his inquiry with the ideas he discovered out of the web pages. It is now and again perplexing to just possibly be giving out concepts which other folks could have been making money from. And we all do understand we have got the website owner to be grateful to for this. The entire explanations you made, the straightforward blog navigation, the friendships you help foster – it’s most astounding, and it’s aiding our son and our family believe that the topic is pleasurable, which is certainly especially essential. Many thanks for everything!
You are a very capable individual!
Nice read, I just passed this onto a friend who was doing a little research on that. And he actually bought me lunch because I found it for him smile Therefore let me rephrase that: Thank you for lunch!
A person necessarily help to make seriously articles I might state. This is the very first time I frequented your web page and to this point? I surprised with the research you made to make this actual post extraordinary. Magnificent task!
Great work! That is the kind of information that are supposed to be shared around the net. Disgrace on Google for no longer positioning this put up upper! Come on over and seek advice from my website . Thanks =)
Hello. Great job. I did not expect this. This is a fantastic story. Thanks!
I must show some thanks to this writer for bailing me out of such a predicament. Because of browsing through the search engines and finding advice which were not productive, I was thinking my entire life was over. Existing minus the answers to the issues you have fixed by way of your main short article is a crucial case, and the ones which might have badly damaged my entire career if I hadn’t noticed your site. Your personal understanding and kindness in maneuvering a lot of stuff was crucial. I’m not sure what I would have done if I had not come upon such a step like this. I can also at this moment look forward to my future. Thanks a lot so much for this professional and sensible help. I will not hesitate to refer your web sites to anyone who wants and needs assistance on this area.
Our community leaders need to read this, and look at developing some of your recommendations.
I was extremely pleased to uncover this great site. I wanted to thank you for ones time just for this wonderful read!! I definitely really liked every bit of it and i also have you saved to fav to see new stuff in your website.
I think other web-site proprietors should take this site as an model, very clean and great user genial style and design, as well as the content. You are an expert in this topic!
I simply wish to inform you you that I am new to online blogging and pretty much enjoyed your write-up. Very possible I am probably to save your blog post . You indeed have excellent article materials. Get Pleasure From it for giving out with us your internet site write-up
I simply hope to notify you that I am new to blogging and extremely cherished your post. Quite possibly I am inclined to remember your blog post . You literally have wonderful article information. Be Grateful For it for swapping with us your current website article
I think this is one of the most vital info for me. And i’m glad reading your article. But should remark on some general things, The site style is great, the articles is really great : D. Good job, cheers
Good website! I truly love how it is easy on my eyes and the data are well written. I am wondering how I might be notified whenever a new post has been made. I have subscribed to your RSS which must do the trick! Have a nice day!
hello there and thank you for your information – I have definitely picked up anything new from right here. I did however expertise some technical points using this web site, since I experienced to reload the site a lot of times previous to I could get it to load properly. I had been wondering if your web hosting is OK? Not that I’m complaining, but sluggish loading instances times will sometimes affect your placement in google and could damage your high-quality score if ads and marketing with Adwords. Anyway I’m adding this RSS to my email and can look out for a lot more of your respective intriguing content. Make sure you update this again very soon..
I have recently started a blog, the information you provide on this website has helped me tremendously. Thanks for all of your time & work. “Yield not to evils, but attack all the more boldly.” by Virgil.
You are a very capable individual!
Great awesome issues here. I am very glad to peer your article. Thanks so much and i’m looking ahead to contact you. Will you kindly drop me a e-mail?
I think this is one of the most vital info for me. And i am glad reading your article. But want to remark on few general things, The website style is perfect, the articles is really great : D. Good job, cheers
Very nice article and right to the point. I don’t know if this is really the best place to ask but do you people have any thoughts on where to hire some professional writers? Thx 🙂
you’re actually a excellent webmaster. The website loading speed is amazing. It seems that you’re doing any unique trick. Furthermore, The contents are masterpiece. you have done a great job on this subject!
I am really impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you modify it yourself? Anyway keep up the excellent quality writing, it’s rare to see a nice blog like this one nowadays..
Pretty section of content. I just stumbled upon your site and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently fast.
I carry on listening to the news broadcast talk about getting free online grant applications so I have been looking around for the top site to get one. Could you tell me please, where could i find some?
I wish to express my admiration for your kind-heartedness for people who must have help with this one area of interest. Your special commitment to getting the message all-around had been remarkably practical and have in every case empowered folks like me to reach their dreams. Your new interesting tips and hints indicates so much a person like me and still more to my office workers. Thanks a ton; from all of us.
I like what you guys are up also. Such intelligent work and reporting! Carry on the superb works guys I¡¦ve incorporated you guys to my blogroll. I think it will improve the value of my web site 🙂
I am also writing to let you be aware of what a excellent discovery my cousin’s girl undergone studying the blog. She came to understand a lot of details, with the inclusion of what it is like to possess an excellent helping spirit to let other folks with ease know specified advanced topics. You actually exceeded my expectations. Thank you for delivering the essential, trustworthy, informative and even easy thoughts on your topic to Jane.
Great blog here! Also your web site loads up fast! What host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
My spouse and i got really fortunate that Albert could conclude his inquiry through your precious recommendations he came across through your web site. It is now and again perplexing to simply possibly be giving freely points that many many others could have been selling. We really consider we have got you to give thanks to because of that. These illustrations you have made, the easy website menu, the relationships you will give support to instill – it’s many great, and it is aiding our son and us imagine that this content is fun, and that is exceptionally pressing. Many thanks for the whole lot!
Whats Taking place i am new to this, I stumbled upon this I have discovered It absolutely helpful and it has helped me out loads. I’m hoping to give a contribution & aid other customers like its aided me. Great job.
It is actually a nice and helpful piece of info. I¡¦m happy that you just shared this useful info with us. Please stay us up to date like this. Thanks for sharing.
I haven¡¦t checked in here for a while because I thought it was getting boring, but the last several posts are great quality so I guess I will add you back to my daily bloglist. You deserve it my friend 🙂
I would like to thnkx for the efforts you’ve put in writing this web site. I’m hoping the same high-grade web site post from you in the upcoming as well. Actually your creative writing abilities has inspired me to get my own website now. Really the blogging is spreading its wings rapidly. Your write up is a good example of it.
Thank you for sharing excellent informations. Your website is very cool. I am impressed by the details that you¡¦ve on this blog. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found simply the info I already searched all over the place and just couldn’t come across. What a perfect site.
Thank you for another excellent post. The place else may just anyone get that type of information in such an ideal way of writing? I have a presentation subsequent week, and I’m at the look for such information.
There is apparently a bunch to identify about this. I believe you made certain nice points in features also.
I’m not sure where you’re getting your info, but good topic. I needs to spend some time learning much more or understanding more. Thanks for wonderful information I was looking for this information for my mission.
My wife and i ended up being really satisfied that Louis could round up his studies because of the precious recommendations he acquired out of the web page. It’s not at all simplistic to simply always be giving for free hints which usually many people have been selling. We discover we’ve got the blog owner to give thanks to because of that. The main explanations you’ve made, the easy blog menu, the friendships your site help to instill – it is mostly impressive, and it’s helping our son and us consider that this subject matter is interesting, which is certainly exceptionally vital. Thanks for all!
Thanks for the sensible critique. Me and my neighbor were just preparing to do some research about this. We got a grab a book from our local library but I think I learned more clear from this post. I am very glad to see such magnificent info being shared freely out there.
I actually wanted to construct a brief note so as to appreciate you for the precious ways you are sharing on this site. My extensive internet research has at the end been recognized with high-quality insight to talk about with my colleagues. I ‘d say that most of us website visitors are unquestionably fortunate to be in a fine site with so many lovely people with useful opinions. I feel extremely fortunate to have discovered your website and look forward to plenty of more fun minutes reading here. Thanks a lot once more for everything.
Some genuinely superb content on this internet site, thanks for contribution. “We are always in search of the redeeming formula, the crystallizing thought.” by Etty Hillesum.
I was examining some of your articles on this site and I believe this web site is rattling instructive! Keep putting up.
My spouse and i felt very happy that Ervin managed to deal with his investigation while using the ideas he discovered through your web page. It is now and again perplexing to simply possibly be handing out helpful hints that many people have been trying to sell. So we remember we need the blog owner to thank for that. Those illustrations you have made, the easy site menu, the relationships you can help to create – it’s got most superb, and it is assisting our son in addition to the family recognize that this issue is brilliant, which is certainly very vital. Thanks for all!
hello!,I like your writing very a lot! percentage we keep up a correspondence more about your article on AOL? I require an expert in this space to resolve my problem. Maybe that is you! Looking ahead to see you.
I’ve been absent for a while, but now I remember why I used to love this site. Thanks, I’ll try and check back more frequently. How frequently you update your website?
I do not even know how I ended up here, but I thought this post was great. I don’t know who you are but certainly you’re going to a famous blogger if you aren’t already 😉 Cheers!
I have been browsing online greater than three hours nowadays, yet I by no means found any fascinating article like yours. It¡¦s lovely price sufficient for me. In my opinion, if all web owners and bloggers made just right content material as you probably did, the web can be a lot more helpful than ever before.
I dugg some of you post as I cogitated they were handy very helpful
I have been exploring for a bit for any high quality articles or blog posts in this sort of house . Exploring in Yahoo I finally stumbled upon this web site. Reading this information So i am glad to exhibit that I’ve a very excellent uncanny feeling I came upon exactly what I needed. I such a lot undoubtedly will make certain to do not disregard this site and give it a look on a relentless basis.
I gotta favorite this web site it seems very useful extremely helpful
Undeniably believe that which you said. Your favorite justification appeared to be on the internet the easiest thing to be aware of. I say to you, I certainly get annoyed while people think about worries that they just do not know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side-effects , people can take a signal. Will likely be back to get more. Thanks
Thank you for all of your effort on this web site. My daughter delights in making time for research and it’s obvious why. Many of us know all of the lively mode you convey very helpful tips through your blog and in addition increase participation from some other people on that article then our simple princess is now discovering so much. Have fun with the rest of the year. You’re the one doing a powerful job.
I really like your writing style, superb info , thanks for posting : D.
As soon as I detected this website I went on reddit to share some of the love with them.
You actually make it seem so easy along with your presentation but I in finding this matter to be actually something which I feel I’d by no means understand. It sort of feels too complex and very extensive for me. I am taking a look forward to your next publish, I will attempt to get the hang of it!
hello!,I like your writing so much! share we keep up a correspondence more approximately your post on AOL? I need an expert in this space to resolve my problem. Maybe that is you! Looking ahead to see you.
Hello There. I found your blog using msn. This is an extremely well written article. I will make sure to bookmark it and return to read more of your useful info. Thanks for the post. I will definitely comeback.
I do accept as true with all of the concepts you’ve introduced for your post. They’re very convincing and will certainly work. Nonetheless, the posts are very quick for novices. Could you please lengthen them a bit from subsequent time? Thanks for the post.
I’ve been absent for a while, but now I remember why I used to love this web site. Thanks , I¡¦ll try and check back more frequently. How frequently you update your web site?
magnificent points altogether, you just received a brand new reader. What could you suggest in regards to your post that you just made some days ago? Any sure?
Merely wanna comment that you have a very decent site, I like the style and design it really stands out.
It¡¦s actually a great and useful piece of info. I am satisfied that you just shared this helpful information with us. Please keep us informed like this. Thanks for sharing.
I simply couldn’t depart your web site before suggesting that I extremely loved the usual info a person supply for your visitors? Is going to be again continuously in order to check up on new posts.
I like the helpful information you provide in your articles. I will bookmark your blog and check again here frequently. I’m quite sure I will learn a lot of new stuff right here! Best of luck for the next!
Enjoyed reading this, very good stuff, thanks . “Hereafter, in a better world than this, I shall desire more love and knowledge of you.” by William Shakespeare.
I have recently started a web site, the information you offer on this web site has helped me tremendously. Thanks for all of your time & work. “Men must be taught as if you taught them not, And things unknown proposed as things forgot.” by Alexander Pope.
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how can we communicate?
I have not checked in here for a while because I thought it was getting boring, but the last several posts are great quality so I guess I’ll add you back to my daily bloglist. You deserve it my friend 🙂
Well I sincerely enjoyed reading it. This information offered by you is very useful for good planning.
I¡¦ll immediately grasp your rss feed as I can not in finding your e-mail subscription link or e-newsletter service. Do you’ve any? Please allow me realize in order that I may just subscribe. Thanks.
Nice read, I just passed this onto a friend who was doing some research on that. And he just bought me lunch since I found it for him smile Thus let me rephrase that: Thank you for lunch!
I’m extremely impressed with your writing skills as well as with the layout on your blog. Is this a paid theme or did you modify it yourself? Anyway keep up the nice quality writing, it’s rare to see a nice blog like this one nowadays..
Hello there, just became alert to your blog through Google, and found that it is truly informative. I am gonna watch out for brussels. I will be grateful if you continue this in future. Numerous people will be benefited from your writing. Cheers!
It¡¦s really a cool and helpful piece of info. I¡¦m glad that you shared this helpful info with us. Please stay us up to date like this. Thank you for sharing.
Wow! This could be one particular of the most helpful blogs We have ever arrive across on this subject. Basically Fantastic. I am also a specialist in this topic therefore I can understand your effort.
Hiya, I am really glad I have found this info. Today bloggers publish only about gossips and web and this is really annoying. A good website with interesting content, this is what I need. Thanks for keeping this site, I’ll be visiting it. Do you do newsletters? Can not find it.
