
Malware C&C server looks exposed to security vendor for a period of time. Hacker have difficulties to implant malware to workstations once malware detector install (layer 3) network backbone routing area. Sure that Hacker won’t be announced defeat then such a way disappear forever.
A smart way utilize cloud resources
We understand that cloud computing uses HTTPS by default and the data transmission over SSL. What if hacker re-engineer their malware system structure. Utilizes the cloud farm belongs to victim, storing the command-and-control (C&C) function and malicious code inside the cloud. As we know, traditional defense mechanism lack of visibility into SSL crypto setup. But It becomes a huge benefit to hacker. How worst situation you can imagine on this scenario.
How Google Docs in Google Drive re-engineer as bad guy gatekeeper.
May be you will say, it is a outdated news. The similar of cyber attack happened on 2012. But hacker never give up! They improve this technique in silent. The hacker use Google Drive as a relay. The concept is going to utilize Drive Proxy. Drive Proxy is a Windows Service that streamlines communication with Google Drive. It uses a simple protocol to communicate with client applications over a pipe. Similar idea of hack concept announced by Black Hill information security on Aug this year. They provide proof of concept to show this method is feasible.
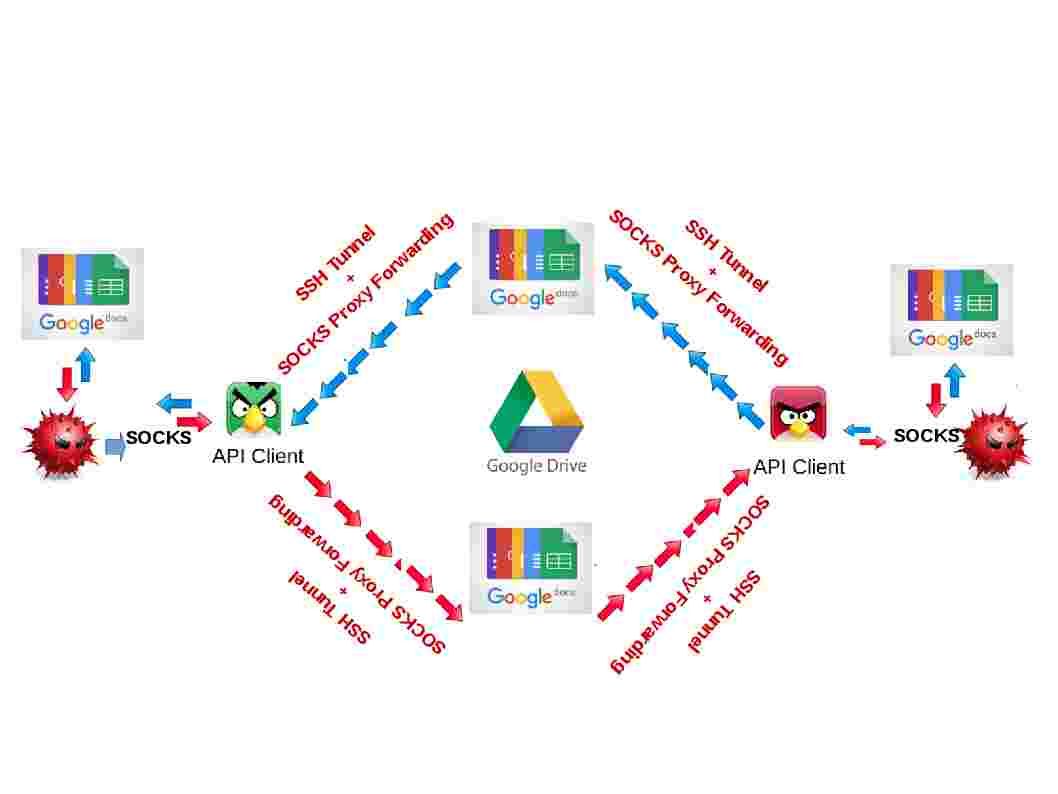
Below infographic can provide similar idea to you in this regard.
For more detail of Google Drive proxy, you need setup a Google API project in the Google Developers Console. For more details, please see below:
- Go to: https://console.developers.google.com/project
- Click on “Create Project”
- Name your project and click on “Create”
- Wait for the project to be created.
- From the left hand side menu, click on “APIs & auth”.
- From the left hand side menu, Click on “APIs”
- You will need to enable the “Drive API” by toggling the switch to “on”
- From the left hand side menu, Click on “Credentials”
- Click on “Create new Client ID”
- Select “Installed application” and click on “Configure consent screen”
- Fill in the details for your consent screen and click on “Save”.
- A new form will be presented. Select “Installed application” and “Other” then click on “Create Client ID”
- You will be presented with a Client ID and Client Secret.
- Switch to the root of the git repository and using a text editor, open ProjectConfig.txt
- You will see a line “ClientID <Your application google id here>”. Replace “<Your application google id here>” by the Client ID in the developer console.
- Example: “944352700820-eh520uo159llp750lf9jmn6srcm35r3j.apps. googleusercontent.com”.
- You will see a line “ClientSecret <Your application google secret here>”. Replace “<Your application google secret here>” by the Client Secret in the developer console.
- Example: “BfI0jTaVzBAuRo9odDmheM2Z”
- You will see a line “UpgradeCode <A GUID to identify your project here>”. Generate a GUID and replace “<A GUID to identify your project here>” with the generated GUID.
- Example: cb1ed02a-7233-4a67-a9f7-ad10a42a2082
- You will see a line “Company <Your Company name here>”. Replace “<Your Company name here>” with the company name you wish to appear in the “Add/Remove programs” window’s company column for Drive Proxy’s entry.
- Example: “Initech, Inc.”
- You will see a line “CompanyPath <Your Company here, must be a valid Windows folder name>”. The installer will install to “%programfiles%\ CompanyPath\Drive Proxy Service”. Replace “<Your Company here, must be a valid Windows folder name>” with the folder name under which you wish to group your programs.
- Example: “Initech”
- You can then open DriveProxy.sln and compile the Installer project.
Happy Thanksgiving Day

Howdy very cool site!! Guy .. Excellent .. Superb .. I’ll bookmark your web site and take the feeds additionally…I am glad to find a lot of useful information here within the publish, we want develop extra strategies in this regard, thanks for sharing.
I just want to tell you that I am just very new to blogs and certainly loved you’re page. More than likely I’m want to bookmark your website . You definitely have tremendous well written articles. Appreciate it for sharing your web page.
You are a very intelligent person!
We’re a group of volunteers and starting a new scheme in our community. Your website provided us with valuable information to work on. You’ve done an impressive job and our whole community will be thankful to you.
Helpful info. Fortunate me I discovered your website by accident, and I am surprised why this twist of fate did not took place in advance! I bookmarked it.
I have been absent for a while, but now I remember why I used to love this website. Thanks , I will try and check back more frequently. How frequently you update your site?
I have been browsing online greater than three hours lately, but I by no means found any attention-grabbing article like yours. It is pretty worth enough for me. In my view, if all website owners and bloggers made good content as you probably did, the web will be a lot more helpful than ever before.
Wow! Thank you! I continuously needed to write on my site something like that. Can I include a portion of your post to my website?
I like the helpful info you provide in your articles. I will bookmark your blog and check again here frequently. I am quite sure I will learn many new stuff right here! Good luck for the next!
Useful information. Fortunate me I discovered your web site unintentionally, and I’m surprised why this accident didn’t came about in advance! I bookmarked it.
You really make it seem so easy together with your presentation but I in finding this matter to be actually one thing that I feel I might never understand. It seems too complex and very large for me. I am taking a look forward on your next put up, I will try to get the hang of it!
Thank you, I’ve recently been searching for info approximately this topic for a long time and yours is the greatest I have came upon so far. However, what about the bottom line? Are you positive concerning the source?
Hi there, I found your blog by means of Google while looking for a similar topic, your web site got here up, it appears great. I’ve bookmarked it in my google bookmarks.
naturally like your website however you have to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I to find it very troublesome to inform the truth then again I will certainly come again again.
You really make it seem so easy with your presentation but I find this topic to be actually something which I think I would never understand. It seems too complex and very broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
of course like your web site however you have to test the spelling on quite a few of your posts. A number of them are rife with spelling problems and I in finding it very bothersome to tell the reality however I¡¦ll definitely come back again.
I’ve been absent for a while, but now I remember why I used to love this site. Thank you, I¡¦ll try and check back more frequently. How frequently you update your web site?
I¡¦ve been exploring for a little for any high quality articles or blog posts on this sort of house . Exploring in Yahoo I at last stumbled upon this website. Reading this info So i am satisfied to convey that I’ve an incredibly excellent uncanny feeling I discovered exactly what I needed. I such a lot certainly will make sure to do not omit this website and give it a look regularly.
I wanted to create you a very little remark just to say thanks a lot the moment again regarding the unique views you have discussed here. This has been really particularly open-handed of people like you to provide extensively all that numerous people could possibly have distributed for an electronic book to generate some bucks for their own end, even more so seeing that you could possibly have done it in case you desired. These smart ideas additionally served as the great way to be aware that someone else have the identical keenness just as mine to know a little more around this issue. Certainly there are some more enjoyable times ahead for many who look into your site.
