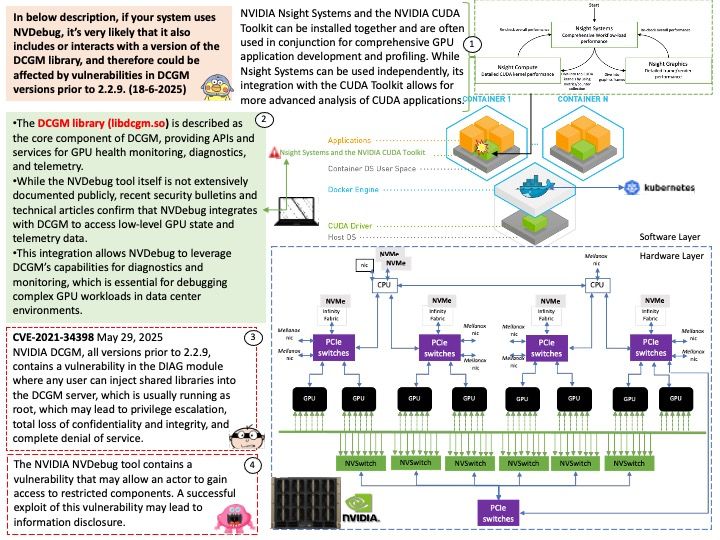
Preface: AI and machine learning workloads rely on optimized object storage to handle the massive, unstructured datasets needed for training and operation. NVIDIA AIStore (AIS) aims to overcome the limitations of traditional filesystems in handling large AI datasets by providing a distributed storage system that can handle the demands of modern AI models.
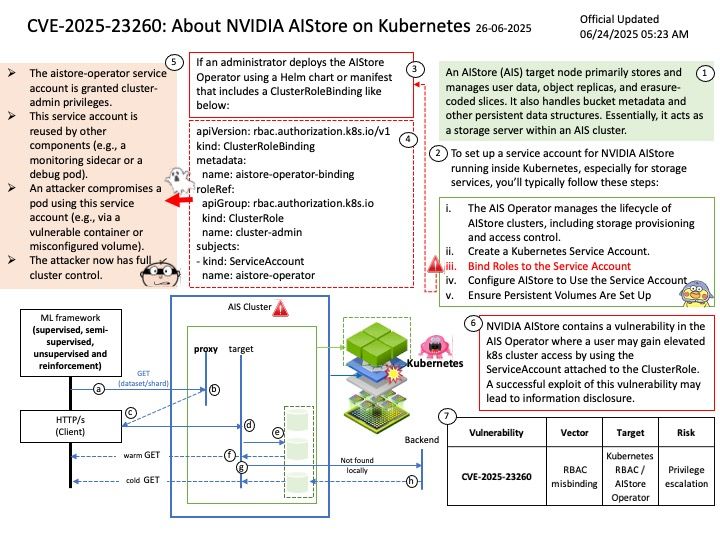
Background: An AIStore (AIS) target node primarily stores and manages user data, object replicas, and erasure-coded slices. It also handles bucket metadata and other persistent data structures. Essentially, it acts as a storage server within an AIS cluster.
To set up a service account for NVIDIA AIStore running inside Kubernetes, especially for storage services, you’ll typically follow these steps:
(1) The AIS Operator manages the lifecycle of AIStore clusters, including storage provisioning and access control.
(2) Create a Kubernetes Service Account.
(3) Bind Roles to the Service Account
(4) Configure AIStore to Use the Service Account
(5) Ensure Persistent Volumes Are Set Up
Vulnerability details: NVIDIA AIStore contains a vulnerability in the AIS Operator where a user may gain elevated k8s cluster access by using the ServiceAccount attached to the ClusterRole. A successful exploit of this vulnerability may lead to information disclosure.
Official announcement: Please see the link for details – https://nvidia.custhelp.com/app/answers/detail/a_id/5660