I have recently started a web site, the information you offer on this web site has helped me tremendously. Thanks for all of your time & work. “It is a great thing to know our vices.” by Cicero.
I have been browsing on-line more than 3 hours as of late, but I by no means found any interesting article like yours. It¡¦s pretty value enough for me. Personally, if all site owners and bloggers made excellent content material as you did, the web shall be a lot more useful than ever before.
Excellent blog here! Also your site loads up fast! What web host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
Hello, i think that i saw you visited my website so i came to “return the favor”.I’m trying to find things to improve my web site!I suppose its ok to use a few of your ideas!!
you are in point of fact a excellent webmaster. The web site loading pace is amazing. It kind of feels that you are doing any distinctive trick. Furthermore, The contents are masterwork. you have done a excellent job in this matter!
I conceive you have mentioned some very interesting details , thankyou for the post.
You have brought up a very wonderful points , regards for the post.
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you can do with a few pics to drive the message home a little bit, but other than that, this is wonderful blog. An excellent read. I will definitely be back.
Definitely believe that which you said. Your favorite justification appeared to be on the web the easiest thing to be aware of. I say to you, I definitely get annoyed while people consider worries that they just don’t know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side-effects , people could take a signal. Will likely be back to get more. Thanks
I simply could not leave your web site before suggesting that I extremely enjoyed the usual info a person supply to your visitors? Is gonna be again incessantly in order to check out new posts
Good ¡V I should certainly pronounce, impressed with your website. I had no trouble navigating through all tabs as well as related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or something, website theme . a tones way for your client to communicate. Excellent task..
A person essentially assist to make seriously posts I might state. This is the first time I frequented your website page and up to now? I amazed with the analysis you made to make this actual post extraordinary. Great job!
Great awesome issues here. I¡¦m very glad to peer your post. Thank you so much and i’m having a look ahead to touch you. Will you please drop me a mail?
Wow, wonderful blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is great, as well as the content!
I was suggested this website by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my problem. You are incredible! Thanks!
Fantastic goods from you, man. I have understand your stuff previous to and you are just extremely fantastic. I actually like what you have acquired here, really like what you are saying and the way in which you say it. You make it enjoyable and you still care for to keep it sensible. I can’t wait to read much more from you. This is really a tremendous site.
It is appropriate time to make some plans for the future and it’s time to be happy. I have read this post and if I could I wish to suggest you few interesting things or advice. Maybe you could write next articles referring to this article. I want to read more things about it!
Magnificent goods from you, man. I’ve understand your stuff previous to and you are just too great. I actually like what you have acquired here, really like what you are stating and the way in which you say it. You make it enjoyable and you still care for to keep it sensible. I can not wait to read much more from you. This is actually a wonderful web site.
I want to express my thanks to you just for bailing me out of such a challenge. As a result of researching through the the web and meeting advice which are not helpful, I thought my life was over. Existing devoid of the approaches to the problems you have fixed all through your guide is a critical case, as well as ones that could have in a wrong way affected my career if I hadn’t noticed your web page. Your training and kindness in controlling the whole lot was vital. I’m not sure what I would’ve done if I had not discovered such a thing like this. It’s possible to at this time look forward to my future. Thanks so much for your high quality and effective guide. I won’t think twice to recommend your web site to any person who should have care about this subject matter.
Hi there, I discovered your blog via Google whilst searching for a comparable topic, your web site came up, it appears good. I’ve bookmarked it in my google bookmarks.
I’m not sure where you are getting your info, but great topic. I needs to spend some time learning more or understanding more. Thanks for great information I was looking for this information for my mission.
My brother suggested I might like this web site. He was totally right. This post truly made my day. You cann’t imagine just how much time I had spent for this info! Thanks!
I like what you guys are up too. Such clever work and reporting! Carry on the superb works guys I¡¦ve incorporated you guys to my blogroll. I think it’ll improve the value of my site 🙂
Heya i’m for the first time here. I came across this board and I find It really useful & it helped me out much. I hope to give something back and help others like you aided me.
My spouse and i got very contented that John managed to finish up his investigations with the precious recommendations he obtained when using the site. It is now and again perplexing to just continually be giving away solutions which some people might have been selling. And we discover we now have the writer to appreciate for this. These illustrations you have made, the straightforward website navigation, the friendships your site help to instill – it’s got everything remarkable, and it is helping our son and us do think the issue is thrilling, which is certainly very vital. Thanks for the whole thing!
A person necessarily help to make significantly posts I might state. That is the first time I frequented your website page and thus far? I surprised with the research you made to create this particular post incredible. Magnificent task!
We are a group of volunteers and starting a new scheme in our community. Your site provided us with valuable information to work on. You have done an impressive job and our entire community will be grateful to you.
I do not even know how I ended up here, but I thought this post was good. I do not know who you are but definitely you’re going to a famous blogger if you are not already 😉 Cheers!
Great web site. A lot of helpful info here. I’m sending it to some buddies ans also sharing in delicious. And naturally, thanks on your effort!
My brother recommended I might like this website. He was entirely right. This post truly made my day. You cann’t imagine simply how much time I had spent for this information! Thanks!
I got what you intend, thanks for posting .Woh I am delighted to find this website through google. “The test and use of a man’s education is that he finds pleasure in the exercise of his mind.” by Carl Barzun.
I together with my guys appeared to be studying the good ideas found on your web site and at once I had a horrible feeling I never expressed respect to you for those strategies. These men became for that reason warmed to read them and have now certainly been tapping into them. Thanks for simply being well accommodating as well as for making a choice on this kind of extraordinary things millions of individuals are really desperate to discover. My personal sincere regret for not expressing gratitude to earlier.
Heya i’m for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you aided me.
I have been absent for a while, but now I remember why I used to love this website. Thank you, I will try and check back more often. How frequently you update your website?
Thank you a bunch for sharing this with all folks you actually know what you are talking about! Bookmarked. Kindly also discuss with my website =). We can have a link alternate agreement between us!
Heya i’m for the first time here. I came across this board and I find It really useful & it helped me out a lot. I hope to give something back and help others like you helped me.
fantastic points altogether, you simply won a logo new reader. What might you recommend about your post that you simply made some days in the past? Any certain?
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I’ll be subscribing to your augment and even I achievement you access consistently rapidly.
I have read some just right stuff here. Certainly price bookmarking for revisiting. I surprise how so much attempt you set to make such a great informative site.
I have been browsing on-line more than 3 hours these days, but I by no means discovered any interesting article like yours. It is pretty worth enough for me. Personally, if all website owners and bloggers made good content as you did, the net will be much more useful than ever before.
I wanted to compose a quick word so as to express gratitude to you for these wonderful points you are placing at this site. My considerable internet search has finally been rewarded with pleasant facts and techniques to write about with my colleagues. I would tell you that most of us site visitors actually are unquestionably endowed to be in a really good site with many wonderful professionals with good points. I feel rather lucky to have seen your entire web site and look forward to many more brilliant moments reading here. Thanks a lot again for all the details.
I¡¦ve read a few excellent stuff here. Certainly price bookmarking for revisiting. I wonder how much effort you set to create the sort of magnificent informative web site.
Just want to say your article is as astonishing. The clearness in your post is simply excellent and i could assume you’re an expert on this subject. Fine with your permission let me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please keep up the enjoyable work.
Of course, what a great website and informative posts, I definitely will bookmark your site.Have an awsome day!
Excellent read, I just passed this onto a colleague who was doing a little research on that. And he actually bought me lunch because I found it for him smile Therefore let me rephrase that: Thank you for lunch!
Coming from my research, shopping for electronics online can for sure be expensive, but there are some how-to’s that you can use to acquire the best bargains. There are continually ways to come across discount promotions that could make one to ge thet best consumer electronics products at the lowest prices. Good blog post.
hello there and thank you for your information – I’ve certainly picked up something new from right here. I did however expertise a few technical points using this site, since I experienced to reload the website lots of times previous to I could get it to load properly. I had been wondering if your hosting is OK? Not that I’m complaining, but sluggish loading instances times will often affect your placement in google and can damage your high-quality score if ads and marketing with Adwords. Anyway I am adding this RSS to my email and could look out for much more of your respective intriguing content. Make sure you update this again soon..
I cling on to listening to the rumor speak about getting free online grant applications so I have been looking around for the most excellent site to get one. Could you advise me please, where could i acquire some?
You completed a number of nice points there. I did a search on the subject and found most folks will go along with with your blog.
you are truly a just right webmaster. The website loading speed is incredible. It sort of feels that you are doing any unique trick. Moreover, The contents are masterwork. you’ve performed a great job on this topic!
I loved as much as you will receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get got an edginess over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly a lot often inside case you shield this hike.
Hey there, I think your blog might be having browser compatibility issues. When I look at your blog in Ie, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, amazing blog!
But wanna comment that you have a very decent site, I love the layout it really stands out.
I figured out more new stuff on this weight reduction issue. One particular issue is a good nutrition is especially vital any time dieting. An enormous reduction in junk food, sugary food, fried foods, sugary foods, red meat, and bright flour products could possibly be necessary. Holding wastes harmful bacteria, and contaminants may prevent goals for shedding fat. While certain drugs in the short term solve the challenge, the bad side effects are not worth it, plus they never present more than a momentary solution. It is a known indisputable fact that 95 of diet plans fail. Thank you for sharing your opinions on this site.
Hmm it seemsappearslooks like your sitewebsiteblog ate my first comment (it was extremelysuper long) so I guess I’ll just sum it up what I submittedhad writtenwrote and say, I’m thoroughly enjoying your blog. I as welltoo am an aspiring blog bloggerwriter but I’m still new to the whole thingeverything. Do you have any helpful hintsrecommendationstips and hintspointssuggestionstips for inexperiencedfirst-timerookienovicebeginnernewbie blog writers? I’d certainlydefinitelygenuinelyreally appreciate it.
alwaysall the timeconstantlycontinuouslyeach time i used to read smaller articlespostsarticles or reviewscontent whichthat alsoas well clear their motive, and that is also happening with this articlepostpiece of writingparagraph which I am reading hereat this placeat this timenow.
Utterly pent articles , regards for information .
I’ll immediately grab your rss as I can not in finding your e-mail subscription link or newsletter service. Do you have any? Please allow me recognise in order that I may just subscribe. Thanks.
Great paintings! This is the type of info that should be shared across the net. Disgrace on Google for no longer positioning this submit higher! Come on over and visit my site . Thanks =)
You actually make it seem really easy with your presentation however I in finding this matter to be actually something that I feel I might never understand. It sort of feels too complicated and very huge for me. I’m having a look forward in your next put up, I will try to get the hold of it!
Thank you for any other informative web site. The place else could I am getting that kind of info written in such an ideal manner? I’ve a mission that I am just now working on, and I have been at the glance out for such info.
Thank you, I’ve just been searching for information approximately this subject for ages and yours is the greatest I have discovered so far. However, what in regards to the bottom line? Are you positive in regards to the supply?
You really make it seem so easy with your presentation but I find this topic to be actually something that I think I would never understand. It seems too complex and very broad for me. I’m looking forward for your next post, I will try to get the hang of it!
hello!,I like your writing so so much! proportion we keep up a correspondence more approximately your article on AOL? I need a specialist in this area to unravel my problem. May be that is you! Taking a look forward to see you.
Attractive section of content. I just stumbled upon your weblog and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Anyway I will be subscribing to your augment and even I achievement you access consistently quickly.
Hello.This article was extremely interesting, especially because I was searching for thoughts on this matter last Sunday.
Well I truly liked reading it. This article offered by you is very constructive for accurate planning.
I am so happy to read this. This is the kind of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this greatest doc.
I truly appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thank you again!
My wife and i ended up being really comfortable when Albert managed to finish up his inquiry out of the precious recommendations he discovered through your web site. It is now and again perplexing to simply find yourself handing out helpful hints which usually many people have been selling. And we all consider we now have the writer to be grateful to for that. The main explanations you’ve made, the easy site navigation, the relationships you help promote – it’s everything spectacular, and it is facilitating our son and our family know that that situation is fun, which is rather pressing. Thanks for all!
I simply wanted to compose a comment to be able to appreciate you for the remarkable concepts you are giving out on this website. My extended internet look up has finally been recognized with good content to go over with my family. I ‘d point out that we website visitors actually are truly blessed to dwell in a magnificent community with so many lovely people with useful basics. I feel extremely lucky to have used the website and look forward to plenty of more entertaining times reading here. Thanks a lot once again for everything.
I have not checked in here for a while because I thought it was getting boring, but the last several posts are great quality so I guess I¡¦ll add you back to my daily bloglist. You deserve it my friend 🙂
Perfectly composed content, thank you for selective information. “You can do very little with faith, but you can do nothing without it.” by Samuel Butler.
I was recommendedsuggested this blogwebsiteweb site by my cousin. I amI’m not sure whether this post is written by him as no onenobody else know such detailed about my problemdifficultytrouble. You areYou’re amazingwonderfulincredible! Thanks!
One other issue is that if you are in a problem where you do not have a cosigner then you may really need to try to wear out all of your financing options. You’ll find many funds and other free college funding that will ensure that you get funds to assist with school expenses. Thank you for the post.
I was just searching for this information for a while. After 6 hours of continuous Googleing, at last I got it in your site. I wonder what’s the lack of Google strategy that don’t rank this type of informative web sites in top of the list. Generally the top websites are full of garbage.