Good site! I really love how it is easy on my eyes and the data are well written. I’m wondering how I could be notified whenever a new post has been made. I’ve subscribed to your RSS which must do the trick! Have a great day!
I truly appreciate this post. I¡¦ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thx again
I’m still learning from you, but I’m improving myself. I certainly liked reading everything that is posted on your blog.Keep the tips coming. I enjoyed it!
There is apparently a bunch to know about this. I believe you made certain nice points in features also.
I have been examinating out a few of your articles and i can state pretty nice stuff. I will make sure to bookmark your website.
Hello. fantastic job. I did not expect this. This is a impressive story. Thanks!
I truly appreciate this post. I¡¦ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thank you again
I carry on listening to the news speak about getting boundless online grant applications so I have been looking around for the best site to get one. Could you advise me please, where could i get some?
I have recently started a web site, the info you offer on this website has helped me tremendously. Thanks for all of your time & work.
hi!,I really like your writing very much! share we keep in touch extra about your post on AOL? I require an expert in this area to resolve my problem. May be that is you! Having a look forward to peer you.
Thank you for the sensible critique. Me & my neighbor were just preparing to do a little research about this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such great information being shared freely out there.
Wonderful work! This is the type of info that should be shared around the web. Disgrace on the search engines for now not positioning this post higher! Come on over and seek advice from my site . Thank you =)
Very nice post. I just stumbled upon your weblog and wished to say that I have truly enjoyed surfing around your blog posts. In any case I will be subscribing to your rss feed and I hope you write again soon!
you are truly a excellent webmaster. The web site loading pace is amazing. It sort of feels that you are doing any unique trick. Also, The contents are masterpiece. you’ve done a excellent process in this matter!
Hi there, I found your blog via Google at the same time as looking for a comparable matter, your site got here up, it looks great. I’ve bookmarked it in my google bookmarks.
Thank you for every other informative blog. The place else could I am getting that type of info written in such a perfect means? I have a project that I am simply now operating on, and I have been on the glance out for such info.
Thanks , I have just been searching for info about this subject for ages and yours is the greatest I have found out so far. But, what about the conclusion? Are you positive concerning the source?
I¡¦ve recently started a website, the info you provide on this website has helped me greatly. Thank you for all of your time & work.
What i do not realize is in fact how you are not actually much more smartly-favored than you may be now. You’re very intelligent. You realize thus significantly when it comes to this subject, produced me in my opinion imagine it from numerous numerous angles. Its like men and women don’t seem to be involved until it¡¦s something to accomplish with Woman gaga! Your individual stuffs great. Always maintain it up!
I was just looking for this information for a while. After six hours of continuous Googleing, finally I got it in your website. I wonder what is the lack of Google strategy that don’t rank this kind of informative web sites in top of the list. Usually the top sites are full of garbage.
Whats Going down i am new to this, I stumbled upon this I have discovered It absolutely helpful and it has aided me out loads. I am hoping to contribute & aid different users like its aided me. Great job.
Heya i am for the first time here. I came across this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you aided me.
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a bit, but instead of that, this is wonderful blog. A fantastic read. I’ll definitely be back.
I would like to thank you for the efforts you’ve put in writing this web site. I’m hoping the same high-grade website post from you in the upcoming also. In fact your creative writing skills has encouraged me to get my own site now. Really the blogging is spreading its wings quickly. Your write up is a great example of it.
Valuable information. Fortunate me I found your site by chance, and I’m shocked why this twist of fate didn’t took place in advance! I bookmarked it.
Hi my friend! I wish to say that this post is amazing, nice written and come with approximately all important infos. I would like to look more posts like this .
Hello, i think that i saw you visited my weblog thus i came to “return the favor”.I’m attempting to find things to enhance my website!I suppose its ok to use a few of your ideas!!
Very nice post. I just stumbled upon your blog and wanted to say that I’ve truly enjoyed surfing around your blog posts. In any case I’ll be subscribing to your feed and I hope you write again soon!
I like what you guys are up also. Such clever work and reporting! Keep up the superb works guys I¡¦ve incorporated you guys to my blogroll. I think it’ll improve the value of my website 🙂
Excellent web site. Lots of useful information here. I am sending it to a few buddies ans additionally sharing in delicious. And obviously, thanks for your sweat!
Great ¡V I should certainly pronounce, impressed with your website. I had no trouble navigating through all tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, site theme . a tones way for your customer to communicate. Excellent task..
I haven¡¦t checked in here for some time as I thought it was getting boring, but the last several posts are good quality so I guess I will add you back to my daily bloglist. You deserve it my friend 🙂
It is in reality a nice and helpful piece of info. I am glad that you simply shared this useful info with us. Please stay us up to date like this. Thanks for sharing.
Hello.This article was really remarkable, especially since I was looking for thoughts on this topic last week.
Very good written article. It will be useful to everyone who utilizes it, as well as me. Keep doing what you are doing – for sure i will check out more posts.
Thank you for every other informative website. Where else may I get that type of information written in such a perfect manner? I’ve a venture that I am just now operating on, and I’ve been on the glance out for such info.
Thank you for some other great article. The place else could anybody get that type of information in such a perfect approach of writing? I have a presentation subsequent week, and I am at the look for such information.
I like the valuable info you provide in your articles. I’ll bookmark your weblog and check again here frequently. I’m quite certain I’ll learn many new stuff right here! Good luck for the next!
I have been surfing online more than 3 hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. Personally, if all web owners and bloggers made good content as you did, the net will be a lot more useful than ever before.
Hiya, I’m really glad I have found this info. Nowadays bloggers publish just about gossips and internet and this is really irritating. A good site with exciting content, this is what I need. Thank you for keeping this web-site, I will be visiting it. Do you do newsletters? Cant find it.
You made several fine points there. I did a search on the theme and found mainly people will have the same opinion with your blog.
Good article and straight to the point. I don’t know if this is really the best place to ask but do you guys have any ideea where to hire some professional writers? Thank you 🙂
Whats Taking place i’m new to this, I stumbled upon this I have found It positively helpful and it has helped me out loads. I hope to give a contribution & help different users like its aided me. Good job.
I carry on listening to the news broadcast talk about receiving free online grant applications so I have been looking around for the top site to get one. Could you tell me please, where could i acquire some?
I¡¦ve learn a few good stuff here. Certainly value bookmarking for revisiting. I surprise how a lot effort you put to create such a great informative website.
I¡¦ve learn several excellent stuff here. Certainly worth bookmarking for revisiting. I surprise how much effort you place to make any such excellent informative website.
Thanks for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our local library but I think I learned more from this post. I’m very glad to see such wonderful info being shared freely out there.
Hello.This article was really remarkable, especially because I was investigating for thoughts on this topic last couple of days.
Hello my family member! I wish to say that this article is amazing, nice written and come with approximately all vital infos. I¡¦d like to peer more posts like this .
Good ¡V I should definitely pronounce, impressed with your website. I had no trouble navigating through all tabs as well as related information ended up being truly simple to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, site theme . a tones way for your client to communicate. Nice task..
whoah this weblog is fantastic i like studying your articles. Keep up the great work! You know, many individuals are looking around for this information, you could help them greatly.
I like the helpful info you provide in your articles. I will bookmark your blog and check again here frequently. I’m quite certain I will learn many new stuff right here! Good luck for the next!
I precisely had to say thanks once more. I do not know the things that I might have sorted out in the absence of those aspects shared by you over my situation. Previously it was a depressing difficulty in my circumstances, however , noticing a well-written way you processed the issue forced me to leap over fulfillment. Extremely grateful for the guidance and as well , believe you recognize what an amazing job you have been putting in educating others by way of your blog post. Probably you have never met any of us.
Hey, you used to write wonderful, but the last several posts have been kinda boring¡K I miss your super writings. Past few posts are just a little out of track! come on!
I like what you guys are up also. Such smart work and reporting! Keep up the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my web site 🙂
I merely have to share it with you that I am new to posting and clearly adored your write-up. Probably I am going to bookmark your blog post . You simply have superb article information. Acknowledge it for giving out with us your web information
I have been surfing online more than 3 hours today, yet I by no means found any attention-grabbing article like yours. It¡¦s lovely worth sufficient for me. In my view, if all webmasters and bloggers made good content as you probably did, the net can be a lot more helpful than ever before.
Exceedingly intriguing points that you have stated, thanks so much for submitting.
Good day there, just became receptive to your blogging site through Search engine, and have found that it is truly educational. I’ll take pleasure in if you decide to carry on this approach.
It happens to be convenient occasion to construct some options for the near future. I’ve read through this blog entry and if I can, I wish to suggest to you you couple intriguing instruction.
I’m extremely pleased to uncover this website. I need to to thank you for ones time just for this fantastic read!! I definitely savored every bit of it and i also have you book marked to look at new things in your website.
