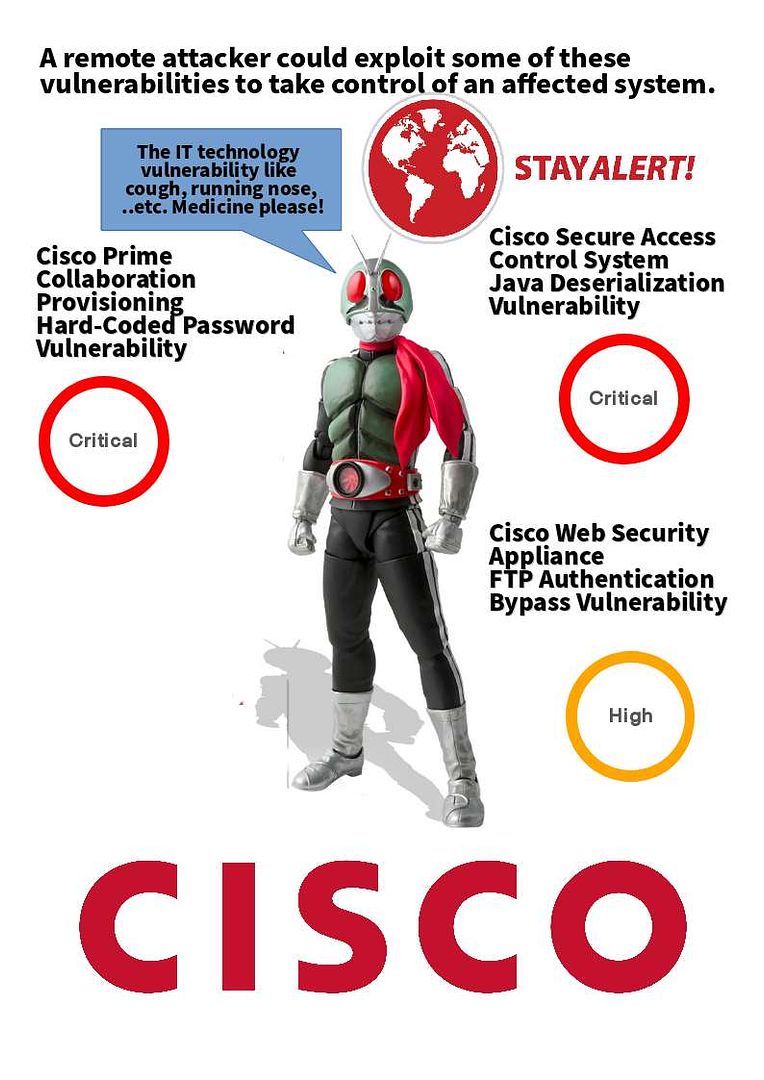
As of this month, Cisco found more vulnerabilities just this month. It looks that network equipment provider will be felt Microsoft pain since they have web server and java applet. For more details, please refer below:
CVE-2018-0087 – A vulnerability in the FTP server of the Cisco Web Security Appliance (WSA) could allow an unauthenticated, remote attacker to log in to the FTP server of the device without a valid password. (High)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-wsa
CVE-2018-0220 – A vulnerability in the web-based management interface of Cisco Videoscape AnyRes Live could allow an authenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the web-based management interface of an affected device. (Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-val
CVE-2018-0219 – A vulnerability in the web-based management interface of Cisco Unified Computing System (UCS) Director could allow an unauthenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the web-based management interface of an affected device.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-ucs
CVE-2018-0217 – A vulnerability in the CLI of the Cisco StarOS operating system for Cisco ASR 5000 Series Aggregation Services Routers could allow an authenticated, local attacker to perform a command injection attack on an affected system.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-staros
*CVE-2018-0224 – A vulnerability in the CLI of the Cisco StarOS operating system for Cisco ASR 5000 Series Aggregation Services Routers could allow an authenticated, local attacker to execute arbitrary commands with root privileges on an affected operating system. (Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-staros1
*CVE-2018-0209 – A vulnerability in the Simple Network Management Protocol (SNMP) subsystem communication channel through the Cisco 550X Series Stackable Managed Switches could allow an authenticated, remote attacker to cause the device to reload unexpectedly, causing a denial of service (DoS) condition.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-550x
CVE-2018-0223 – A vulnerability in DesktopServlet in the web-based management interface of Cisco Security Manager could allow an unauthenticated, remote attacker to conduct a reflected cross-site scripting (XSS) attack against a user of the web-based interface.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-sm
CVE-2018-0208 – A vulnerability in the web-based management interface of the (cloud based) Cisco Registered Envelope Service could allow an authenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the web-based management interface of the affected service.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-res
CVE-2018-0144 – A vulnerability in the web-based management interface of Cisco Prime Data Center Network Manager could allow an unauthenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the web-based management interface of an affected device.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-pdcnm
*CVE-2018-0141 – A vulnerability in Cisco Prime Collaboration Provisioning (PCP) Software 11.6 could allow an unauthenticated, local attacker to log in to the underlying Linux operating system.(Critical)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-cpcp
CVE-2018-0210 – A vulnerability in the web-based management interface of Cisco Data Center Network Manager could allow an unauthenticated, remote attacker to conduct a cross-site request forgery (CSRF) attack and perform arbitrary actions on an affected device.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-dcnm
Cisco Identity Services Engine (ISE)
CVE-2018-0215 – A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an unauthenticated, remote attacker to conduct a cross-site request forgery (CSRF) attack and perform arbitrary actions on an affected device.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-ise4
*CVE-2018-0213 – A vulnerability in the credential reset functionality for Cisco Identity Services Engine (ISE) could allow an authenticated, remote attacker to gain elevated privileges.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-ise2
*CVE-2018-0214 – A vulnerability in certain CLI commands of Cisco Identity Services Engine (ISE) could allow an authenticated, local attacker to execute arbitrary commands on the host operating system with the privileges of the local user, aka Command Injection.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-ise3
CVE-2018-0212 – A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an unauthenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the web-based management interface of an affected device.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-ise1
CVE-2018-0216 – A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an unauthenticated, remote attacker to conduct a cross-site request forgery (CSRF) attack and perform arbitrary actions on an affected device. (Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-ise5
* CVE-2018-0211 – A vulnerability in specific CLI commands for the Cisco Identity Services Engine could allow an authenticated, local attacker to cause a denial of service (DoS) condition.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-ise
* CVE-2018-0221 – A vulnerability in specific CLI commands for the Cisco Identity Services Engine (ISE) could allow an authenticated, local attacker to perform command injection to the underlying operating system or cause a hang or disconnect of the user session.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-ise6
Cisco Secure Access Control
CVE-2018-0207 – A vulnerability in the web-based user interface of the Cisco Secure Access Control Server prior to 5.8 patch 9 could allow an unauthenticated, remote attacker to gain read access to certain information in the affected system. (Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-acs
CVE-2018-0147 – A vulnerability in Java deserialization used by Cisco Secure Access Control System (ACS) prior to release 5.8 patch 9 could allow an unauthenticated, remote attacker to execute arbitrary commands on an affected device.(Critical)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-acs2
CVE-2018-0218 – A vulnerability in the web-based user interface of the Cisco Secure Access Control Server prior to 5.8 patch 9 could allow an unauthenticated, remote attacker to gain read access to certain information in the affected system.(Medium)
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180307-acs1