One more thing I would like to say is that instead of trying to fit all your online degree training on days that you end work (considering that people are drained when they get back), try to obtain most of your instructional classes on the weekends and only a couple courses in weekdays, even if it means taking some time off your weekend break. This pays off because on the week-ends, you will be more rested along with concentrated upon school work. Thx for the different points I have realized from your site.
Normally I do not read article on blogs, but I would like to say that this write-up very compelled me to check out and do it! Your writing style has been amazed me. Thank you, very nice article.
of course like your web site but you have to check the spelling on several of your posts. Many of them are rife with spelling problems and I find it very bothersome to tell the truth nevertheless I will certainly come back again.
I’ve recently started a website, the information you offer on this website has helped me greatly. Thanks for all of your time & work.
You made some decent points there. I did a search on the topic and found most individuals will approve with your website.
Every weekend i used to visitgo to seepay a visitpay a quick visit this websiteweb sitesiteweb page, becauseasfor the reason that i wantwish for enjoyment, sinceasfor the reason that this this websiteweb sitesiteweb page conations reallyactuallyin facttrulygenuinely nicepleasantgoodfastidious funny stuffinformationdatamaterial too.
I am so happy to read this. This is the type of manual that needs to be given and not the random misinformation that’s at the other blogs. Appreciate your sharing this best doc.
Hi my family member! I wish to say that this article is awesome, great written and include approximately all vital infos. I would like to look extra posts like this.
You could certainly see your skills within the work you write. The world hopes for even more passionate writers such as you who aren’t afraid to say how they believe. At all times follow your heart. “Golf and sex are about the only things you can enjoy without being good at.” by Jimmy Demaret.
I and my pals ended up digesting the excellent procedures located on the blog then all of the sudden I had a terrible suspicion I never thanked the site owner for them. Most of the people appeared to be totally joyful to read them and now have really been enjoying these things. I appreciate you for indeed being considerably accommodating and then for choosing this kind of terrific issues millions of individuals are really eager to discover. Our own sincere apologies for not saying thanks to you earlier.
Hi there, just became aware of your blog through Google, and found that it’s truly informative. I am gonna watch out for brussels. I’ll be grateful if you continue this in future. A lot of people will be benefited from your writing. Cheers!
I am also writing to let you be aware of of the excellent discovery my friend’s daughter gained using your webblog. She came to find a good number of issues, with the inclusion of what it is like to possess an awesome giving character to get other individuals really easily understand specified hard to do subject areas. You truly surpassed our own expected results. Thanks for producing such helpful, healthy, informative and even unique tips on this topic to Kate.
Hey there, You have done a fantastic job. I will definitely digg it and personally recommend to my friends. I am sure they’ll be benefited from this web site.
You made some clear points there. I looked on the internet for the issue and found most people will approve with your blog.
Very nice post and straight to the point. I don’t know if this is actually the best place to ask but do you people have any thoughts on where to hire some professional writers? Thank you 🙂
You actually make it seem so easy with your presentation but I find this topic to be really something that I think I would never understand. It seems too complicated and extremely broad for me. I’m looking forward for your next post, I will try to get the hang of it!
magnificent points altogether, you simply received a brand new reader. What could you suggest in regards to your post that you just made a few days in the past? Any positive?
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you can do with a few pics to drive the message home a little bit, but instead of that, this is magnificent blog. An excellent read. I will definitely be back.
Great blog here! Additionally your web site quite a bit up fast! What web host are you using? Can I am getting your affiliate link in your host? I want my website loaded up as fast as yours lol
Very interesting subject, thank you for posting.
Hi my family member! I want to say that this post is amazing, great written and include approximately all important infos. I would like to look more posts like this.
Its superb as your other posts : D, thanks for posting . “Before borrowing money from a friend it’s best to decide which you need most.” by Joe Moore.
Very interesting information!Perfect just what I was looking for! “You have to be deviant if you’re going to do anything new.” by David Lee.
F*ckin’ tremendous issues here. I’m very satisfied to see your post. Thank you a lot and i’m having a look ahead to contact you. Will you kindly drop me a mail?
This is my first time visitgo to seepay a visitpay a quick visit at here and i am reallyactuallyin facttrulygenuinely impressedhappypleassant to read alleverthing at onealonesingle place.
Great write-up, I¡¦m regular visitor of one¡¦s web site, maintain up the nice operate, and It is going to be a regular visitor for a long time.
fantastic points altogether, you just gained a new reader. What could you recommend about your publish that you simply made some days in the past? Any certain?
Heya i am for the first time here. I came across this board and I find It really useful & it helped me out a lot. I hope to give something back and aid others like you aided me.
It is the best time to make some plans for the future and it is time to be happy. I have read this post and if I could I desire to suggest you some interesting things or advice. Maybe you can write next articles referring to this article. I wish to read more things about it!
Very good written story. It will be useful to anybody who usess it, as well as myself. Keep doing what you are doing – i will definitely read more posts.
I was just searching for this information for some time. After six hours of continuous Googleing, finally I got it in your site. I wonder what is the lack of Google strategy that do not rank this kind of informative sites in top of the list. Generally the top sites are full of garbage.
What i don’t understood is in truth how you’re no longer really a lot more neatly-liked than you may be right now. You are so intelligent. You understand therefore significantly relating to this topic, produced me in my view imagine it from a lot of varied angles. Its like men and women don’t seem to be interested except it¡¦s something to accomplish with Lady gaga! Your individual stuffs great. All the time maintain it up!
Nice blog here! Also your website loads up very fast! What web host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
Thank you a bunch for sharing this with all of us you actually realize what you’re talking approximately! Bookmarked. Please additionally seek advice from my site =). We may have a link alternate contract among us!
HiWhat’s upHi thereHello alleverybodyevery one, here every oneevery person is sharing suchthesethese kinds of experienceknowledgefamiliarityknow-how, sothustherefore it’s nicepleasantgoodfastidious to read this blogweblogwebpagewebsiteweb site, and I used to visitgo to seepay a visitpay a quick visit this blogweblogwebpagewebsiteweb site everydaydailyevery dayall the time.
Hello very cool website!! Guy .. Excellent .. Superb .. I will bookmark your site and take the feeds additionally¡KI am happy to seek out a lot of useful information right here in the put up, we need work out extra techniques in this regard, thanks for sharing. . . . . .
You are my inspiration , I own few blogs and often run out from to brand.
howdy, puissant blog on blubbery loss. parallel helped.
Thank you, I’ve just been searching for info about this subject for a long time and yours is the best I’ve found out so far. But, what in regards to the bottom line? Are you sure about the supply?
Bonjour ! Par contre ca mérite plus d’infos et de creuser,non ?
Hey there, You have done an excellent job. I’ll definitely digg it and personally recommend to my friends. I am sure they will be benefited from this web site.
I am so happy to read this. This is the kind of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this greatest doc.
My brother recommended I might like this web site. He was totally right. This post actually made my day. You cann’t imagine simply how much time I had spent for this information! Thanks!
My wife and i ended up being now joyful Emmanuel could finish up his investigations because of the precious recommendations he came across in your web pages. It is now and again perplexing to just find yourself freely giving ideas that people have been trying to sell. And now we fully understand we need you to thank because of that. The main explanations you made, the straightforward web site menu, the friendships you can help to foster – it is all sensational, and it’s facilitating our son and us do think this topic is enjoyable, which is certainly rather essential. Many thanks for all!
I am not sure where you’re getting your info, but great topic. I needs to spend some time learning much more or understanding more. Thanks for magnificent info I was looking for this information for my mission.
Wow! This could be one particular of the most beneficial blogs We’ve ever arrive across on this subject. Basically Wonderful. I’m also a specialist in this topic therefore I can understand your hard work.
Hiya, I am really glad I have found this info. Today bloggers publish only about gossips and internet and this is actually frustrating. A good site with exciting content, this is what I need. Thanks for keeping this website, I will be visiting it. Do you do newsletters? Can’t find it.
I enjoy you because of every one of your work on this web site. Betty really likes getting into research and it’s really simple to grasp why. Most of us hear all about the dynamic manner you make worthwhile items via your web site and as well attract response from people on that situation so my princess is without a doubt starting to learn a lot of things. Enjoy the remaining portion of the new year. You have been conducting a really good job.
I have been browsing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. Personally, if all website owners and bloggers made good content as you did, the internet will be much more useful than ever before.
I like what you guys are up too. Such clever work and reporting! Keep up the excellent works guys I’ve incorporated you guys to my blogroll. I think it will improve the value of my site :).
Wow, awesome blog structure! How lengthy have you been running a blog for? you make running a blog look easy. The full look of your web site is magnificent, as neatly as the content!
Hi, i think that i saw you visited my blog so i came to “return the favor”.I’m trying to find things to enhance my website!I suppose its ok to use a few of your ideas!!
hello!,I love your writing very so much! percentage we keep in touch more approximately your article on AOL? I require a specialist in this house to unravel my problem. May be that’s you! Having a look forward to look you.
My brother recommended I might like this website. He was totally right. This post actually made my day. You can not imagine simply how much time I had spent for this information! Thanks!
I genuinely enjoy reading through on this web site , it holds excellent articles . “Dream no small dreams. They have no power to stir the souls of men.” by Victor Hugo.
Real excellent info can be found on web site. “The greatest mistake is trying to be more agreeable than you can be.” by Walter Bagehot.
Hey, you used to write magnificent, but the last several posts have been kinda boring… I miss your great writings. Past several posts are just a little out of track! come on!
You have noted very interesting points! ps nice internet site.
I have not checked in here for some time since I thought it was getting boring, but the last several posts are good quality so I guess I’ll add you back to my everyday bloglist. You deserve it my friend 🙂
Pretty section of content. I just stumbled upon your website and in accession capital to assert that I acquire actually enjoyed account your blog posts. Anyway I’ll be subscribing to your feeds and even I achievement you access consistently rapidly.
I just wanted to post a small comment to thank you for all of the precious information you are writing on this site. My extended internet research has finally been recognized with good concept to write about with my guests. I would believe that many of us website visitors actually are undeniably fortunate to be in a wonderful place with many brilliant professionals with helpful hints. I feel really lucky to have seen your entire website and look forward to many more fabulous times reading here. Thanks a lot again for all the details.
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research about this. We got a grab a book from our area library but I think I learned more from this post. I am very glad to see such magnificent info being shared freely out there.
Bonjour ! J’aime beaucoup cependant peut un ou deux truc qu’il faudrait revoir à mon avis ! Sans prétention bien sur
I have not checked in here for some time because I thought it was getting boring, but the last few posts are good quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
I in addition to my pals happened to be taking note of the best advice found on the website then quickly came up with a terrible feeling I had not thanked the blog owner for those strategies. All the young men appeared to be warmed to read them and have absolutely been taking pleasure in those things. We appreciate you actually being simply helpful and then for picking some nice useful guides millions of individuals are really wanting to discover. My personal honest apologies for not saying thanks to earlier.
Terrific work! That is the type of info that are supposed to be shared around the internet. Disgrace on Google for no longer positioning this post higher! Come on over and visit my site . Thank you =)
Hi there, just became aware of your blog through Google, and found that it’s really informative. I’m going to watch out for brussels. I’ll appreciate if you continue this in future. Numerous people will be benefited from your writing. Cheers!
hello there and thank you for your information – I have definitely picked up something new from right here. I did however expertise a few technical issues using this website, as I experienced to reload the web site a lot of times previous to I could get it to load correctly. I had been wondering if your hosting is OK? Not that I’m complaining, but sluggish loading instances times will sometimes affect your placement in google and can damage your high quality score if advertising and marketing with Adwords. Well I’m adding this RSS to my e-mail and could look out for a lot more of your respective fascinating content. Ensure that you update this again soon..
I¡¦ve recently started a site, the info you offer on this website has helped me greatly. Thanks for all of your time & work.
hi!,I really like your writing so so much! proportion we keep up a correspondence extra approximately your post on AOL? I require a specialist on this space to resolve my problem. Maybe that is you! Looking forward to see you.
Thank you so much for providing individuals with an exceptionally nice chance to read critical reviews from this website. It is often very amazing and as well , stuffed with a good time for me and my office co-workers to visit your site at a minimum 3 times in one week to read through the new stuff you will have. Not to mention, I’m also actually impressed for the excellent suggestions you give. Selected two facts on this page are in truth the most efficient I’ve ever had.
fantastic issues altogether, you simply won a new reader. What may you suggest in regards to your publish that you just made a few days in the past? Any positive?
Hello there, I found your website by the use of Google at the same time as looking for a related topic, your website came up, it appears great. I’ve bookmarked it in my google bookmarks.
Thank you a lot for sharing this with all people you really recognize what you are talking approximately! Bookmarked. Please also discuss with my website =). We can have a hyperlink trade contract between us!
You actually make it seem so easy with your presentation but I find this topic to be actually something that I think I would never understand. It seems too complicated and extremely broad for me. I am looking forward for your next post, I will try to get the hang of it!
I as well as my buddies have been looking through the good secrets and techniques found on your web page and then quickly I had a horrible feeling I never expressed respect to the site owner for those strategies. The boys became as a result glad to learn them and already have very much been loving these things. Thank you for truly being really considerate and for utilizing varieties of important information millions of individuals are really desirous to know about. My very own sincere regret for not expressing appreciation to you earlier.