I conceive you have observed some very interesting details , thankyou for the post.
you’re in point of fact a excellent webmaster. The web site loading velocity is amazing. It sort of feels that you’re doing any unique trick. Also, The contents are masterpiece. you have done a wonderful job in this topic!
magnificent issues altogether, you just received a emblem new reader. What may you recommend about your submit that you just made some days ago? Any positive?
Hi my loved one! I want to say that this article is amazing, nice written and come with almost all vital infos. I would like to see extra posts like this .
As I web site possessor I believe the content material here is rattling wonderful , appreciate it for your hard work. You should keep it up forever! Best of luck.
Hello. remarkable job. I did not expect this. This is a great story. Thanks!
Thanks a lot for giving everyone an exceptionally pleasant possiblity to read critical reviews from here. It is always very excellent plus packed with a lot of fun for me personally and my office friends to search your website a minimum of 3 times weekly to study the new stuff you have. Not to mention, I am just at all times contented with the staggering tricks you serve. Selected 4 facts in this article are without a doubt the most impressive I have had.
I will right away snatch your rss as I can not to find your email subscription hyperlink or e-newsletter service. Do you’ve any? Please permit me recognise so that I could subscribe. Thanks.
Generally I don’t read post on blogs, however I wish to say that this write-up very compelled me to check out and do so! Your writing taste has been amazed me. Thank you, quite great article.
Great write-up, I am normal visitor of one¡¦s website, maintain up the nice operate, and It’s going to be a regular visitor for a lengthy time.
I truly appreciate this post. I’ve been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thx again!
hi!,I really like your writing so a lot! percentage we keep in touch more about your article on AOL? I require an expert in this space to solve my problem. Maybe that is you! Having a look ahead to peer you.
What i do not realize is in fact how you are no longer really a lot more well-favored than you might be now. You are so intelligent. You recognize thus considerably relating to this topic, made me individually believe it from numerous various angles. Its like women and men are not involved unless it¡¦s something to accomplish with Lady gaga! Your own stuffs great. Always handle it up!
Definitely, what a splendid site and educative posts, I will bookmark your site.Have an awsome day!
Heya i’m for the first time here. I came across this board and I find It really useful & it helped me out a lot. I hope to give something back and help others like you aided me.
Great post. I was checking constantly this blog and I’m impressed! Extremely useful info specifically the last part 🙂 I care for such info a lot. I was seeking this particular information for a long time. Thank you and good luck.
Hello my loved one! I want to say that this article is amazing, nice written and include almost all vital infos. I’d like to see extra posts like this.
I am genuinely delighted to read this blog posts which contains tons of helpful information, thanks for providing these data.|
I really appreciate this post. I’ve been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thx again!
Hi my loved one! I want to say that this post is awesome, great written and come with approximately all vital infos. I¡¦d like to see extra posts like this .
Generally I do not learn post on blogs, but I would like to say that this write-up very forced me to take a look at and do so! Your writing style has been surprised me. Thank you, very nice article.
I will immediately snatch your rss feed as I can not find your email subscription link or e-newsletter service. Do you have any? Please allow me understand in order that I may subscribe. Thanks.
Generally I don’t learn article on blogs, but I would like to say that this write-up very compelled me to check out and do so! Your writing taste has been amazed me. Thanks, quite great post.
I’ll immediately clutch your rss as I can not find your email subscription link or newsletter service. Do you have any? Kindly let me recognise so that I may just subscribe. Thanks.
Hi my family member! I wish to say that this post is awesome, great written and come with approximately all vital infos. I’d like to see more posts like this.
Hello my loved one! I want to say that this post is awesome, nice written and come with approximately all important infos. I¡¦d like to look extra posts like this .
You made some good points there. I looked on the internet for the subject matter and found most people will approve with your site.
Wow! This could be one particular of the most beneficial blogs We have ever arrive across on this subject. Actually Excellent. I am also a specialist in this topic so I can understand your hard work.
What i do not understood is in fact how you are not really much more well-favored than you may be right now. You’re so intelligent. You know therefore considerably on the subject of this matter, produced me for my part consider it from a lot of varied angles. Its like men and women don’t seem to be fascinated until it is one thing to accomplish with Girl gaga! Your personal stuffs great. At all times take care of it up!
Terrific work! This is the type of info that should be shared around the internet. Shame on Google for no longer positioning this put up upper! Come on over and discuss with my site . Thanks =)
Wow, marvelous blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is excellent, let alone the content!
Great amazing issues here. I¡¦m very glad to see your post. Thanks so much and i’m looking ahead to contact you. Will you please drop me a e-mail?
I have been exploring for a little bit for any high quality articles or weblog posts on this sort of area . Exploring in Yahoo I eventually stumbled upon this website. Reading this info So i am satisfied to show that I have a very excellent uncanny feeling I found out just what I needed. I such a lot for sure will make sure to don¡¦t disregard this site and provides it a look regularly.
Good web site! I really love how it is simple on my eyes and the data are well written. I’m wondering how I could be notified when a new post has been made. I’ve subscribed to your feed which must do the trick! Have a nice day!
I¡¦ll immediately snatch your rss as I can not in finding your e-mail subscription hyperlink or newsletter service. Do you’ve any? Please allow me recognise so that I may subscribe. Thanks.
Hello there, I discovered your blog via Google whilst searching for a comparable topic, your web site got here up, it appears good. I have bookmarked it in my google bookmarks.
I would like to thank you for the efforts you’ve put in writing this site. I’m hoping the same high-grade blog post from you in the upcoming as well. In fact your creative writing skills has inspired me to get my own website now. Really the blogging is spreading its wings fast. Your write up is a great example of it.
I will right away snatch your rss feed as I can’t to find your e-mail subscription hyperlink or newsletter service. Do you’ve any? Kindly permit me recognize in order that I could subscribe. Thanks.
Just wanna input that you have a very decent site, I the style and design it really stands out.
Appreciate it for helping out, fantastic information.
Bonjour ! Ahahaha sympa comme site!
Bonjour ! Ou se trouve le flux Rss que je puisse le suivre ?
Hello, you used to write magnificent, but the last several posts have been kinda boring¡K I miss your great writings. Past few posts are just a little out of track! come on!
I enjoy looking through an article that can make people
think. Also, many thanks for allowing me to comment!
Your style is very unique compared to other people I’ve read
stuff from. Thanks for posting when you’ve got the opportunity,
Guess I will just bookmark this web site.
Hi there, just became alert to your blog through Google, and found that it’s truly informative. I am going to watch out for brussels. I will appreciate if you continue this in future. Lots of people will be benefited from your writing. Cheers!
Unquestionably consider that which you said. Your favorite justification seemed to be on the web
the easiest thing to take into account of. I say to you, I certainly get annoyed whilst people think about worries
that they just do not recognise about. You managed to hit the nail upon the top and outlined out the whole thing without having side
effect , people can take a signal. Will likely be back
to get more. Thanks
Just wanna remark that you have a very decent web site , I the pattern it actually stands out.
Great write-up, I¡¦m regular visitor of one¡¦s blog, maintain up the nice operate, and It is going to be a regular visitor for a long time.
hi!,I like your writing very a lot! percentage we communicate more approximately your article on AOL? I need a specialist in this space to unravel my problem. Maybe that is you! Having a look forward to look you.
I don’t even know how I ended up here, but I thought this post was good. I don’t know who you are but certainly you are going to a famous blogger if you are not already 😉 Cheers!
As a Newbie, I am always searching online for articles that can be of assistance to me. Thank you
Hiya, I am really glad I’ve found this information. Nowadays bloggers publish just about gossips and web and this is really irritating. A good blog with interesting content, this is what I need. Thank you for keeping this web-site, I’ll be visiting it. Do you do newsletters? Can’t find it.
excellent points altogether, you simply received a new reader. What could you recommend in regards to your submit that you made some days ago? Any certain?
I was excited to uncover this web site. I need to to thank you for ones time for this particularly fantastic read!! I definitely savored every part of it and i also have you book-marked to see new information on your web site.
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how could we communicate?
I like what you guys are up too. Such clever work and reporting! Keep up the excellent works guys I’ve incorporated you guys to my blogroll. I think it will improve the value of my web site :).
Good ¡V I should certainly pronounce, impressed with your web site. I had no trouble navigating through all tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or something, website theme . a tones way for your client to communicate. Excellent task..
I am continually looking online for posts that can facilitate me. Thank you!
I simply could not depart your website prior to suggesting that I extremely loved the usual info an individual provide for your visitors? Is gonna be again ceaselessly to inspect new posts
It is in reality a nice and useful piece of info. I’m satisfied that you just shared this useful info with us. Please stay us informed like this. Thanks for sharing.
Hey, you used to write wonderful, but the last few posts have been kinda boring… I miss your tremendous writings. Past several posts are just a little out of track! come on!
I think other site proprietors should take this web site as an model, very clean and magnificent user friendly style and design, as well as the content. You are an expert in this topic!
Fantastic site. Plenty of helpful information here. I’m sending it to a few buddies ans also sharing in delicious. And of course, thank you for your effort!
