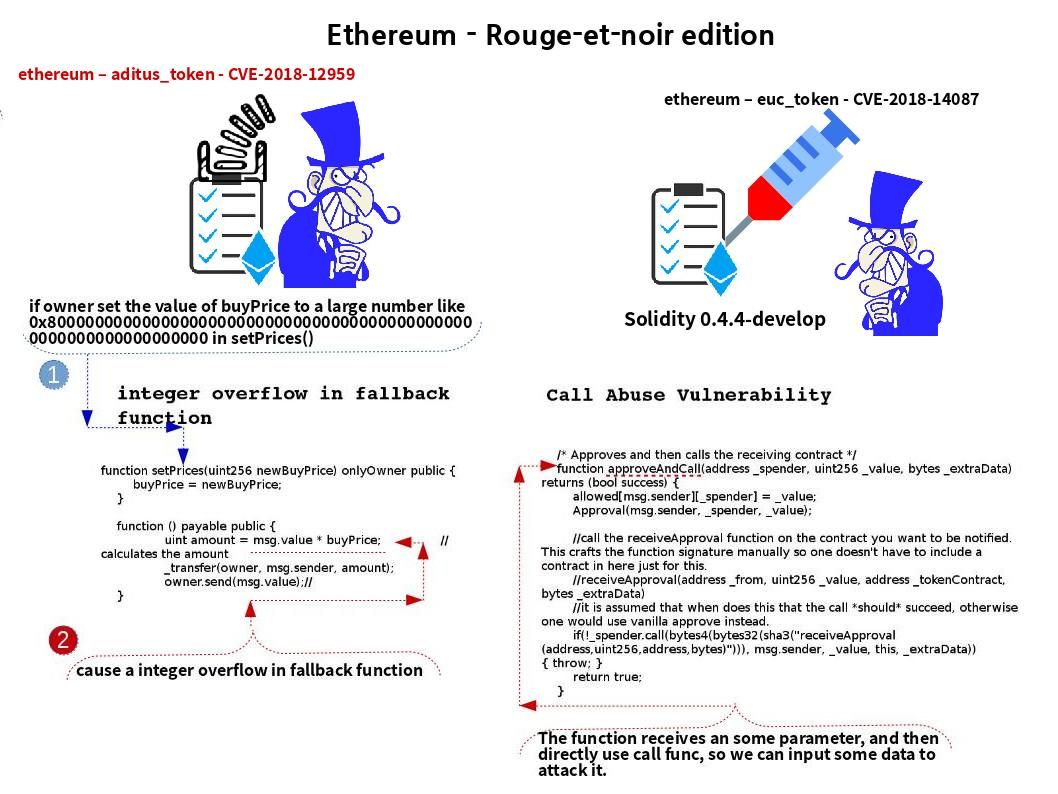
An Integer Overflow is the condition that occurs when the result of an arithmetic operation, such as multiplication or addition, exceeds the maximum size of the integer type used to store it. Ethereum hits such vulnerability in frequent. The solidity programming language rescue Ethererum in the cryptocurrency world. But no prefect things in the world. A vulnerability found on Ethereum EUC token recently. The EUC token build by solidity programming language. The guru given his nick name “call abused” vulnerability. For details, please see below hyperlink for references.
Ethereum EUC Token (call abused) – CVE-2018-14087
https://github.com/rootclay/Audit-of-smart-contracts/tree/master/0x8810C63470d38639954c6B41AaC545848C46484a
Additional information – Ethereum integer overflow vulnerabilities
Ethereum aditus token (CV-2018-12959):
https://github.com/hellowuzekai/blockchains/blob/master/overflow2.md
Ethereum mkcb_token:
https://github.com/hellowuzekai/blockchains/blob/master/README.md
Ethereum singaporecoinorigin token:
https://github.com/hellowuzekai/blockchains/blob/master/overflow1.md
Ethereum stex white list token:
https://github.com/hellowuzekai/blockchains/blob/master/overflow3.md
Ethereum tracto token:
https://github.com/tracto2/Tracto-ERC20/issues/1
Ethereum virgo zodiactoken token:
https://github.com/hellowuzekai/blockchains/blob/master/transferFrom.md
Not belongs to integer overflow vulnerability:
Ethereum userwallet 0x0a7bca9fb7af-f26c6ed8029b-b6f0f5d291587c42 token:
https://github.com/hellowuzekai/blockchains/blob/master/delegatecall.md