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research about this. We got a grab a book from our area library but I think I learned more clear from this post. I’m very glad to see such wonderful info being shared freely out there.
Nice read, I just passed this onto a friend who was doing a little research on that. And he just bought me lunch since I found it for him smile Thus let me rephrase that: Thanks for lunch! “We have two ears and one mouth so that we can listen twice as much as we speak.” by Epictetus.
I’ll right away take hold of your rss feed as I can not in finding your e-mail subscription link or e-newsletter service. Do you’ve any? Kindly allow me understand in order that I may just subscribe. Thanks.
Pretty section of content. I just stumbled upon your site and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently fast.
Hello, Neat post. There’s a problem along with your website in web explorer, might test this¡K IE still is the marketplace chief and a good component of other folks will omit your excellent writing because of this problem.
Fairly intriguing suggestions you have said, thank you so much for setting up.
It’s nearly unthinkable to see well-educated individual on this area, however you come across as like you comprehend which you’re revealing! Thank You
I take pleasure in, cause I discovered exactly what I was taking a look for. You have ended my 4 day long hunt! God Bless you man. Have a nice day. Bye
I in addition to my pals were reading through the excellent information on your website while all of the sudden got a horrible feeling I had not thanked the web site owner for those strategies. Those guys had been as a result glad to study all of them and have now honestly been making the most of these things. I appreciate you for actually being very thoughtful and then for going for this kind of fine guides millions of individuals are really desirous to be aware of. My very own sincere regret for not expressing gratitude to earlier.
Hello my family member! I want to say that this post is amazing, great written and come with almost all significant infos. I¡¦d like to look more posts like this .
You are a very capable individual!
Noticeably intriguing points that you have stated, say thanks a lot for putting up.
It really is nearly extremely difficult to encounter well-educated men and women on this theme, even though you appear like you are familiar with those things you’re revealing! Thanks
Thanks for some other excellent post. Where else may just anybody get that type of information in such an ideal way of writing? I’ve a presentation next week, and I am at the look for such information.
I simply intend to notify you that I am new to wordpress blogging and completely loved your page. Quite possibly I am going to bookmark your blog post . You really have excellent article content. Get Pleasure From it for discussing with us your own url post
It can be practically unthinkable to see well-updated men and women on this content, fortunately you appear like you are familiar with whatever you’re talking about! With Thanks
Really enlightening data you have stated, thanks for publishing.
Its wonderful as your other posts : D, regards for posting . “It takes less time to do things right than to explain why you did it wrong.” by Henry Wadsworth Longfellow.
It’s actually mostly impossible to encounter well-qualified people on this matter, however , you come across as like you comprehend which you’re indicating! Appreciate It
Good site! I truly love how it is easy on my eyes and the data are well written. I am wondering how I might be notified when a new post has been made. I’ve subscribed to your feed which must do the trick! Have a nice day!
I gotta favorite this web site it seems very helpful extremely helpful
It is actually practically close to impossible to encounter well-educated individuals on this theme, still you come across as like you know the things that you’re preaching about! Thank You
Generally I do not learn article on blogs, however I would like to say that this write-up very pressured me to check out and do so! Your writing style has been amazed me. Thank you, very nice post.
I merely desire to advise you that I am new to online blogging and utterly adored your report. Very likely I am going to save your blog post . You truly have fabulous article content. Admire it for expressing with us your very own url write-up
It certainly is nearly close to impossible to come across well-updated visitors on this area, however you come across as like you understand those things you’re writing about! Appreciate It
Unbelievably beneficial advice that you have remarked, a big heads up for publishing.
Genuinely compelling knowledge you’ll have remarked, thanks a lot for writing.
Perfectly composed subject material , thankyou for selective information .
Thank you, I’ve recently been searching for information approximately this subject for a long time and yours is the greatest I have came upon so far. However, what in regards to the bottom line? Are you positive concerning the source?
It certainly is near unthinkable to find well-advised men or women on this niche, and yet you appear like you are familiar with the things that you’re posting on! Thank You
I merely intend to reveal to you that I am new to putting up a blog and genuinely adored your site. Very likely I am likely to save your blog post . You really have impressive article content. Love it for sharing with us your current web webpage
It’s actually almost unthinkable to encounter well-advised users on this area, nevertheless you come across as like you are familiar with those things you’re covering! Cheers
Pretty absorbing highlights you have mentioned, warm regards for publishing.
you’re truly a good webmaster. The site loading pace is amazing. It sort of feels that you’re doing any distinctive trick. In addition, The contents are masterwork. you have performed a great activity in this topic!
It’s nearly extremely difficult to see well-advised individual on this matter, but you seem like you fully understand the things that you’re preaching about! Appreciation
I simply need to reveal to you that I am new to writing a blog and certainly admired your website. Probably I am likely to save your blog post . You simply have extraordinary article materials. Like it for expressing with us your current domain information
Of course, what a magnificent site and informative posts, I surely will bookmark your website.Best Regards!
What i do not realize is in fact how you’re no longer actually a lot more neatly-preferred than you might be now. You are very intelligent. You recognize thus considerably with regards to this subject, made me for my part imagine it from numerous numerous angles. Its like women and men are not interested until it is something to do with Lady gaga! Your personal stuffs excellent. All the time care for it up!
Whats Happening i am new to this, I stumbled upon this I have found It positively useful and it has helped me out loads. I am hoping to contribute & assist different users like its helped me. Great job.
Excellent blog here! Also your web site loads up very fast! What web host are you using? Can I get your affiliate link to your host? I wish my site loaded up as quickly as yours lol
Hello.This post was really remarkable, especially since I was investigating for thoughts on this issue last Friday.
I simply wanted to thank you very much all over again. I’m not certain the things that I would have gone through without the solutions shown by you on such a area of interest. It had been a real distressing scenario for me personally, nevertheless taking a look at a new expert technique you treated it made me to leap over joy. I am just happier for the information and as well , wish you are aware of a great job you have been providing training other individuals through your web page. I’m certain you haven’t come across any of us.
What i don’t realize is if truth be told how you’re no longer really much more well-liked than you may be now. You are so intelligent. You recognize thus significantly in relation to this subject, produced me in my opinion consider it from numerous various angles. Its like women and men don’t seem to be involved until it¡¦s something to accomplish with Woman gaga! Your personal stuffs excellent. Always deal with it up!
Hello. excellent job. I did not expect this. This is a splendid story. Thanks!
I haven¡¦t checked in here for some time since I thought it was getting boring, but the last several posts are good quality so I guess I will add you back to my daily bloglist. You deserve it my friend 🙂
Someone essentially help to make significantly articles I would state. This is the first time I frequented your web page and to this point? I amazed with the research you made to create this actual submit incredible. Magnificent activity!
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how could we communicate?
hey there and thank you for your information – I have definitely picked up something new from right here. I did however expertise a few technical points using this site, since I experienced to reload the web site a lot of times previous to I could get it to load correctly. I had been wondering if your web hosting is OK? Not that I’m complaining, but slow loading instances times will sometimes affect your placement in google and can damage your quality score if advertising and marketing with Adwords. Anyway I am adding this RSS to my email and can look out for a lot more of your respective exciting content. Make sure you update this again very soon..
Usually I don’t learn article on blogs, however I wish to say that this write-up very pressured me to try and do so! Your writing taste has been surprised me. Thanks, very nice post.
I have been absent for some time, but now I remember why I used to love this blog. Thanks, I will try and check back more frequently. How frequently you update your site?
I haveI’ve been surfingbrowsing onlineon-line more thangreater than three3 hours these daysnowadaystodaylatelyas of late, yetbut I neverby no means founddiscovered any interestingfascinatingattention-grabbing article like yours. It’sIt is lovelyprettybeautiful worthvalueprice enoughsufficient for me. In my opinionPersonallyIn my view, if all webmasterssite ownerswebsite ownersweb owners and bloggers made just rightgoodexcellent contentcontent material as you didyou probably did, the internetnetweb will beshall bemight bewill probably becan bewill likely be much morea lot more usefulhelpful than ever before.
Just a smiling visitant here to share the love (:, btw outstanding style and design. “Make the most of your regrets… . To regret deeply is to live afresh.” by Henry David Thoreau.
My spouse and IWeMy partner and I stumbled over here coming from afrom aby a different web pagewebsitepageweb address and thought I mightmay as wellmight as wellshould check things out. I like what I see so now i amnow i’mi am just following you. Look forward to going overexploringfinding out aboutlooking overchecking outlooking atlooking into your web page againyet againfor a second timerepeatedly.
What I have constantly told men and women is that when looking for a good internet electronics retail store, there are a few components that you have to take into consideration. First and foremost, you need to make sure to discover a reputable as well as reliable shop that has got great opinions and scores from other people and market sector people. This will make sure that you are getting along with a well-known store providing you with good assistance and help to it’s patrons. Many thanks sharing your notions on this blog site.
Somebody essentially help to make severely posts I might state. That is the first time I frequented your web page and up to now? I surprised with the research you made to create this particular publish extraordinary. Fantastic job!
My spouse and i got absolutely excited that Peter could complete his inquiry from your ideas he acquired from your weblog. It’s not at all simplistic just to always be giving freely guides which men and women could have been making money from. And we all already know we need the website owner to be grateful to because of that. The illustrations you made, the simple web site menu, the relationships you give support to engender – it is most fabulous, and it’s letting our son and us reason why the article is fun, which is certainly pretty pressing. Many thanks for the whole thing!
Thankyou for helping out, good info .
I’m really impressed with your writing skills as well as with the layout on your blog. Is this a paid theme or did you modify it yourself? Either way keep up the nice quality writing, it’s rare to see a great blog like this one these days..
Thanks a lot for providing individuals with remarkably nice possiblity to read from this blog. It’s usually so enjoyable and as well , packed with a great time for me personally and my office acquaintances to visit your website not less than 3 times in one week to see the newest items you have got. And indeed, I’m also at all times pleased considering the fantastic advice you serve. Certain 1 facts in this article are really the most efficient I’ve ever had.
Enjoyed looking at this, very good stuff, appreciate it. “Whenever you want to marry someone, go have lunch with his ex-wife.” by Francis William Bourdillon.
Wow, superb blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is magnificent, let alone the content!
This is very interesting, You are a very skilled blogger. I’ve joined your rss feed and look forward to seeking more of your fantastic post. Also, I have shared your website in my social networks!
Merely wanna comment on few general things, The website style and design is perfect, the subject material is very wonderful. “If a man does his best, what else is there” by George Smith Patton, Jr..
Utterly composed articles , thankyou for selective information .
Great weblog here! Also your site quite a bit up very fast! What host are you the use of? Can I get your associate link for your host? I want my site loaded up as fast as yours lol
Excellent read, I just passed this onto a colleague who was doing some research on that. And he actually bought me lunch because I found it for him smile Thus let me rephrase that: Thank you for lunch!
I was suggested this website by my cousin. I’m not sure whether this post is written by him as no one else know such detailed about my difficulty. You’re wonderful! Thanks!
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently quickly.
It’s really a great and helpful piece of information. I’m happy that you just shared this useful information with us. Please stay us informed like this. Thank you for sharing.
Fantastic website. Lots of useful information here. I’m sending it to several buddies ans also sharing in delicious. And obviously, thanks to your sweat!
I’ve been absent for a while, but now I remember why I used to love this site. Thanks, I will try and check back more often. How frequently you update your web site?
Dead indited content , thanks for entropy.
Excellent read, I just passed this onto a colleague who was doing a little research on that. And he just bought me lunch as I found it for him smile Thus let me rephrase that: Thank you for lunch! “There are places and moments in which one is so completely alone that one sees the world entire.” by Jules Renard.
Some really choice articles on this website , bookmarked .
It is truly a nice and useful piece of information. I am satisfied that you shared this useful information with us. Please stay us informed like this. Thank you for sharing.
Hi there, I discovered your site by means of Google while looking for a comparable topic, your web site came up, it appears to be like great. I have bookmarked it in my google bookmarks.
Simply want to say your article is as astonishing. The clearness in your post is simply great and i can assume you’re an expert on this subject. Well with your permission allow me to grab your feed to keep updated with forthcoming post. Thanks a million and please carry on the enjoyable work.
I have been absent for a while, but now I remember why I used to love this website. Thank you, I¡¦ll try and check back more frequently. How frequently you update your site?
Thank you a lot for providing individuals with an extraordinarily brilliant possiblity to read in detail from this web site. It is often so pleasurable and packed with a good time for me personally and my office peers to search the blog a minimum of thrice in a week to read the fresh guidance you will have. And of course, I’m also certainly satisfied considering the astounding opinions you give. Selected 1 tips on this page are indeed the most beneficial we’ve ever had.
Someone necessarily lend a hand to make severely posts I’d state. That is the first time I frequented your website page and so far? I amazed with the analysis you made to create this actual post amazing. Excellent task!
I like this website very much, Its a very nice office to read and obtain info . “Reason is not measured by size or height, but by principle.” by Epictetus.
Hey There. I found your blog using msn. This is an extremely well written article. I’ll be sure to bookmark it and come back to read more of your useful information. Thanks for the post. I’ll certainly return.
I’m no longer positive where you are getting your info, however good topic. I needs to spend a while finding out much more or understanding more. Thanks for fantastic info I used to be on the lookout for this information for my mission.
You made certain fine points there. I did a search on the topic and found the majority of people will have the same opinion with your blog.
I like the helpful information you provide in your articles. I will bookmark your blog and check again here regularly. I am quite certain I will learn a lot of new stuff right here! Best of luck for the next!