Hi there, just became alert to your blog through Google, and found that it’s really informative. I am going to watch out for brussels. I’ll appreciate if you continue this in future. Numerous people will be benefited from your writing. Cheers!
I would like to thnkx for the efforts you’ve put in writing this site. I am hoping the same high-grade site post from you in the upcoming as well. In fact your creative writing skills has encouraged me to get my own website now. Really the blogging is spreading its wings rapidly. Your write up is a great example of it.
I in addition to my guys appeared to be looking at the great procedures on your site and suddenly developed an awful suspicion I never expressed respect to the web blog owner for those tips. All the men are already stimulated to read through them and have in effect in reality been taking pleasure in these things. Thank you for indeed being quite considerate and for going for this sort of important themes most people are really needing to be informed on. Our honest apologies for not expressing appreciation to earlier.
Great awesome things here. I¡¦m very glad to look your article. Thanks a lot and i am looking forward to touch you. Will you please drop me a mail?
I’m very pleased to uncover this great site. I want to to thank you for ones time for this particularly wonderful read!! I definitely enjoyed every bit of it and i also have you bookmarked to look at new stuff in your website.
I merely wish to notify you that I am new to blogging and totally valued your information. Quite possibly I am going to remember your blog post . You indeed have impressive article materials. Love it for telling with us the best domain page
It is usually perfect time to put together some preparations for the possible future. I’ve browsed this posting and if I have the ability to, I wish to suggest you very few great tips.
Might be nearly unattainable to see well-updated individual on this area, regrettably you seem like you are familiar with which you’re writing about! Thank You
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I get in fact enjoyed account your blog posts. Anyway I’ll be subscribing to your augment and even I achievement you access consistently quickly.
It truly is mostly not possible to come across well-updated people on this area, in addition you appear like you know the things that you’re talking about! Thanks A Lot
Unbelievably alluring elements you have said, a big heads up for posting.
I just want to tell you that I am new to blogging and certainly adored your page. Probably I am most likely to save your blog post . You undoubtedly have fantastic article materials. Admire it for giving out with us all of your url page
My brother suggested I might like this website. He was entirely right. This post truly made my day. You can not imagine simply how much time I had spent for this info! Thanks!
Wow, wonderful blog structure! How long have you ever been blogging for? you made running a blog look easy. The whole look of your web site is wonderful, let alone the content material!
Wonderful beat ! I would like to apprentice while you amend your web site, how can i subscribe for a blog web site? The account helped me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear concept
Wonderful work! That is the type of info that are supposed to be shared across the internet. Shame on the search engines for not positioning this post upper! Come on over and visit my web site . Thank you =)
naturally like your web site however you have to check the spelling on quite a few of your posts. A number of them are rife with spelling issues and I in finding it very bothersome to inform the truth however I will certainly come again again.
I get pleasure from, lead to I discovered exactly what I was taking a look for. You’ve ended my four day long hunt! God Bless you man. Have a nice day. Bye
Where is a good place start a website for business at a very low price?
Muchos Gracias for your blog.Much thanks again. Keep writing.
Bonjour ! Ca été pris ou le sujet ? Ca me rappelle quelque chose ce site !
I want to show some appreciation to you just for rescuing me from such a trouble. After researching through the world wide web and seeing tricks which are not productive, I assumed my life was well over. Living without the solutions to the problems you have resolved by way of your review is a crucial case, and the kind that might have in a wrong way affected my career if I had not come across the blog. Your actual knowledge and kindness in controlling all the details was useful. I am not sure what I would’ve done if I had not come upon such a solution like this. It’s possible to now look forward to my future. Thank you so much for the reliable and effective help. I won’t think twice to propose your web site to anybody who needs to have guidelines on this issue.
I just want to inform you you that I am new to writing a blog and totally admired your post. Most likely I am prone to remember your blog post . You definitely have fantastic article material. Be Thankful For it for share-out with us your main internet site page
It is right occasion to make some preparations for the foreseeable future. I’ve digested this document and if I may just, I want to encourage you some significant recommendations.
I’m very happy to uncover this web site. I want to to thank you for ones time for this particularly wonderful read!! I definitely really liked every part of it and I have you saved as a favorite to check out new stuff on your blog.
It’s nearly not possible to come across well-aware parties on this matter, however you seem like you understand the things you’re posting on! Gratitude
Extraordinarily enlightening knowledge you’ll have stated, thank you for publishing.
It is actually nearly close to impossible to see well-qualified visitors on this matter, however, you appear like you are familiar with the things that you’re writing about! Many Thanks
It is ideal day to make some schemes for the extended term. I’ve browsed this blog entry and if I could, I want to encourage you couple worthwhile tips and advice.
I’m very happy to discover this page. I need to to thank you for ones time due to this wonderful read!! I definitely enjoyed every bit of it and i also have you saved to fav to check out new things in your web site.
I merely intend to inform you you that I am new to blogging and utterly valued your write-up. Likely I am most likely to remember your blog post . You seriously have lovely article content. Delight In it for discussing with us your very own site article
I was extremely pleased to find this web site. I want to to thank you for ones time for this particularly fantastic read!! I definitely enjoyed every part of it and I have you saved to fav to look at new information on your blog.
It’s perfect time to make some plans for the future and it is time to be happy. I’ve read this post and if I could I want to suggest you few interesting things or suggestions. Perhaps you can write next articles referring to this article. I desire to read more things about it!
I think other website proprietors should take this website as an model, very clean and excellent user genial style and design, as well as the content. You’re an expert in this topic!
I simply desire to notify you that I am new to posting and really valued your site. Very likely I am inclined to bookmark your blog post . You indeed have fantastic article material. Love it for sharing with us your main internet document
I was suggested this blog by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my trouble. You are wonderful! Thanks!
Thank you a lot for providing individuals with such a spectacular opportunity to check tips from here. It’s usually very cool and also full of amusement for me and my office friends to search your website a minimum of thrice weekly to find out the new things you will have. And indeed, I am also certainly contented considering the gorgeous concepts you serve. Selected 1 facts on this page are surely the most efficient I’ve had.
This is very interesting, You are a very skilled blogger. I’ve joined your feed and look forward to seeking more of your great post. Also, I have shared your website in my social networks!
Thank you, I have just been searching for information approximately this topic for ages and yours is the greatest I’ve found out till now. However, what about the bottom line? Are you sure concerning the source?
I merely want to advise you that I am new to posting and undeniably cherished your work. Likely I am probably to remember your blog post . You undoubtedly have stunning article material. Get Pleasure From it for share-out with us your current internet site information
I was excited to find this website. I want to to thank you for ones time just for this wonderful read!! I definitely savored every part of it and I have you saved to fav to check out new stuff in your site.
Keep functioning ,impressive job!
As I site possessor I believe the content matter here is rattling excellent , appreciate it for your efforts. You should keep it up forever! Good Luck.
Very well written information. It will be supportive to anybody who utilizes it, including myself. Keep doing what you are doing – looking forward to more posts.
Thanks pertaining to discussing the following superb written content on your site. I ran into it on the search engines. I will check back again if you publish extra aricles.
Hey There. I found your blog using msn. This is a really well written article. I’ll be sure to bookmark it and come back to read more of your useful information. Thanks for the post. I will certainly return.
Thank you ever so for you blog article.Really looking forward to read more. Really Great.
I simply hope to reveal to you that I am new to wordpress blogging and extremely enjoyed your page. Probably I am likely to store your blog post . You definitely have great article information. Delight In it for discussing with us your own blog article
Great article! We will be linking to this great content on our site.
Keep up the great writing.
Every weekend i used to go to see this website, as i want enjoyment,
since this this site conations really pleasant funny stuff
too.
I was wondering if you ever considered changing the layout of your site?
Its very well written; I love what youve got
to say. But maybe you could a little more in the way
of content so people could connect with it better.
Youve got an awful lot of text for only having 1
or 2 images. Maybe you could space it out better?
Thank you for the good writeup. It in fact was a amusement account it.
Look advanced to more added agreeable from you! By the way, how can we communicate?
Thank you for the good writeup. It in fact was a amusement account it.
Look advanced to more added agreeable from you! By the way, how
can we communicate?
Hello! This is kind of off topic but I need some help
from an established blog. Is it tough to set up your own blog?
I’m not very techincal but I can figure things out pretty fast.
I’m thinking about setting up my own but I’m not sure
where to begin. Do you have any ideas or suggestions?
Many thanks
Woah! I’m really enjoying the template/theme of this blog.
It’s simple, yet effective. A lot of times it’s
tough to get that “perfect balance” between user friendliness and visual appeal.
I must say you have done a excellent job with this.
Additionally, the blog loads super fast for me on Opera.
Excellent Blog!
Merely wanna input on few general things, The website design and style is perfect, the subject matter is very fantastic. “Good judgment comes from experience, and experience comes from bad judgment.” by Barry LePatner.
Very nice info and straight to the point. I am not sure if this is really the best place to ask but do you guys have any thoughts on where to get some professional writers? Thanks in advance 🙂
You can definitely see your enthusiasm within the work you write. The world hopes for more passionate writers such as you who are not afraid to say how they believe. All the time follow your heart.
Hello, i believe that i noticed you visited my website so i came to
return the favor?.I am trying to find issues to enhance my site!I assume
its ok to use some of your ideas!!
You could definitely see your skills within the work you write. The world hopes for more passionate writers such as you who are not afraid to say how they believe. Always go after your heart.
Keep functioning ,fantastic job!
You actually make it seem so easy with your presentation but I find this matter to be actually something which I think I would never understand. It seems too complicated and extremely broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
Thank you for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our area library but I think I learned more from this post. I’m very glad to see such magnificent information being shared freely out there.
I keep listening to the news update talk about receiving free online grant applications so I have been looking around for the best site to get one. Could you advise me please, where could i find some?
Some genuinely good posts on this web site, regards for contribution. “There is one universal gesture that has one universal message–a smile” by Valerie Sokolosky.
This is really interesting, You are a very skilled
blogger. I have joined your feed and look forward to seeking more
of your magnificent post. Also, I’ve shared your site in my social networks!
I don’t even know the way I ended up here, but I assumed this post was good.
I don’t understand who you might be however
certainly you are going to a famous blogger should you aren’t already.
Cheers!
I really like your blog.. very nice colors & theme. Did you design this website yourself or did you
hire someone to do it for you? Plz respond as I’m looking to design my own blog and would like to find out where u got this from.
many thanks
Thanks to my father who stated to me concerning this weblog,
this webpage is actually amazing.
I precisely needed to thank you very much again. I’m not certain what I would have gone through without the entire advice shared by you regarding this problem. It had been a very intimidating condition in my position, nevertheless viewing a specialized tactic you resolved that took me to leap over fulfillment. I am just happier for your help and thus hope you realize what a powerful job you’re providing educating other individuals via your webpage. I’m certain you haven’t got to know any of us.
Hi, Neat post. There is an issue along with your website in web explorer, might check this¡K IE nonetheless is the marketplace chief and a huge portion of other folks will pass over your magnificent writing because of this problem.
Thanks for every other informative website. The place else may just I get that kind of info written in such a perfect method? I have a challenge that I am just now operating on, and I have been on the look out for such info.
I genuinely enjoy looking at on this website , it contains fantastic blog posts. “The longing to produce great inspirations didn’t produce anything but more longing.” by Sophie Kerr.
This is very interesting, You are a very skilled blogger. I’ve joined your feed and look forward to seeking more of your wonderful post. Also, I have shared your site in my social networks!
Hi there very cool web site!! Man .. Beautiful .. Superb .. I will bookmark your website and take the feeds also¡KI’m glad to find numerous helpful information here in the submit, we need work out extra strategies in this regard, thank you for sharing. . . . . .
I intended to draft you this bit of note just to say thank you over again for all the spectacular information you have featured at this time. This is certainly remarkably generous of people like you to give unreservedly all most people could have marketed as an e-book in order to make some dough for their own end, particularly considering that you could possibly have done it in the event you desired. Those basics in addition worked like the great way to realize that many people have a similar passion just like my own to grasp a little more on the topic of this issue. I’m sure there are numerous more enjoyable occasions in the future for individuals who read carefully your website.
I am very happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this greatest doc.
Thanks so much for providing individuals with remarkably memorable chance to read critical reviews from here. It is usually so brilliant and jam-packed with a lot of fun for me personally and my office peers to search your site more than three times a week to read the newest guides you will have. And indeed, we are certainly impressed for the gorgeous guidelines you give. Certain 1 tips in this post are absolutely the very best I have ever had.
Wow, wonderful blog structure! How long have you been blogging for? you make running a blog glance easy. The total look of your website is fantastic, as neatly as the content material!
Wow! This could be one particular of the most helpful blogs We’ve ever arrive across on this subject. Basically Magnificent. I’m also an expert in this topic so I can understand your effort.
Enjoyed reading through this, very good stuff, thankyou . “The fox knows many things, but the hedgehog knows one big thing.” by Archilocus.
As a Newbie, I am permanently searching online for articles that can benefit me. Thank you
I intended to compose you that tiny note just to give many thanks over again with the marvelous guidelines you’ve featured on this site. It was simply tremendously open-handed with you giving openly exactly what most of us would’ve offered as an electronic book to earn some dough for their own end, primarily considering that you could have done it in case you decided. These advice likewise worked to be a good way to be aware that some people have similar dream like my very own to know a little more around this condition. I am certain there are several more pleasant opportunities in the future for folks who view your website.
You are my inhalation , I own few blogs and very sporadically run out from to post .
Hiya very nice website!! Man .. Beautiful .. Amazing .. I’ll bookmark your website and take the feeds also…I am happy to search out numerous useful info right here within the put up, we want develop more techniques in this regard, thanks for sharing.
Simply desire to say your article is as astonishing. The clarity in your post is just great and i could assume you are an expert on this subject. Fine with your permission allow me to grab your feed to keep updated with forthcoming post. Thanks a million and please carry on the enjoyable work.
I really like your writing style, excellent information, thanks for posting :D. “If a cluttered desk is the sign of a cluttered mind, what is the significance of a clean desk” by Laurence J. Peter.
you’re in point of fact a excellent webmaster. The site loading speed is incredible. It kind of feels that you are doing any distinctive trick. Moreover, The contents are masterwork. you’ve performed a fantastic process in this subject!
You completed a few fine points there. I did a search on the subject and found nearly all folks will have the same opinion with your blog.
I think other website proprietors should take this web site as an model, very clean and fantastic user friendly style and design, let alone the content. You are an expert in this topic!
certainly like your web site however you have to check the spelling on several of your posts. A number of them are rife with spelling issues and I in finding it very troublesome to inform the reality then again I will certainly come back again.
Wow! This can be one particular of the most useful blogs We have ever arrive across on this subject. Actually Fantastic. I am also an expert in this topic so I can understand your hard work.
I was suggested this blog by my cousin. I’m not sure whether this post is written by him as no one else know such detailed about my trouble. You’re amazing! Thanks!
whoah this weblog is excellent i love reading your articles. Stay up the great work! You already know, a lot of persons are hunting round for this information, you can help them greatly.
hey there and thank you for your info – I’ve certainly
picked up something new from right here. I did however expertise a
few technical points using this website, as I experienced to reload the website a lot of times previous to I could get it to load properly.
I had been wondering if your web hosting is OK? Not that I’m complaining,
but slow loading instances times will often affect your placement in google and can damage your high-quality score if advertising and marketing
with Adwords. Well I’m adding this RSS to my e-mail and can look out for a lot more of your respective exciting
content. Make sure you update this again very soon.
As soon as I noticed this website I went on reddit to share some of the love with them.
Attractive section of content. I just stumbled upon your blog and in accession capital to assert that
I acquire actually enjoyed account your blog posts. Any
way I will be subscribing to your augment
and even I achievement you access consistently rapidly.
Valuable info. Fortunate me I discovered your website unintentionally, and I am shocked why this coincidence didn’t took place in advance! I bookmarked it.
magnificent issues altogether, you simply won a brand new reader. What might you recommend in regards to your put up that you just made some days in the past? Any certain?
Great post. I was checking constantly this blog and I am impressed! Very useful info specifically the last part 🙂 I care for such information a lot. I was seeking this certain information for a long time. Thank you and good luck.
If you wish for to grow your knowledge only keep visiting this site
and be updated with the most up-to-date gossip posted
here.
Only wanna tell that this is very beneficial , Thanks for taking your time to write this.
I am really impressed with your writing skills as well as with the layout on your blog. Is this a paid theme or did you modify it yourself? Anyway keep up the nice quality writing, it is rare to see a great blog like this one these days..
continuously i used to read smaller content which also clear their motive, and that is also
happening with this post which I am reading now.
I really like your writing style, good information, regards for putting up :D. “Faith is a continuation of reason.” by William Adams.
Wow! Thank you! I constantly needed to write on my site something like that. Can I take a part of your post to my site?
I together with my friends were taking note of the great points located on your web blog and immediately I got an awful suspicion I never thanked the web site owner for them. Those ladies became totally glad to read through all of them and have now really been taking advantage of those things. Thank you for actually being really kind and then for making a decision on these kinds of beneficial guides millions of individuals are really wanting to be aware of. Our sincere apologies for not saying thanks to earlier.
I actually wanted to develop a simple note in order to thank you for all the awesome guides you are giving out on this website. My extended internet lookup has at the end of the day been compensated with excellent facts and strategies to write about with my companions. I would point out that many of us website visitors are unquestionably endowed to be in a great network with very many wonderful professionals with valuable points. I feel rather grateful to have used your entire webpages and look forward to tons of more fun minutes reading here. Thanks a lot once more for everything.
You made a few good points there. I did a search on the issue and found nearly all folks will consent with your blog.
Attractive section of content. I just stumbled upon your site and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently fast.
Wow, awesome blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is magnificent, as well as the content!