It¡¦s truly a great and helpful piece of information. I¡¦m satisfied that you simply shared this useful info with us. Please stay us up to date like this. Thank you for sharing.
Hey There. I found your blog using msn. This is an extremely well written article. I’ll make sure to bookmark it and return to read more of your useful information. Thanks for the post. I’ll certainly return.
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thank you again!
Thank you, I’ve just been searching for information approximately this topic for a long time and yours is the best I’ve found out so far. However, what concerning the bottom line? Are you positive about the source?
A person essentially lend a hand to make critically posts I’d state. This is the first time I frequented your website page and so far? I amazed with the research you made to make this actual post extraordinary. Great job!
I think you have noted some very interesting details , appreciate it for the post.
Thanks for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our area library but I think I learned more clear from this post. I am very glad to see such wonderful info being shared freely out there.
I’m not sure where you are getting your information, but great topic. I needs to spend some time learning much more or understanding more. Thanks for wonderful info I was looking for this info for my mission.
I’m just commenting to let you understand of the fantastic discovery our princess found going through your site. She realized many issues, with the inclusion of how it is like to possess a very effective coaching character to let other folks without hassle grasp several complicated matters. You really did more than readers’ desires. Thank you for churning out the warm and helpful, healthy, informative as well as fun thoughts on that topic to Emily.
There is noticeably a bunch to identify about this. I feel you made various good points in features also.
I wanted to type a simple note to be able to appreciate you for those marvelous tactics you are giving here. My particularly long internet lookup has at the end been compensated with wonderful facts and strategies to exchange with my great friends. I ‘d assert that most of us readers actually are definitely fortunate to dwell in a really good network with so many marvellous professionals with good advice. I feel truly grateful to have come across your entire website page and look forward to some more fun times reading here. Thank you again for all the details.
I was suggested this blog by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my problem. You’re wonderful! Thanks!
Very interesting details you have mentioned , appreciate it for posting . “There is nothing in a caterpillar that tells you it’s going to be a butterfly.” by Richard Buckminster Fuller.
Heya i am for the first time here. I found this board and I find It really useful & it helped me out much. I hope to give something back and help others like you aided me.
I keep listening to the news talk about receiving boundless online grant applications so I have been looking around for the top site to get one. Could you tell me please, where could i acquire some?
I and also my guys happened to be going through the nice secrets and techniques found on your site while before long came up with an awful suspicion I had not expressed respect to the blog owner for them. All of the boys ended up for this reason passionate to study them and have now in fact been having fun with those things. Thanks for genuinely so helpful and then for deciding upon this kind of good things millions of individuals are really needing to be aware of. My very own sincere regret for not saying thanks to you sooner.
You actually make it seem so easy with your presentation but I find this matter to be really something that I think I would never understand. It seems too complicated and extremely broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
whoah this weblog is wonderful i like studying your articles. Stay up the great work! You understand, lots of people are searching around for this information, you could help them greatly.
Of course, what a fantastic site and educative posts, I will bookmark your website.All the Best!
I am not sure where you are getting your information, but good topic. I needs to spend a while studying more or figuring out more. Thank you for wonderful information I was looking for this info for my mission.
magnificent issues altogether, you simply won a new reader. What would you recommend about your submit that you just made a few days ago? Any positive?
A person essentially help to make significantly articles I’d state. That is the first time I frequented your website page and so far? I surprised with the analysis you made to make this particular post amazing. Wonderful task!
Awsome post and right to the point. I don’t know if this is actually the best place to ask but do you people have any thoughts on where to get some professional writers? Thanks in advance 🙂
I’m still learning from you, while I’m improving myself. I absolutely liked reading all that is written on your site.Keep the aarticles coming. I enjoyed it!
When I originally commented I appear to have clicked the -Notify me when new comments are added- checkbox and now every time a comment is added I receive four emails with the exact same comment. There has to be a means you can remove me from that service? Kudos!
Nice read, I just passed this onto a friend who was doing a little research on that. And he just bought me lunch because I found it for him smile Therefore let me rephrase that: Thanks for lunch!
Very nice article and straight to the point. I don’t know if this is really the best place to ask but do you folks have any ideea where to hire some professional writers? Thx 🙂
I was recommended this web site by my cousin. I am not sure whether this post is written by him as nobody else know such detailed about my difficulty. You are wonderful! Thanks!
I haven’t checked in here for some time since I thought it was getting boring, but the last few posts are great quality so I guess I’ll add you back to my daily bloglist. You deserve it my friend 🙂
Great work! That is the kind of information that are meant to be shared around the web. Disgrace on Google for not positioning this submit upper! Come on over and discuss with my website . Thank you =)
What i don’t understood is in truth how you are now not actually a lot more neatly-favored than you might be right now. You are very intelligent. You understand therefore significantly in the case of this matter, produced me personally imagine it from so many varied angles. Its like men and women are not interested unless it is something to accomplish with Lady gaga! Your personal stuffs great. Always handle it up!
of course like your web-site but you need to check the spelling on several of your posts. A number of them are rife with spelling issues and I in finding it very bothersome to tell the truth however I will certainly come back again.
I was looking at some of your posts on this website and I think this website is very instructive! Retain posting .
I like this website very much, Its a rattling nice position to read and find information. “A little in one’s own pocket is better than much in another man’s purse.” by Miguel de Cervantes.
I really like your writing style, fantastic information, thanks for posting : D.
I’ve recently started a site, the information you provide on this website has helped me tremendously. Thank you for all of your time & work. “The inner fire is the most important thing mankind possesses.” by Edith Sodergran.
Utterly pent content, thank you for information. “He who establishes his argument by noise and command shows that his reason is weak.” by Michel de Montaigne.
I like the efforts you have put in this, thanks for all the great posts.
Some truly quality content on this website , saved to bookmarks .
I like this weblog very much, Its a rattling nice billet to read and find info . “Young men think old men are fools but old men know young men are fools.” by George Chapman.
Thank you for any other informative web site. The place else could I am getting that type of information written in such a perfect way? I’ve a challenge that I’m just now working on, and I’ve been on the look out for such info.
Keep functioning ,fantastic job!
Oh my goodness! an incredible article dude. Thanks However I’m experiencing challenge with ur rss . Don’t know why Unable to subscribe to it. Is there anyone getting an identical rss drawback? Anybody who is aware of kindly respond. Thnkx
Good ¡V I should definitely pronounce, impressed with your web site. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, web site theme . a tones way for your client to communicate. Excellent task..
Keep functioning ,fantastic job!
Hi, I do think this is an excellent web site. I stumbledupon it 😉 I’m going to revisit yet again since i have book marked it. Money and freedom is the best way to change, may you be rich and continue to help others.
you are in reality a just right webmaster. The web site loading speed is amazing. It sort of feels that you’re doing any distinctive trick. In addition, The contents are masterpiece. you have performed a excellent job on this matter!
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research about this. We got a grab a book from our local library but I think I learned more clear from this post. I am very glad to see such excellent info being shared freely out there.
Dead written content material , regards for selective information .
hey there and thank you for your information – I’ve definitely picked up anything new from right here. I did however expertise several technical points using this site, as I experienced to reload the website many times previous to I could get it to load correctly. I had been wondering if your hosting is OK? Not that I’m complaining, but slow loading instances times will very frequently affect your placement in google and can damage your quality score if ads and marketing with Adwords. Anyway I am adding this RSS to my e-mail and could look out for much more of your respective interesting content. Ensure that you update this again very soon..
I truly wanted to write a quick note to be able to appreciate you for the nice guidelines you are sharing at this site. My extended internet lookup has finally been rewarded with reasonable details to share with my neighbours. I would repeat that many of us visitors actually are undeniably blessed to dwell in a fabulous community with many wonderful individuals with good tips and hints. I feel quite fortunate to have seen your entire website page and look forward to many more fabulous times reading here. Thank you again for everything.
I precisely needed to say thanks once again. I am not sure the things that I would have carried out without the information shown by you concerning this question. It was an absolute intimidating concern in my circumstances, however , being able to view a professional avenue you handled the issue took me to weep with contentment. I am happier for this guidance and even hope that you find out what an amazing job your are getting into educating some other people thru a site. Most likely you’ve never encountered all of us.
Helpful information. Fortunate me I found your site by accident, and I’m shocked why this coincidence did not took place in advance! I bookmarked it.
I truly appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thx again
I conceive you have noted some very interesting points , appreciate it for the post.
I appreciate, cause I discovered just what I used to be having a look for. You’ve ended my 4 day long hunt! God Bless you man. Have a great day. Bye
Hey There. I found your blog using msn. This is a really well written article. I’ll be sure to bookmark it and return to read more of your useful information. Thanks for the post. I will definitely comeback.
What i don’t realize is in truth how you are now not actually a lot more neatly-appreciated than you may be right now. You’re very intelligent. You recognize therefore considerably in relation to this subject, made me in my opinion consider it from so many various angles. Its like men and women aren’t interested until it is one thing to accomplish with Girl gaga! Your individual stuffs outstanding. Always take care of it up!
Someone essentially lend a hand to make significantly articles I would state. This is the first time I frequented your website page and up to now? I amazed with the analysis you made to create this actual put up amazing. Wonderful activity!
This website really has all of the information I needed about this subject and didn’t know who to ask.
Pretty nice post. I just stumbled upon your blog and wished to say that I’ve truly enjoyed browsing your blog posts. After all I will be subscribing to your rss feed and I hope you write again soon!
I’ve been surfing on-line greater than three hours these days, but I by no means discovered any attention-grabbing article like yours. It’s beautiful price enough for me. In my view, if all web owners and bloggers made excellent content as you did, the internet will be a lot more helpful than ever before. “It’s all right to have butterflies in your stomach. Just get them to fly in formation.” by Dr. Rob Gilbert.
How do I make firefox show at the top of my start list?
Somebody essentially assist to make critically articles I’d state. That is the very first time I frequented your web page and up to now? I surprised with the research you made to make this particular put up incredible. Magnificent job!
Hello there, just became aware of your blog through Google, and found that it is truly informative. I am going to watch out for brussels. I’ll appreciate if you continue this in future. Numerous people will be benefited from your writing. Cheers!
It¡¦s actually a nice and helpful piece of information. I am satisfied that you simply shared this helpful information with us. Please keep us up to date like this. Thank you for sharing.
Nice post. I was checking constantly this blog and I’m impressed! Very useful information specially the last part 🙂 I care for such info a lot. I was seeking this particular info for a long time. Thank you and best of luck.
I precisely wanted to thank you so much again. I do not know what I could possibly have made to happen without the advice shared by you on my subject matter. This was an absolute alarming case for me, nevertheless being able to view your specialised mode you resolved it forced me to cry for happiness. I am just happier for the assistance as well as believe you recognize what an amazing job you are providing educating people thru a web site. More than likely you’ve never come across any of us.
Wow! This could be one particular of the most helpful blogs We’ve ever arrive across on this subject. Basically Fantastic. I am also an expert in this topic so I can understand your hard work.
It is the best time to make some plans for the future and it is time to be happy. I have read this post and if I could I wish to suggest you some interesting things or tips. Perhaps you could write next articles referring to this article. I wish to read even more things about it!
As a Newbie, I am constantly searching online for articles that can aid me. Thank you
Keep working ,great job!
you’re in point of fact a good webmaster. The site loading speed is amazing. It sort of feels that you’re doing any distinctive trick. Furthermore, The contents are masterpiece. you’ve performed a wonderful task on this subject!
I simply desired to thank you so much again. I do not know what I could possibly have undertaken without the type of concepts documented by you over that problem. It previously was a depressing dilemma in my circumstances, nevertheless taking a look at a well-written technique you resolved it took me to cry over delight. I am just happy for your guidance and as well , trust you really know what a great job you were getting into instructing the rest by way of your website. I am certain you’ve never encountered any of us.
I have fun with, result in I discovered just what I used to be taking a look for. You’ve ended my four day lengthy hunt! God Bless you man. Have a great day. Bye
I would like to thank you for the efforts you’ve put in writing this web site. I’m hoping the same high-grade website post from you in the upcoming also. In fact your creative writing abilities has inspired me to get my own site now. Actually the blogging is spreading its wings quickly. Your write up is a great example of it.
Hello, Neat post. There’s a problem along with your website in web explorer, may test this¡K IE still is the marketplace chief and a big component of people will omit your fantastic writing because of this problem.
This is really interesting, You’re a very skilled blogger. I have joined your feed and look forward to seeking more of your excellent post. Also, I have shared your web site in my social networks!
As I site possessor I believe the content matter here is rattling magnificent , appreciate it for your hard work. You should keep it up forever! Best of luck.
Simply want to say your article is as astounding. The clarity in your post is simply cool and i can assume you’re an expert on this subject. Fine with your permission allow me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the enjoyable work.
Some truly select blog posts on this internet site , saved to my bookmarks .
Hiya, I’m really glad I’ve found this information. Today bloggers publish just about gossips and internet and this is really irritating. A good web site with interesting content, this is what I need. Thank you for keeping this site, I will be visiting it. Do you do newsletters? Cant find it.
You are a very smart individual!
Hi there, just became aware of your blog through Google, and found that it’s truly informative. I am gonna watch out for brussels. I’ll be grateful if you continue this in future. Lots of people will be benefited from your writing. Cheers!