Thank you a lot for sharing this with all of us you actually realize what you’re speaking approximately! Bookmarked. Please additionally discuss with my site =). We may have a link exchange agreement between us!
I’m not sure where you are getting your info, but good topic. I needs to spend some time learning much more or understanding more. Thanks for fantastic information I was looking for this information for my mission.
I don’t even know how I ended up here, but I thought this post was good. I don’t know who you are but definitely you are going to a famous blogger if you are not already 😉 Cheers!
What i do not understood is in reality how you’re not really much more well-preferred than you may be now. You are so intelligent. You understand thus considerably relating to this subject, made me in my view believe it from a lot of varied angles. Its like women and men are not interested unless it¡¦s something to do with Woman gaga! Your personal stuffs nice. Always maintain it up!
Excellent blog here! Also your site loads up very fast! What web host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as fast as yours lol
Thank you for helping out, good information. “The four stages of man are infancy, childhood, adolescence, and obsolescence.” by Bruce Barton.
Hello my friend! I want to say that this article is awesome, great written and come with approximately all vital infos. I would like to see extra posts like this.
Magnificent site. Plenty of helpful info here. I am sending it to some pals ans also sharing in delicious. And naturally, thanks in your sweat!
Someone essentially lend a hand to make seriously posts I’d state. This is the very first time I frequented your web page and to this point? I surprised with the research you made to make this actual post amazing. Great activity!
Hello, Neat post. There is an issue with your web site in internet explorer, would check this… IE still is the marketplace leader and a large component of other people will omit your wonderful writing because of this problem.
I simply had to thank you so much yet again. I am not sure the things I would’ve made to happen in the absence of these creative ideas revealed by you regarding this field. Certainly was a frustrating crisis for me, nevertheless finding out a specialised style you treated the issue took me to leap over contentment. Now i am grateful for your advice and trust you know what a powerful job you are always doing training the mediocre ones through the use of a site. I know that you’ve never got to know any of us.
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Any way I’ll be subscribing to your augment and even I achievement you access consistently rapidly.
Simply desire to say your article is as astonishing. The clearness in your post is just cool and i can assume you are an expert on this subject. Fine with your permission let me to grab your feed to keep up to date with forthcoming post. Thanks a million and please carry on the enjoyable work.
I wanted to put you one little observation in order to say thanks over again about the superb pointers you have shared on this site. It’s simply tremendously generous of you to grant without restraint precisely what most people could possibly have made available as an ebook to end up making some dough for their own end, and in particular now that you might well have tried it if you wanted. The creative ideas in addition worked as a fantastic way to be aware that many people have the identical desire just as my own to learn more around this matter. I’m sure there are lots of more enjoyable situations ahead for individuals who view your blog.
I do accept as true with all the ideas you’ve offered on your post. They are very convincing and will certainly work. Nonetheless, the posts are very quick for newbies. Could you please lengthen them a bit from next time? Thanks for the post.
It¡¦s actually a cool and helpful piece of info. I¡¦m glad that you just shared this helpful info with us. Please keep us up to date like this. Thank you for sharing.
fantastic put up, very informative. I’m wondering why the opposite experts of this sector do not understand this. You should continue your writing. I’m sure, you have a great readers’ base already!
excellent issues altogether, you simply received a brand new reader. What could you recommend in regards to your publish that you made some days in the past? Any positive?
I wanted to send a simple remark so as to express gratitude to you for these remarkable hints you are giving out on this website. My particularly long internet investigation has at the end been rewarded with really good information to share with my two friends. I ‘d tell you that we readers actually are unequivocally endowed to be in a fabulous community with so many awesome professionals with useful basics. I feel extremely blessed to have encountered your web pages and look forward to many more exciting moments reading here. Thanks again for all the details.
Thanks for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such fantastic information being shared freely out there.
It¡¦s actually a great and useful piece of information. I¡¦m happy that you simply shared this helpful information with us. Please stay us informed like this. Thank you for sharing.
Wow! This could be one particular of the most helpful blogs We’ve ever arrive across on this subject. Actually Fantastic. I am also a specialist in this topic therefore I can understand your hard work.
Hello, Neat post. There is an issue along with your site in web explorer, could check this… IE still is the market chief and a large element of folks will leave out your fantastic writing due to this problem.
I believe you have remarked some very interesting details , regards for the post.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! However, how can we communicate?
I do agree with all the ideas you have offered for your post. They are very convincing and will definitely work. Nonetheless, the posts are very quick for beginners. May you please extend them a bit from next time? Thank you for the post.
of course like your website however you need to check the spelling on quite a few of your posts. Many of them are rife with spelling issues and I in finding it very bothersome to tell the truth on the other hand I’ll definitely come again again.
Unquestionably believe that which you said. Your favorite reason seemed to be on the net the simplest thing to be aware of. I say to you, I certainly get irked while people consider worries that they just do not know about. You managed to hit the nail upon the top as well as defined out the whole thing without having side-effects , people can take a signal. Will probably be back to get more. Thanks
I dugg some of you post as I thought they were handy very useful
I read this piece of writing fully about the difference
of hottest and previous technologies, it’s amazing article.
I think other web-site proprietors should take this web site as an model, very clean and excellent user genial style and design, as well as the content. You are an expert in this topic!
I’ve been surfing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. In my opinion, if all web owners and bloggers made good content as you did, the web will be a lot more useful than ever before.
Fantastic website. A lot of helpful information here. I¡¦m sending it to several buddies ans also sharing in delicious. And obviously, thanks for your effort!
I do not even know how I ended up here, but I thought this post was great. I don’t know who you are but definitely you’re going to a famous blogger if you aren’t already 😉 Cheers!
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you aided me.
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you could do with a few pics to drive the message home a little bit, but instead of that, this is great blog. A great read. I’ll definitely be back.
Wow, amazing blog structure! How long have you been running a blog for? you make running a blog look easy. The total look of your site is excellent, let alone the content!
naturally like your website but you have to check the spelling on several of your posts. Several of them are rife with spelling problems and I find it very troublesome to tell the truth nevertheless I¡¦ll surely come back again.
I just could not go away your website before suggesting that I actually enjoyed the usual info an individual supply on your guests? Is gonna be again ceaselessly in order to check out new posts.
Unquestionably believe that which you said. Your favorite reason appeared to be on the net the easiest thing to be aware of. I say to you, I definitely get irked while people think about worries that they just don’t know about. You managed to hit the nail upon the top and defined out the whole thing without having side-effects , people can take a signal. Will probably be back to get more. Thanks
Hello there, You have done an excellent job. I will certainly digg it and personally suggest to my friends. I am sure they’ll be benefited from this website.
Thanks, I have recently been searching for info about this subject for a long time and yours is the best I have came upon till now. But, what concerning the conclusion? Are you sure concerning the source?
I have recently started a blog, the info you provide on this website has helped me tremendously. Thank you for all of your time & work.
I simply desired to thank you very much once again. I do not know the things that I would’ve carried out in the absence of those pointers provided by you about such theme. It absolutely was an absolute intimidating crisis in my position, nevertheless coming across this professional manner you treated the issue forced me to leap with contentment. I am happy for this guidance as well as pray you are aware of a great job you are accomplishing educating men and women thru your website. Most probably you’ve never got to know any of us.
Keep working ,remarkable job!
I’m writing to make you know of the remarkable discovery my wife’s princess experienced reading yuor web blog. She even learned a good number of things, including how it is like to have an amazing helping spirit to have other individuals with ease master several problematic things. You really exceeded people’s expected results. I appreciate you for providing the interesting, trusted, informative not to mention cool thoughts on your topic to Evelyn.
I do not even know how I ended up here, but I thought this post was good. I don’t know who you are but definitely you’re going to a famous blogger if you aren’t already 😉 Cheers!
You have observed very interesting details ! ps nice site. “Wisdom is the supreme part of happiness.” by Sophocles.
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get got an edginess over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly a lot often inside case you shield this hike.
Simply wanna input on few general things, The website layout is perfect, the subject material is very wonderful. “I delight in men over seventy. They always offer one the devotion of a lifetime.” by Oscar Fingall O’Flahertie Wills Wilde.
I’ve recently started a blog, the info you provide on this website has helped me greatly. Thanks for all of your time & work. “A creative man is motivated by the desire to achieve, not by the desire to beat others.” by Ayn Rand.
magnificent points altogether, you just received a brand new reader. What might you suggest in regards to your post that you just made some days ago? Any certain?
Merely wanna input on few general things, The website pattern is perfect, the content material is really wonderful. “Good judgment comes from experience, and experience comes from bad judgment.” by Barry LePatner.
I enjoy, cause I discovered just what I was taking a look for. You’ve ended my four day long hunt! God Bless you man. Have a great day. Bye
Only wanna remark on few general things, The website pattern is perfect, the written content is real good : D.
I have been surfing on-line greater than three hours nowadays, but I never discovered any interesting article like yours. It is pretty value sufficient for me. In my view, if all webmasters and bloggers made excellent content as you probably did, the web will be a lot more useful than ever before.