I simply couldn’t depart your site before suggesting that I really enjoyed the standard information a person supply for your visitors? Is gonna be back incessantly in order to check out new posts
You really make it seem so easy with your presentation but I find this matter to be really something that I think I would never understand. It seems too complicated and very broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
Wow! Thank you! I permanently wanted to write on my site something like that. Can I take a portion of your post to my blog?
hey there and thank you for your info – I’ve definitely picked up anything new from right here. I did however expertise several technical points using this site, as I experienced to reload the site lots of times previous to I could get it to load properly. I had been wondering if your web host is OK? Not that I’m complaining, but slow loading instances times will often affect your placement in google and can damage your quality score if advertising and marketing with Adwords. Anyway I am adding this RSS to my e-mail and can look out for much more of your respective intriguing content. Ensure that you update this again very soon..
Keep functioning ,impressive job!
Keep working ,splendid job!
Great ¡V I should definitely pronounce, impressed with your site. I had no trouble navigating through all the tabs and related info ended up being truly simple to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your customer to communicate. Excellent task..
I just want to tell you that I’m new to blogging and site-building and certainly loved your web-site. Almost certainly I’m want to bookmark your website . You actually have good stories. Kudos for sharing your website page.
Hey very cool site!! Guy .. Beautiful .. Amazing .. I’ll bookmark your website and take the feeds also¡KI’m satisfied to search out so many useful information here within the publish, we’d like work out more techniques on this regard, thanks for sharing. . . . . .
You made a few nice points there. I did a search on the issue and found mainly persons will agree with your blog.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! However, how could we communicate?
I just could not leave your site prior to suggesting that I extremely enjoyed the usual info an individual provide for your guests? Is gonna be again regularly in order to check up on new posts
I have been checking out many of your posts and i must say pretty nice stuff. I will make sure to bookmark your site.
I’ve been browsing on-line more than 3 hours lately, but I by no means discovered any attention-grabbing article like yours. It¡¦s beautiful value sufficient for me. In my view, if all website owners and bloggers made excellent content as you probably did, the net shall be a lot more useful than ever before.
I have read a few good stuff here. Certainly value bookmarking for revisiting. I wonder how a lot effort you place to make one of these wonderful informative website.
I simply had to appreciate you once more. I do not know the things I could possibly have sorted out without the type of hints provided by you on my problem. It was actually a very frightening scenario in my view, nevertheless observing the skilled way you handled it took me to leap for happiness. Now i’m thankful for this guidance and in addition have high hopes you are aware of a great job you happen to be getting into teaching people through the use of a web site. I am certain you haven’t got to know any of us.
Good blog! I truly love how it is simple on my eyes and the data are well written. I’m wondering how I could be notified whenever a new post has been made. I have subscribed to your RSS feed which must do the trick! Have a great day!
I’ve been absent for some time, but now I remember why I used to love this site. Thanks , I¡¦ll try and check back more frequently. How frequently you update your web site?
Simply want to say your article is as amazing. The clarity in your post is simply excellent and i can assume you’re an expert on this subject. Fine with your permission let me to grab your feed to keep updated with forthcoming post. Thanks a million and please carry on the enjoyable work.
Wow, superb blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is excellent, as well as the content!
I together with my guys were reviewing the good items located on your web site and immediately I had a horrible feeling I never expressed respect to you for them. All the boys appeared to be so passionate to read through all of them and already have simply been taking pleasure in these things. Appreciate your simply being so accommodating as well as for picking out this sort of wonderful information most people are really wanting to understand about. My personal honest apologies for not saying thanks to you sooner.
I have been reading out a few of your stories and i can state pretty clever stuff. I will make sure to bookmark your website.
Thanks for another fantastic article. The place else may just anyone get that type of information in such a perfect manner of writing? I have a presentation next week, and I’m on the search for such info.
Hey there, You have done a great job. I will certainly digg it and personally suggest to my friends. I am sure they’ll be benefited from this website.
I think other web-site proprietors should take this web site as an model, very clean and magnificent user genial style and design, let alone the content. You’re an expert in this topic!
Good blog! I truly love how it is simple on my eyes and the data are well written. I am wondering how I might be notified when a new post has been made. I have subscribed to your RSS which must do the trick! Have a nice day!
Excellent read, I just passed this onto a friend who was doing some research on that. And he actually bought me lunch as I found it for him smile So let me rephrase that: Thank you for lunch!
Outstanding post but I was wondering if you could write a litte more on this subject? I’d be very thankful if you could elaborate a little bit further. Thank you!
Just a smiling visitor here to share the love (:, btw outstanding layout.
HiHelloHi thereHello thereHowdyGreetings, I thinkI believeI do believeI do thinkThere’s no doubt that your siteyour websiteyour web siteyour blog might bemay becould becould possibly be having browserinternet browserweb browser compatibility issuesproblems. When IWhenever I look at yourtake a look at your websiteweb sitesiteblog in Safari, it looks fine but whenhowever whenhowever, ifhowever, when opening in Internet ExplorerIEI.E., it hasit’s got some overlapping issues. I justI simplyI merely wanted to give you aprovide you with a quick heads up! Other than thatApart from thatBesides thatAside from that, fantasticwonderfulgreatexcellent blogwebsitesite!
obviously like your web-site but you have to check the spelling on quite a few of your posts. Many of them are rife with spelling problems and I find it very troublesome to inform the truth nevertheless I’ll surely come again again.
I like the valuable info you provide in your articles. I will bookmark your weblog and check again here frequently. I am quite sure I’ll learn a lot of new stuff right here! Good luck for the next!
It happens to be right day to generate some plans for the longer term. I’ve study this document and if I should, I desire to recommend you handful of interesting instruction.
I am continually browsing online for tips that can assist me. Thanks!
Thank you, I’ve recently been searching for information about this topic for ages and yours is the greatest I’ve came upon so far. However, what in regards to the conclusion? Are you sure about the source?
Wow! This can be one particular of the most beneficial blogs We have ever arrive across on this subject. Basically Magnificent. I am also an expert in this topic so I can understand your effort.
Very interesting topic, thank you for posting.
Good – I should certainly pronounce, impressed with your website. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or something, web site theme . a tones way for your customer to communicate. Excellent task..
Wonderful website. Plenty of helpful info here. I¡¦m sending it to a few friends ans additionally sharing in delicious. And obviously, thanks on your sweat!
UndeniablyUnquestionablyDefinitely believeconsiderimagine that that youwhich you statedsaid. Your favouritefavorite justificationreason appeared to beseemed to be at theon the internetnetweb the simplesteasiest thingfactor to keep in mindbear in mindrememberconsidertake into accounthave in mindtake notebe mindfulunderstandbe awaretake into accout of. I say to you, I definitelycertainly get irkedannoyed at the same time aswhilsteven aswhile other folksfolksother peoplepeople considerthink about concernsworriesissues that they plainlyjust do notdon’t realizerecognizeunderstandrecogniseknow about. You controlledmanaged to hit the nail upon the topthe highest as smartlywellneatly asand alsoand definedoutlined out the whole thingthe entire thing with no needwithout having side effectside-effects , other folksfolksother peoplepeople cancould take a signal. Will likelyprobably be backagain to get more. Thank youThanks
Well I definitely liked studying it. This subject offered by you is very useful for good planning.
Howdy! I know this is kinda off topic nevertheless I’d figured I’d ask. Would you be interested in exchanging links or maybe guest authoring a blog article or vice-versa? My site goes over a lot of the same subjects as yours and I feel we could greatly benefit from each other. If you happen to be interested feel free to shoot me an email. I look forward to hearing from you! Great blog by the way!
Hi there, simply changed into aware of your blog via Google, and found that it is really informative. I’m going to be careful for brussels. I’ll be grateful when you continue this in future. Lots of other folks will likely be benefited out of your writing. Cheers!
Wow, superb weblog structure! How lengthy have you ever been running a blog for? you make running a blog glance easy. The whole glance of your website is magnificent, as well as the content!
Thanks for this!
I would like to voice my admiration for your kind-heartedness for those individuals that absolutely need help on in this field. Your personal dedication to passing the solution all through became astonishingly productive and have specifically enabled regular people just like me to achieve their pursuits. Your entire warm and helpful help and advice signifies this much a person like me and substantially more to my colleagues. Warm regards; from everyone of us.
With havin so much content and articleswritten contentcontent do you ever run into any problemsissues of plagorism or copyright violationinfringement? My websitesiteblog has a lot of completely uniqueexclusiveunique content I’ve either authoredcreatedwritten myself or outsourced but it looks likeappearsseems a lot of it is popping it up all over the webinternet without my agreementauthorizationpermission. Do you know any solutionstechniquesmethodsways to help protect againstreducestopprevent content from being ripped offstolen? I’d certainlydefinitelygenuinelytrulyreally appreciate it.
This excellent website really has all the information and facts I needed about this subject and didn’t know who to ask.
A motivating discussion is worth comment. I do believe that you should write more on this subject matter, it may not be a taboo subject but usually people don’t discuss these topics. To the next! Cheers!!
This is very interesting, You are a very skilled blogger. I’ve joined your rss feed and look forward to seeking more of your excellent post. Also, I’ve shared your web site in my social networks!
Heya i’m for the first time here. I found this board and I find It really useful & it helped me out a lot. I hope to give something back and aid others like you aided me.
I’m not sure where you are getting your info, but great topic. I needs to spend some time learning much more or understanding more. Thanks for excellent info I was looking for this info for my mission.
Hi, Neat post. There is an issue with your website in internet explorer, may check this¡K IE nonetheless is the marketplace chief and a huge part of people will pass over your fantastic writing because of this problem.
I’ll right away snatch your rss feed as I can not to find your email subscription hyperlink or newsletter service. Do you’ve any? Kindly let me recognise so that I may just subscribe. Thanks.
I intended to compose you that bit of note to say thanks over again for your personal pleasant tactics you have documented here. It is so remarkably open-handed with you giving publicly just what some people could possibly have marketed as an e-book to generate some bucks for their own end, notably seeing that you could have tried it if you considered necessary. These secrets likewise served to be the fantastic way to understand that other individuals have the identical eagerness just as mine to understand a lot more related to this matter. I believe there are millions of more pleasurable opportunities ahead for folks who take a look at your site.
Magnificent beat ! I wish to apprentice while you amend your web site, how could i subscribe for a blog site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear idea
Nice read, I just passed this onto a friend who was doing a little research on that. And he actually bought me lunch since I found it for him smile Therefore let me rephrase that: Thank you for lunch!
Thanks for every other fantastic post. The place else may just anybody get that type of information in such a perfect manner of writing? I’ve a presentation subsequent week, and I am on the search for such info.
Magnificent beat ! I would like to apprentice while you amend your website, how can i subscribe for a blog website? The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear idea
Someone essentially lend a hand to make critically articles I might state. That is the very first time I frequented your web page and up to now? I surprised with the analysis you made to create this actual submit incredible. Magnificent activity!
You can certainly see your enthusiasm in the paintings you write. The arena hopes for more passionate writers like you who aren’t afraid to say how they believe. All the time follow your heart.
An interesting dialogue is worth comment. I think that it’s best to write extra on this topic, it may not be a taboo subject however usually individuals are not enough to talk on such topics. To the next. Cheers
Nice blog here! Also your web site loads up fast! What host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as quickly as yours lol
I really enjoy examining on this site, it holds wonderful content . “One doesn’t discover new lands without consenting to lose sight of the shore for a very long time.” by Andre Gide.
I truly appreciate this post. I’ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again!
I have not checked in here for some time as I thought it was getting boring, but the last few posts are great quality so I guess I will add you back to my daily bloglist. You deserve it my friend 🙂
Wow! Thank you! I continuously needed to write on my blog something like that. Can I take a portion of your post to my blog?
Hello, i think that i saw you visited my web site thus i came to “return the favor”.I am trying to find things to enhance my site!I suppose its ok to use a few of your ideas!!
Wow! This can be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Fantastic. I am also an expert in this topic so I can understand your hard work.
I simply desired to thank you so much once more. I am not sure the things I could possibly have sorted out without the actual recommendations revealed by you over my topic. It was actually a fearsome scenario in my circumstances, but understanding your professional technique you dealt with the issue made me to weep for joy. I’m grateful for your help and in addition expect you really know what a great job you were undertaking instructing some other people with the aid of your site. I’m certain you’ve never encountered any of us.
Definitely believe that which you said. Your favorite reason seemed to be on the web the easiest thing to be aware of. I say to you, I certainly get annoyed while people think about worries that they plainly don’t know about. You managed to hit the nail upon the top and defined out the whole thing without having side-effects , people can take a signal. Will likely be back to get more. Thanks
I was looking at some of your content on this internet site and I believe this internet site is rattling informative! Keep posting.
My spouse and i got absolutely thrilled when Albert managed to do his investigations while using the ideas he was given out of your web site. It is now and again perplexing just to be giving away tricks which others might have been trying to sell. And we also discover we need you to appreciate for that. The most important illustrations you made, the simple blog navigation, the friendships your site make it easier to foster – it’s mostly astonishing, and it’s really letting our son in addition to our family reckon that that content is awesome, and that is rather important. Many thanks for all!
Awesome post. I am a normal visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Good write-up, I am regular visitor of one¡¦s website, maintain up the nice operate, and It is going to be a regular visitor for a long time.
Very nice post. I just stumbled upon your blog and wished to say that I’ve really enjoyed surfing around your blog posts. After all I will be subscribing to your rss feed and I hope you write again soon!
I like this web blog very much, Its a very nice spot to read and find info . “‘Taint’t worthwhile to wear a day all out before it comes.” by Sarah Orne Jewett.
Really nice layout and superb content , absolutely nothing else we want : D.
This is a topic that is close to my heart… Cheers! Where are your contact details though?
Hey, you used to write magnificent, but the last few posts have been kinda boring… I miss your super writings. Past several posts are just a bit out of track! come on!
Hello.This article was really remarkable, particularly because I was investigating for thoughts on this topic last week.
Hello there, You’ve done a great job. I will certainly digg it and personally suggest to my friends. I’m sure they will be benefited from this site.
Excellent weblog here! Additionally your site rather a lot up fast! What web host are you the use of? Can I am getting your affiliate hyperlink on your host? I wish my website loaded up as quickly as yours lol
I simply couldn’t leave your site prior to suggesting that I really loved the standard information an individual supply for your visitors? Is going to be again ceaselessly in order to check up on new posts
Whats Going down i’m new to this, I stumbled upon this I have found It positively helpful and it has aided me out loads. I’m hoping to give a contribution & assist different users like its helped me. Good job.
Awesome write-up. I’m a regular visitor of your site and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a really long time.
I’m so happy to read this. This is the kind of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this best doc.
I wanted to compose a brief message in order to appreciate you for all the nice advice you are placing here. My prolonged internet research has at the end of the day been rewarded with professional content to talk about with my contacts. I ‘d tell you that many of us website visitors actually are unequivocally endowed to exist in a really good community with many perfect individuals with good points. I feel really privileged to have used the webpages and look forward to really more amazing minutes reading here. Thanks a lot once more for everything.
Awesome post. I’m a regular visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossip and web stuff and this is actually frustrating. A good blog with exciting content, that’s what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
I as well as my buddies happened to be checking the best strategies found on your web page and then then came up with an awful suspicion I never thanked the blog owner for those techniques. Those men ended up certainly excited to see them and already have in truth been taking advantage of those things. Thank you for truly being really thoughtful and for opting for this form of important guides millions of individuals are really desperate to be informed on. Our sincere regret for not saying thanks to you earlier.
Only a smiling visitor here to share the love (:, btw outstanding design and style. “Make the most of your regrets… . To regret deeply is to live afresh.” by Henry David Thoreau.
Some truly nice and utilitarian information on this web site, besides I think the pattern holds superb features.
Wow, superb weblog layout! How long have you been running a blog for? you made running a blog look easy. The whole glance of your website is magnificent, let alone the content material!
Only wanna comment that you have a very nice site, I the design it really stands out.
I believe this web site contains some very excellent info for everyone :D. “Experience is not what happens to you it’s what you do with what happens to you.” by Aldous Huxley.
I’ll immediately snatch your rss as I can not in finding your e-mail subscription link or newsletter service. Do you have any? Please allow me recognise in order that I could subscribe. Thanks.
What i don’t realize is if truth be told how you’re not really a lot more neatly-liked than you might be right now. You are very intelligent. You understand therefore considerably on the subject of this matter, made me in my opinion believe it from a lot of varied angles. Its like women and men don’t seem to be involved until it is one thing to do with Lady gaga! Your own stuffs excellent. All the time handle it up!
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you could do with a few pics to drive the message home a bit, but instead of that, this is magnificent blog. A fantastic read. I’ll definitely be back.
I like the helpful info you provide in your articles. I’ll bookmark your weblog and check again here regularly. I am quite sure I’ll learn a lot of new stuff right here! Good luck for the next!
Great goods from you, man. I have understand your stuff previous to and you’re just too great. I actually like what you’ve acquired here, certainly like what you are saying and the way in which you say it. You make it enjoyable and you still care for to keep it sensible. I can not wait to read much more from you. This is actually a wonderful website.
You can certainly see your expertise within the paintings you write. The arena hopes for more passionate writers such as you who aren’t afraid to say how they believe. At all times go after your heart. “The most profound joy has more of gravity than of gaiety in it.” by Michel de Montaigne.
I’m not sure where you’re getting your info, but great topic. I needs to spend some time learning much more or understanding more. Thanks for magnificent information I was looking for this information for my mission.
Hello, i think that i saw you visited my blog thus i came to “return the favor”.I am attempting to find things to improve my website!I suppose its ok to use a few of your ideas!!
You have brought up a very great details , thankyou for the post.
Keep working ,terrific job!
I like the helpful information you provide in your articles. I will bookmark your weblog and check again here frequently. I’m quite sure I will learn many new stuff right here! Best of luck for the next!
Howdy very nice web site!! Guy .. Beautiful .. Superb .. I’ll bookmark your blog and take the feeds also…I’m satisfied to seek out so many useful information right here in the submit, we want develop more techniques on this regard, thanks for sharing.
I¡¦ve recently started a web site, the info you provide on this site has helped me tremendously. Thank you for all of your time & work.
I’m not sure where you’re getting your info, but great topic. I needs to spend some time learning much more or understanding more. Thanks for fantastic information I was looking for this information for my mission.
You have noted very interesting details ! ps nice website . “He that will not sail till all dangers are over must never put to sea.” by Thomas Fuller.
Really wonderful information can be found on website . “There used to be a real me, but I had it surgically removed.” by Peter Sellers.
It’s in reality a nice and helpful piece of information. I’m glad that you shared this useful info with us. Please keep us informed like this. Thank you for sharing.
Great paintings! This is the type of information that should be shared around the internet. Disgrace on the search engines for now not positioning this put up higher! Come on over and talk over with my website . Thanks =)
hi!,I like your writing very a lot! percentage we communicate more about your post on AOL? I require an expert in this house to unravel my problem. May be that is you! Taking a look forward to look you.
Just wanna input on few general things, The website design is perfect, the subject matter is really good. “Art for art’s sake makes no more sense than gin for gin’s sake.” by W. Somerset Maugham.
I do believe all the concepts you’ve presented for your post. They’re really convincing and will definitely work. Still, the posts are too brief for newbies. Could you please extend them a little from subsequent time? Thanks for the post.
Fantastic website. Plenty of useful info here. I am sending it to several buddies ans additionally sharing in delicious. And obviously, thanks on your sweat!
Thank you for sharing excellent informations. Your website is so cool. I’m impressed by the details that you have on this website. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for extra articles. You, my friend, ROCK! I found simply the information I already searched everywhere and just could not come across. What a perfect web-site.
Hey there. I found your blog by the use of Google whilst looking for a comparable matter, your web site got here up. It appears to be good. I’ve bookmarked it in my google bookmarks to come back then.
It can be almost unthinkable to find well-aware users on this theme, still you come across as like you know exactly what you’re talking about! Excellent
Hey, you used to write fantastic, but the last several posts have been kinda boring… I miss your super writings. Past several posts are just a little bit out of track! come on!
I dugg some of you post as I thought they were handy very useful
Excellent read, I just passed this onto a friend who was doing some research on that. And he actually bought me lunch as I found it for him smile Therefore let me rephrase that: Thank you for lunch! “By nature, men are nearly alike by practice, they get to be wide apart.” by Confucius.
I was looking at some of your content on this internet site and I conceive this website is rattling instructive! Continue putting up.
I have recently started a web site, the information you offer on this website has helped me tremendously. Thank you for all of your time & work. “Yield not to evils, but attack all the more boldly.” by Virgil.
I¡¦ve recently started a site, the info you provide on this website has helped me greatly. Thanks for all of your time & work.
I like the helpful information you provide in your articles. I’ll bookmark your blog and check again here frequently. I am quite sure I will learn lots of new stuff right here! Good luck for the next!
I’ve been surfing on-line greater than three hours nowadays, yet I by no means discovered any interesting article like yours. It is pretty worth sufficient for me. In my view, if all website owners and bloggers made good content material as you did, the net shall be a lot more helpful than ever before. “I thank God for my handicaps, for through them, I have found myself, my work and my God.” by Hellen Keller.
Spot on with this write-up, I really assume this web site needs way more consideration. I’ll in all probability be again to learn much more, thanks for that info.
I conceive you have observed some very interesting points , thankyou for the post.
I am continually searching online for tips that can aid me. Thx!
Well I truly enjoyed studying it. This subject offered by you is very practical for proper planning.
We are a group of volunteers and starting a new scheme in our community. Your web site provided us with valuable info to work on. You’ve done a formidable job and our entire community will be thankful to you.
I carry on listening to the news update speak about getting boundless online grant applications so I have been looking around for the finest site to get one. Could you tell me please, where could i get some?
I’m really enjoying the theme/design of your web site. Do you ever run into any internet browser compatibility problems? A couple of my blog readers have complained about my site not working correctly in Explorer but looks great in Firefox. Do you have any advice to help fix this problem?
magnificent points altogether, you just gained a new reader. What may you suggest about your put up that you just made a few days in the past? Any certain?
Great write-up, I’m normal visitor of one’s web site, maintain up the excellent operate, and It’s going to be a regular visitor for a long time.
I simply wished to thank you very much once more. I am not sure what I could possibly have accomplished in the absence of the type of secrets documented by you regarding this topic. Entirely was a daunting matter in my opinion, however , understanding a expert mode you treated it forced me to jump for delight. Extremely happy for this support and as well , trust you realize what a powerful job you are always undertaking teaching most people thru your blog post. Most likely you haven’t encountered all of us.
I’m really loving the theme/design of your web site. Do you ever run into any internet browser compatibility problems? A few of my blog audience have complained about my website not working correctly in Explorer but looks great in Chrome. Do you have any tips to help fix this problem?
Can I just say what a reduction to seek out someone who actually is aware of what theyre talking about on the internet. You undoubtedly know easy methods to carry a difficulty to mild and make it important. Extra folks need to learn this and perceive this facet of the story. I cant consider youre not more popular because you definitely have the gift.
hi!,I really like your writing so much! proportion we keep in touch extra about your post on AOL? I need an expert in this area to solve my problem. May be that’s you! Having a look forward to peer you.
Awesome write-up. I’m a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Hi! I know this is somewhat off topic but I was wondering which blog platform are you using for this website? I’m getting sick and tired of WordPress because I’ve had issues with hackers and I’m looking at alternatives for another platform. I would be fantastic if you could point me in the direction of a good platform.
I’m truly enjoying the design and layout of your website. It’s a very easy on the eyes which makes it much more enjoyable for me to come here and visit more often. Did you hire out a developer to create your theme? Exceptional work!
One thing is that one of the most prevalent incentives for using your credit cards is a cash-back as well as rebate provision. Generally, you’ll have access to 1-5 back with various buying. Depending on the card, you may get 1 again on most acquisitions, and 5 again on purchases made going to convenience stores, gasoline stations, grocery stores and also ‘member merchants’.
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish only about gossip and internet stuff and this is actually frustrating. A good web site with exciting content, that’s what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish only about gossip and internet stuff and this is actually irritating. A good blog with interesting content, this is what I need. Thanks for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
Hiya! I simply wish to give a huge thumbs up for the nice info you will have here on this post. I shall be coming back to your blog for more soon.
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish only about gossip and internet stuff and this is really irritating. A good blog with exciting content, that’s what I need. Thanks for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
Hey there. I discovered your web site by way of Google at the same time as looking for a related matter, your site came up. It appears great. I have bookmarked it in my google bookmarks to come back then.
Hiya, I am really glad I’ve found this info. Today bloggers publish only about gossip and web stuff and this is really irritating. A good site with interesting content, that is what I need. Thank you for making this web-site, and I will be visiting again. Do you do newsletters by email?
Simply wish to say your article is as astonishing. The clarity in your post is simply great, and I could assume you are an expert on this subject. Well with your permission let me grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the gratifying work.
Awesome post. I am a normal visitor of your site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Awesome post. I am a regular visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a really long time.
Hiya, I am really glad I’ve found this info. Nowadays bloggers publish only about gossip and web stuff and this is actually irritating. A good website with interesting content, that is what I need. Thank you for making this site, and I will be visiting again. Do you do newsletters by email?
Hiya, I am really glad I have found this info. Nowadays bloggers publish only about gossip and internet stuff and this is actually irritating. A good blog with exciting content, this is what I need. Thank you for making this web site, and I will be visiting again. Do you do newsletters by email?
Awesome write-up. I am a normal visitor of your web site and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a long time.
Hi there. I discovered your web site by way of Google even as looking for a related matter, your site got here up. It looks good. I have bookmarked it in my google bookmarks to visit then.
Hiya, I am really glad I have found this info. Nowadays bloggers publish only about gossip and web stuff and this is really annoying. A good website with interesting content, that is what I need. Thank you for making this site, and I’ll be visiting again. Do you do newsletters by email?
Hey there. I discovered your site by way of Google even as searching for a similar matter, your site came up. It looks good. I have bookmarked it in my google bookmarks to visit then.
Awesome write-up. I am a regular visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a long time.
Hey there. I discovered your web site by means of Google even as searching for a related topic, your site came up. It seems great. I’ve bookmarked it in my google bookmarks to visit then.
Awesome write-up. I’m a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hiya, I’m really glad I’ve found this information. Today bloggers publish just about gossip and web stuff and this is actually annoying. A good site with exciting content, that’s what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
Hey there. I found your website by way of Google at the same time as searching for a comparable subject, your site got here up. It seems good. I have bookmarked it in my google bookmarks to come back then.
Awesome write-up. I am a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Awesome write-up. I am a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a really long time.