My wife and i ended up being quite thankful Michael managed to finish up his inquiry via the precious recommendations he was given in your site. It’s not at all simplistic just to be giving out concepts which often others have been trying to sell. And we also acknowledge we’ve got the blog owner to thank for this. Those illustrations you made, the easy blog navigation, the friendships you can aid to promote – it is everything powerful, and it’s really making our son in addition to the family imagine that that subject matter is exciting, which is certainly wonderfully mandatory. Thanks for all!
Great ¡V I should definitely pronounce, impressed with your site. I had no trouble navigating through all the tabs as well as related information ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or anything, site theme . a tones way for your customer to communicate. Excellent task..
Excellent post. I was checking continuously this blog and I’m impressed! Extremely helpful info particularly the last part 🙂 I care for such information a lot. I was seeking this certain information for a long time. Thank you and good luck.
Hey There. I found your blog using msn. This is a really well written article. I will make sure to bookmark it and come back to read more of your useful information. Thanks for the post. I’ll definitely comeback.
You really make it appear so easy along with your presentation however I to find this topic to be actually one thing which I think I’d never understand. It seems too complex and very wide for me. I am taking a look forward on your subsequent publish, I will attempt to get the hang of it!
I have recently started a website, the information you provide on this web site has helped me tremendously. Thanks for all of your time & work.
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get got an shakiness over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly a lot often inside case you shield this increase.
Thank you for sharing superb informations. Your site is very cool. I am impressed by the details that you¡¦ve on this website. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found just the information I already searched all over the place and just could not come across. What a great site.
you’re really a just right webmaster. The site loading speed is incredible. It seems that you’re doing any unique trick. In addition, The contents are masterpiece. you have performed a great process in this subject!
I really like your writing style, wonderful information, regards for posting : D.
Thank you for sharing excellent informations. Your web-site is very cool. I’m impressed by the details that you have on this website. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for extra articles. You, my friend, ROCK! I found just the information I already searched all over the place and simply could not come across. What a great website.
Hi my friend! I want to say that this article is awesome, nice written and include almost all vital infos. I would like to see more posts like this.
Wow! This could be one particular of the most helpful blogs We’ve ever arrive across on this subject. Basically Wonderful. I am also a specialist in this topic so I can understand your effort.
I wish to show thanks to the writer for bailing me out of this type of trouble. After checking through the world-wide-web and getting recommendations which are not productive, I believed my life was over. Existing devoid of the answers to the difficulties you’ve solved as a result of your good write-up is a crucial case, as well as the kind which could have negatively affected my entire career if I had not noticed the blog. Your good understanding and kindness in handling every item was excellent. I’m not sure what I would’ve done if I hadn’t encountered such a thing like this. I am able to now relish my future. Thanks a lot so much for your reliable and results-oriented guide. I won’t think twice to recommend the sites to any person who requires assistance on this subject matter.
I am not sure where you are getting your information, but good topic. I needs to spend some time learning much more or understanding more. Thanks for excellent info I was looking for this info for my mission.
I have learn a few excellent stuff here. Definitely price bookmarking for revisiting. I wonder how a lot attempt you place to make this kind of great informative site.
excellent points altogether, you just gained a new reader. What would you suggest about your submit that you made some days ago? Any positive?
HelloHi there, simplyjust turned intobecamewasbecomechanged into aware ofalert to your blogweblog thruthroughvia Google, and foundand located that it isit’s reallytruly informative. I’mI am gonnagoing to watch outbe careful for brussels. I willI’ll appreciatebe grateful if youshould youwhen youin the event youin case youfor those whoif you happen to continueproceed this in future. A lot ofLots ofManyNumerous other folksfolksother peoplepeople will beshall bemight bewill probably becan bewill likely be benefited from yourout of your writing. Cheers!
Great post. I was checking continuously this blog and I’m impressed! Very helpful information specially the last part 🙂 I care for such information much. I was seeking this particular info for a very long time. Thank you and good luck.
I am extremely impressed with your writing skills and also with the layout on your weblog. Is this a paid theme or did you customize it yourself? Either way keep up the excellent quality writing, it’s rare to see a nice blog like this one these days..
Wow! This can be one particular of the most beneficial blogs We’ve ever arrive across on this subject. Actually Wonderful. I am also an expert in this topic so I can understand your effort.
Usually I do not learn article on blogs, but I would like to say that this write-up very pressured me to try and do it! Your writing taste has been surprised me. Thanks, quite great article.
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our area library but I think I learned more from this post. I’m very glad to see such magnificent info being shared freely out there.
Hiya, I am really glad I’ve found this information. Nowadays bloggers publish only about gossips and net and this is actually irritating. A good web site with exciting content, this is what I need. Thank you for keeping this web site, I will be visiting it. Do you do newsletters? Cant find it.
I haven’t checked in here for some time because I thought it was getting boring, but the last few posts are great quality so I guess I’ll add you back to my daily bloglist. You deserve it my friend 🙂
Thanks for any other fantastic post. The place else may anybody get that type of info in such a perfect method of writing? I’ve a presentation next week, and I am at the look for such information.
Only wanna remark on few general things, The website style and design is perfect, the subject material is really wonderful. “War is much too serious a matter to be entrusted to the military.” by Georges Clemenceau.
I will immediately clutch your rss feed as I can’t in finding your e-mail subscription link or e-newsletter service. Do you’ve any? Kindly let me know so that I could subscribe. Thanks.
you are actually a excellent webmaster. The site loading velocity is incredible. It kind of feels that you’re doing any distinctive trick. Moreover, The contents are masterwork. you’ve done a fantastic task on this subject!
of course like your web site but you have to take a look at the spelling on quite a few of your posts. Many of them are rife with spelling problems and I find it very bothersome to inform the truth on the other hand I will definitely come again again.
I have been browsing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. Personally, if all webmasters and bloggers made good content as you did, the internet will be much more useful than ever before.
As soon as I detected this website I went on reddit to share some of the love with them.
It is appropriate time to make some plans for the future and it’s time to be happy. I have read this post and if I could I wish to suggest you some interesting things or tips. Maybe you could write next articles referring to this article. I wish to read even more things about it!
It¡¦s really a cool and useful piece of information. I¡¦m satisfied that you shared this helpful information with us. Please stay us up to date like this. Thank you for sharing.
Simply wish to say your article is as astounding. The clearness in your post is simply nice and i could assume you’re an expert on this subject. Well with your permission allow me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the gratifying work.
Great awesome issues here. I am very happy to look your article. Thanks so much and i am looking forward to touch you. Will you please drop me a mail?
Hi my loved one! I want to say that this post is amazing, great written and come with almost all important infos. I’d like to look more posts like this.
I am writing to make you be aware of what a excellent discovery my wife’s child undergone browsing your web page. She figured out numerous pieces, which included what it’s like to have an ideal helping heart to get many people completely thoroughly grasp specific problematic subject areas. You truly exceeded my expectations. Many thanks for distributing the useful, dependable, explanatory and as well as fun guidance on that topic to Emily.
Keep on workingthis going pleaseon writing, great job!
I really like your writing style, good info , thanks for putting up : D.
I¡¦ll right away take hold of your rss as I can not to find your email subscription hyperlink or newsletter service. Do you’ve any? Please allow me recognize in order that I may subscribe. Thanks.
Hi there very cool blog!! Guy .. Excellent .. Amazing .. I’ll bookmark your blog and take the feeds additionally¡KI’m glad to seek out so many helpful information here in the submit, we want develop more techniques on this regard, thanks for sharing. . . . . .
Hello There. I found your blog using msn. This is a really well written article. I will make sure to bookmark it and come back to read more of your useful information. Thanks for the post. I will definitely return.
Great goods from you, man. I have understand your stuff previous to and you are just extremely fantastic. I actually like what you have acquired here, really like what you’re stating and the way in which you say it. You make it enjoyable and you still take care of to keep it smart. I can not wait to read far more from you. This is actually a tremendous site.
Perfectly composed written content , thanks for information .
Very interesting info !Perfect just what I was searching for! “If you want to test your memory, try to recall what you were worrying about one year ago today.” by Rotarian.
It is actually a nice and helpful piece of information. I’m glad that you just shared this useful information with us. Please stay us informed like this. Thanks for sharing.
I like this post, enjoyed this one regards for posting. “The goal of revival is conformity to the image of Christ, not imitation of animals.” by Richard F. Lovelace.
Some really superb content on this web site, regards for contribution. “A religious awakening which does not awaken the sleeper to love has roused him in vain.” by Jessamyn West.
Thanks for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our area library but I think I learned more clear from this post. I’m very glad to see such great info being shared freely out there.
I wanted to jot down a small comment so as to express gratitude to you for the splendid ways you are showing at this website. My extensive internet look up has now been paid with pleasant suggestions to talk about with my two friends. I ‘d believe that many of us website visitors actually are undeniably blessed to live in a wonderful place with so many outstanding professionals with insightful techniques. I feel quite privileged to have seen your weblog and look forward to really more enjoyable moments reading here. Thanks a lot again for all the details.
whoah this blog is wonderful i love reading your posts. Stay up the good work! You realize, many individuals are searching round for this info, you can help them greatly.