Hey there. I found your website by the use of Google at the same time as looking for a related subject, your website came up. It looks good. I have bookmarked it in my google bookmarks to come back then.
Hiya, I am really glad I’ve found this info. Today bloggers publish only about gossip and internet stuff and this is really annoying. A good web site with exciting content, that’s what I need. Thanks for making this site, and I’ll be visiting again. Do you do newsletters by email?
Hello there. I found your blog by way of Google even as searching for a comparable subject, your site got here up. It seems great. I’ve bookmarked it in my google bookmarks to visit then.
Hiya, I’m really glad I have found this info. Today bloggers publish just about gossip and web stuff and this is really annoying. A good site with interesting content, that is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
Awesome write-up. I’m a regular visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a long time.
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish just about gossip and web stuff and this is actually irritating. A good blog with interesting content, that is what I need. Thanks for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I am really glad I have found this info. Nowadays bloggers publish only about gossip and web stuff and this is really annoying. A good blog with exciting content, that is what I need. Thank you for making this web site, and I will be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I have found this information. Nowadays bloggers publish just about gossip and internet stuff and this is really irritating. A good website with interesting content, this is what I need. Thank you for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hi there. I discovered your website by means of Google at the same time as looking for a similar matter, your web site came up. It looks good. I’ve bookmarked it in my google bookmarks to visit then.
Hello there. I discovered your website via Google even as searching for a similar topic, your web site got here up. It seems to be great. I’ve bookmarked it in my google bookmarks to visit then.
Hi there. I discovered your site via Google while looking for a similar subject, your website got here up. It looks good. I’ve bookmarked it in my google bookmarks to visit then.
Awesome post. I am a regular visitor of your web site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a long time.
Hiya, I’m really glad I have found this information. Nowadays bloggers publish just about gossip and web stuff and this is actually frustrating. A good website with interesting content, this is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
you’re in point of fact a just right webmaster. The website loading pace is amazing. It seems that you are doing any distinctive trick. Also, The contents are masterpiece. you have done a fantastic process in this matter!
Hi there. I found your web site by means of Google at the same time as searching for a similar topic, your website came up. It appears great. I’ve bookmarked it in my google bookmarks to visit then.
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish only about gossip and net stuff and this is really irritating. A good blog with exciting content, this is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
Hello there. I found your web site by means of Google even as looking for a comparable subject, your site got here up. It appears to be great. I’ve bookmarked it in my google bookmarks to visit then.
Awesome post. I’m a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Hello there. I discovered your web site by the use of Google whilst searching for a comparable topic, your web site came up. It seems good. I’ve bookmarked it in my google bookmarks to come back then.
Awesome write-up. I am a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a long time.
Awesome write-up. I am a normal visitor of your website and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a really long time.
Hey there. I discovered your blog via Google at the same time as looking for a comparable matter, your web site came up. It appears to be great. I’ve bookmarked it in my google bookmarks to visit then.
Awesome post. I am a normal visitor of your blog and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a long time.
Hiya, I am really glad I’ve found this info. Today bloggers publish only about gossip and net stuff and this is really annoying. A good site with interesting content, this is what I need. Thank you for making this site, and I will be visiting again. Do you do newsletters by email?
Hiya, I am really glad I have found this information. Today bloggers publish only about gossip and web stuff and this is actually annoying. A good web site with exciting content, this is what I need. Thanks for making this web site, and I will be visiting again. Do you do newsletters by email?
Awesome write-up. I’m a normal visitor of your blog and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a long time.
Hey there. I discovered your site via Google while searching for a comparable subject, your site came up. It appears to be great. I have bookmarked it in my google bookmarks to come back then.
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish just about gossip and net stuff and this is actually annoying. A good web site with interesting content, that is what I need. Thank you for making this web site, and I will be visiting again. Do you do newsletters by email?
Hey there. I found your site by the use of Google while searching for a similar subject, your web site got here up. It looks great. I’ve bookmarked it in my google bookmarks to visit then.
Hi there. I discovered your site by the use of Google whilst looking for a similar subject, your site came up. It looks good. I have bookmarked it in my google bookmarks to visit then.
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossip and web stuff and this is really irritating. A good web site with interesting content, that is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
There is clearly a lot to know about this. I think you made some good points in features also.
Awesome write-up. I’m a normal visitor of your website and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a really long time.
Hiya, I’m really glad I’ve found this information. Today bloggers publish just about gossip and net stuff and this is really frustrating. A good blog with exciting content, this is what I need. Thank you for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I am really glad I’ve found this info. Today bloggers publish just about gossip and net stuff and this is actually irritating. A good site with exciting content, that is what I need. Thanks for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Awesome write-up. I am a normal visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Hey there. I found your site by way of Google whilst searching for a related topic, your website got here up. It appears good. I have bookmarked it in my google bookmarks to come back then.
Hey there. I found your site via Google at the same time as searching for a comparable subject, your website got here up. It appears great. I’ve bookmarked it in my google bookmarks to come back then.
Awesome write-up. I am a normal visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a long time.
Awesome post. I’m a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a really long time.
Hi there. I discovered your website by means of Google at the same time as searching for a similar subject, your site came up. It appears to be great. I have bookmarked it in my google bookmarks to visit then.
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you could do with a few pics to drive the message home a little bit, but instead of that, this is excellent blog. A great read. I’ll definitely be back.
Hi there. I found your blog by means of Google at the same time as searching for a related topic, your site came up. It looks great. I’ve bookmarked it in my google bookmarks to visit then.
Hey there. I found your site by the use of Google while searching for a comparable topic, your website came up. It appears to be great. I have bookmarked it in my google bookmarks to come back then.
Awesome write-up. I’m a regular visitor of your site and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Hiya, I’m really glad I have found this info. Nowadays bloggers publish just about gossip and web stuff and this is actually irritating. A good site with exciting content, that’s what I need. Thank you for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
Hey there. I found your blog by means of Google whilst looking for a similar subject, your site came up. It seems great. I have bookmarked it in my google bookmarks to visit then.
Hello there. I found your blog via Google while looking for a comparable subject, your website got here up. It seems to be good. I have bookmarked it in my google bookmarks to come back then.
Hiya, I am really glad I’ve found this information. Today bloggers publish only about gossip and net stuff and this is really frustrating. A good website with interesting content, this is what I need. Thank you for making this site, and I will be visiting again. Do you do newsletters by email?
Awesome post. I am a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a long time.
I think this is one of the most significant info for me. And i’m glad reading your article. But want to remark on few general things, The website style is wonderful, the articles is really great : D. Good job, cheers
Awesome write-up. I am a regular visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a really long time.
I am no longer positive the place you’re getting your information, however great topic. I must spend some time learning much more or working out more. Thanks for fantastic information I was looking for this information for my mission.
Awesome post. I’m a normal visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a long time.
I simply wanted to say thanks again. I do not know what I would have handled in the absence of the creative concepts shared by you regarding such a subject. Completely was a difficult case in my opinion, nevertheless coming across the well-written form you treated it made me to jump for happiness. I will be happy for this work and thus hope you recognize what a great job your are doing training other individuals through your web page. I am certain you’ve never encountered any of us.
Hello there. I found your website via Google whilst looking for a comparable topic, your website came up. It appears great. I have bookmarked it in my google bookmarks to visit then.
Hi there. I discovered your web site by means of Google even as looking for a comparable matter, your website came up. It looks good. I have bookmarked it in my google bookmarks to visit then.
Awesome post. I’m a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a long time.
Hi there. I found your site by way of Google even as looking for a similar matter, your website got here up. It seems great. I’ve bookmarked it in my google bookmarks to visit then.
I have been examinating out a few of your stories and i can state pretty clever stuff. I will surely bookmark your blog.
Attractive section of content. I just stumbled upon your web site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I will be subscribing to your augment and even I achievement you access consistently rapidly.
Hiya, I am really glad I have found this info. Nowadays bloggers publish just about gossip and web stuff and this is really irritating. A good site with exciting content, this is what I need. Thanks for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish just about gossip and internet stuff and this is really annoying. A good blog with exciting content, that is what I need. Thank you for making this site, and I’ll be visiting again. Do you do newsletters by email?
Hi there. I found your web site by way of Google while searching for a related subject, your site came up. It appears good. I’ve bookmarked it in my google bookmarks to come back then.
Hiya, I am really glad I have found this info. Today bloggers publish just about gossip and net stuff and this is really irritating. A good site with exciting content, that’s what I need. Thanks for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish just about gossip and internet stuff and this is really irritating. A good blog with interesting content, that’s what I need. Thanks for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hey there. I discovered your blog by the use of Google at the same time as looking for a similar topic, your site got here up. It appears to be great. I’ve bookmarked it in my google bookmarks to come back then.
Awesome post. I’m a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Keep working ,fantastic job!
of course like your web-site but you have to check the spelling on several of your posts. Many of them are rife with spelling problems and I in finding it very troublesome to inform the reality however I¡¦ll definitely come again again.
Whats Going down i am new to this, I stumbled upon this I have discovered It absolutely helpful and it has helped me out loads. I’m hoping to contribute & aid other users like its aided me. Good job.
I’m very happy to read this. This is the type of manual that needs to be given and not the random misinformation that’s at the other blogs. Appreciate your sharing this best doc.
Yes! Finally someone writes about cumbersome.
A person necessarily assist to make critically posts I’d state. That is the first time I frequented your web page and to this point? I surprised with the research you made to create this particular put up amazing. Magnificent activity!
Great article! Thanks for this very useful detail and I hope everyone else will find it helpful too.
I ‘d mention that most of us visitors are endowed to exist in a fabulous place with very many wonderful individuals with very helpful things.
Good write-up, I am regular visitor of one¡¦s website, maintain up the excellent operate, and It is going to be a regular visitor for a long time.
Normally I don’t read an article on blogs, however, I would like to say that this write-up on this worth-sharing article very pressured me to try and do so!
I want to show my affection for your kind-heartedness giving support to all those that must have assistance with this particular niche. Your very own commitment to getting the solution across had become particularly important and have continuously empowered individuals much like me to get to their targets. Your helpful key points means much a person like me and substantially more to my mates. With thanks; from everyone of us.
The young boys ended up stimulated to read through them and now have unquestionably been having fun with these things.
I don’t knowdo not know if it’swhether it’s just me or ifif perhaps everyone elseeverybody else experiencingencountering problems withissues with your blogyour websiteyour site. It seems likeIt appears likeIt appears as ifIt looks likeIt appears as though some of the textwritten text on yourwithin yourin your postscontent are running off the screen. Can someone elsesomebody else please commentprovide feedback and let me know if this is happening to them tooas well? This mightThis couldThis may be a problemissue with my browserweb browserinternet browser because I’ve had this happen beforepreviously. ThanksKudosAppreciate itCheersThank youMany thanks
Respect to post author, some good information .
I do believe all of the concepts you have presented on your post.They’re very convincing and can certainly work. Nonetheless,the posts are very quick for newbies. May justyou please lengthen them a little from subsequent time?Thank you for the post.
An attention-grabbing dialogue is value comment. I believe that you require to write far more on this matter, it won’t be a taboo topic even so normally individuals are not sufficient to speak on such topics. To the next. Cheers
This guy has something very important to say!
I have been absent for some time, but now I remember why I used to love this blog. Thank you, I will try and check back more frequently. How frequently you update your website?
Thanks for sharing the post.. parents are worlds best person in each lives of individual..they need or must succeed to sustain needs of the family.
Utterly indited subject matter, Really enjoyed studying.
(Very useful article, this is definitely very helpful for a website. Thanks
Those guidelines additionally worked to become a good way to recognize that other people online have the identical fervor like mine to grasp great deal more around this condition.
The information you have posted is very useful. The sites you have referred was good. Thanks for sharing
Those guidelines additionally worked to become a good way to recognize that other people online have the identical fervor like mine to grasp great deal more around this condition.
Its like you read my mind! You seemappear to know so mucha lot about this, like you wrote the book in it or something. I think that you couldcan do with somea few pics to drive the message home a bita little bit, but other thaninstead of that, this is greatwonderfulfantasticmagnificentexcellent blog. A greatAn excellentA fantastic read. I’llI will definitelycertainly be back.
I don’tdo not even know how I ended up here, but I thought this post was goodgreat. I don’tdo not know who you are but definitelycertainly you areyou’re going to a famous blogger if you are notaren’t already 😉 Cheers!
It’s great to encounter a blog every once in a while which is not the same from date rehashed material. Fantastic read.
Very handy article, this is unquestionably very valuable to get a website. Thanks. Thumb up for this particular informative article.
Appreciation for really being considerate and for deciding on certain fantastic guides most people really would like to be conscious of.
Hello! This is my first visit to your blog! We are a group of volunteers and beginning a brand new initiative in a neighborhood in precisely the exact same niche. Your site provided us helpful information to operate on. You have done an outstanding job. {
Hello there, just became alert to your blog through Google, and found that it is really informative. I’m gonna watch out for brussels. I’ll appreciate if you continue this in future. A lot of people will be benefited from your writing. Cheers!
Thank youThanks for sharing your infothoughts. I trulyreally appreciate your efforts and I amwill be waiting for your nextfurther postwrite ups thank youthanks once again.
Please allow me to know if you’re searching for an author for your website. You have some great articles, and I believe I’d be a fantastic asset. Should you ever want to take some of this load off, then I’d like to write some content to your site in exchange for a link back to mine. Please take me an email if interested. Thanks. {