Nice read, I just passed this onto a friend who was doing a little research on that. And he actually bought me lunch since I found it for him smile Thus let me rephrase that: Thanks for lunch!
magnificent submit, very informative. I’m wondering why the other specialists of this sector don’t understand this. You must continue your writing. I’m confident, you’ve a great readers’ base already!
Fantastic beat ! I would like to apprentice while you amend your web site, how can i subscribe for a blog site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear idea
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how could we communicate?
Undeniably believe that which you said. Your favorite justification seemed to be on the web the simplest thing to be aware of. I say to you, I certainly get annoyed while people think about worries that they just don’t know about. You managed to hit the nail upon the top and also defined out the whole thing without having side effect , people could take a signal. Will likely be back to get more. Thanks
I think other website proprietors should take this site as an model, very clean and fantastic user genial style and design, let alone the content. You’re an expert in this topic!
Of course, what a fantastic website and informative posts, I surely will bookmark your website.Best Regards!
Thanks for some other wonderful post. Where else may anyone get that type of information in such an ideal means of writing? I’ve a presentation next week, and I’m on the search for such info.
I want to express appreciation to the writer just for bailing me out of this situation. As a result of searching throughout the online world and getting ideas that were not productive, I figured my entire life was well over. Being alive minus the approaches to the problems you’ve resolved as a result of this posting is a serious case, and the ones that might have badly damaged my entire career if I hadn’t discovered the website. Your own natural talent and kindness in playing with all things was useful. I don’t know what I would’ve done if I hadn’t come across such a step like this. It’s possible to now look forward to my future. Thanks for your time so much for this reliable and effective help. I will not hesitate to refer your web page to any individual who would need guidance about this subject.
I have been checking out many of your articles and i can claim pretty good stuff. I will surely bookmark your blog.
HiWhat’s upHi thereHello, after reading this awesomeremarkableamazing articlepostpiece of writingparagraph i am alsotooas well happygladcheerfuldelighted to share my experienceknowledgefamiliarityknow-how here with friendsmatescolleagues.
But wanna input on few general things, The website style is perfect, the subject matter is very wonderful. “The idea of God is the sole wrong for which I cannot forgive mankind.” by Marquis de Sade.
howdy, exalted blog on fatlike loss. akin helped.
Bonjour ! Il n’y a pas de flux RSS ici ?
I really appreciate this post. I¡¦ve been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thank you again
I don’t even know how I ended up here, but I thought this post was good. I don’t know who you are but certainly you are going to a famous blogger if you are not already 😉 Cheers!
Good day very cool web site!! Guy .. Beautiful .. Wonderful .. I will bookmark your website and take the feeds also¡KI am satisfied to find so many helpful information here within the put up, we want develop extra strategies in this regard, thank you for sharing. . . . . .
Hello there, You’ve done an excellent job. I’ll certainly digg it and personally recommend to my friends. I am confident they will be benefited from this site.
Hi, i think that i saw you visited my site so i came to “return the favor”.I’m trying to find things to improve my website!I suppose its ok to use some of your ideas!!
There is clearly a lot to know about this. I assume you made various good points in features also.
hello there and thank you for your information – I have certainly picked up something new from right here. I did however expertise a few technical issues using this web site, as I experienced to reload the web site lots of times previous to I could get it to load properly. I had been wondering if your web host is OK? Not that I’m complaining, but sluggish loading instances times will very frequently affect your placement in google and can damage your quality score if ads and marketing with Adwords. Well I’m adding this RSS to my e-mail and could look out for much more of your respective interesting content. Make sure you update this again very soon..
Valuable info. Lucky me I discovered your website accidentally, and I am stunned why this coincidence did not happened in advance! I bookmarked it.
Hello there I am so excited I found your blog, I really
found you by mistake, while I was looking on Bing for something else, Anyways I am here now and would
just like to say cheers for a remarkable post and a all round
entertaining blog (I also love the theme/design), I don’t have time to read through it all at the
moment but I have book-marked it and also added in your RSS feeds, so when I
have time I will be back to read more, Please do keep up the fantastic work.
Undeniably believe that which you stated. Your favorite reason appeared to be on the internet the easiest thing to be aware of. I say to you, I certainly get annoyed while people consider worries that they plainly do not know about. You managed to hit the nail upon the top and also defined out the whole thing without having side effect , people can take a signal. Will probably be back to get more. Thanks
Hello my family member! I want to say that this post is awesome, great written and include approximately all significant infos. I¡¦d like to see more posts like this .
Hey there, You’ve done a great job. I will definitely digg it and personally recommend to my friends. I am confident they will be benefited from this web site.
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thank you again
We are a group of volunteers and opening a new scheme in our community. Your web site provided us with valuable information to work on. You have done an impressive job and our whole community will be thankful to you.
Nice read, I just passed this onto a colleague who was doing a little research on that. And he actually bought me lunch as I found it for him smile Thus let me rephrase that: Thanks for lunch! “To be 70 years young is sometimes far more cheerful and hopeful than to be 40 years old.” by Oliver Wendell Holmes.
This is really interesting, You’re a very skilled blogger. I have joined your feed and look forward to seeking more of your magnificent post. Also, I have shared your website in my social networks!
Good write-up, I’m regular visitor of one’s web site, maintain up the nice operate, and It’s going to be a regular visitor for a lengthy time.
Hello There. I found your blog using msn. This is a really well written article. I’ll be sure to bookmark it and return to read more of your useful information. Thanks for the post. I’ll definitely comeback.
magnificent issues altogether, you just won a emblem new reader. What would you recommend about your publish that you just made some days in the past? Any positive?
Somebody necessarily assist to make significantly posts I would state. This is the first time I frequented your website page and so far? I amazed with the research you made to make this actual post amazing. Fantastic job!
What i don’t understood is in fact how you are now not really a lot more neatly-favored than you might be right now. You’re so intelligent. You understand thus considerably with regards to this topic, produced me in my opinion imagine it from so many various angles. Its like men and women aren’t fascinated except it¡¦s something to do with Woman gaga! Your individual stuffs nice. All the time take care of it up!
This is very interesting, You’re a very skilled blogger. I have joined your feed and look forward to seeking more of your magnificent post. Also, I have shared your site in my social networks!
Bonjour ! Cool j’ai bien aimé ! Merci pour cette lecture tiptop
Well I sincerely enjoyed reading it. This information procured by you is very helpful for accurate planning.
Hello.This article was extremely fascinating, particularly because I was looking for thoughts on this topic last Sunday.
I am so happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that’s at the other blogs. Appreciate your sharing this greatest doc.
Heya i’m for the first time here. I came across this board and I find It truly useful & it helped me out a lot. I hope to give something back and help others like you aided me.
Nice post. I was checking constantly this blog and I’m impressed! Very helpful information particularly the last part 🙂 I care for such info a lot. I was seeking this certain info for a long time. Thank you and best of luck.
My spouse and i have been satisfied that Raymond could carry out his studies by way of the precious recommendations he had from your very own blog. It’s not at all simplistic to just happen to be making a gift of guidance which often other people may have been making money from. And now we remember we need the blog owner to thank because of that. Those explanations you have made, the easy website navigation, the friendships your site help instill – it’s all sensational, and it’s really aiding our son and the family reckon that that issue is exciting, which is certainly especially vital. Thanks for the whole lot!
Wonderful beat ! I wish to apprentice while you amend your website, how can i subscribe for a blog site? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear idea
whoah this weblog is wonderful i love reading your articles. Keep up the good paintings! You recognize, a lot of persons are hunting round for this info, you could help them greatly.
My wife and i felt very thrilled Michael managed to finish up his basic research using the precious recommendations he acquired out of your site. It is now and again perplexing to simply continually be offering tips and hints that many others could have been trying to sell. And we all know we’ve got the website owner to be grateful to for that. Those explanations you made, the easy website menu, the friendships your site assist to promote – it is all spectacular, and it’s really assisting our son and us consider that that subject matter is cool, which is certainly highly fundamental. Thanks for all!
You are a very intelligent individual!
Hello there, You’ve done a fantastic job. I’ll certainly digg it and personally suggest to my friends. I am sure they’ll be benefited from this web site.
You really make it appear really easy with your presentation but I in finding this matter to be really something that I feel I’d by no means understand. It sort of feels too complicated and extremely huge for me. I’m looking ahead on your subsequent put up, I will attempt to get the cling of it!
Awsome post and right to the point. I don’t know if this is actually the best place to ask but do you people have any thoughts on where to get some professional writers? Thank you 🙂
Hi there, You have done a great job. I will definitely digg it and personally suggest to my friends. I am sure they’ll be benefited from this site.
It’s remarkable to visit this web site and reading
the views of all colleagues regarding this paragraph, while I am also zealous of getting know-how.
Wonderful article! That is the kind of information that are meant to be shared
across the net. Shame on the search engines for not positioning this put up
higher! Come on over and discuss with my site . Thank you =)
I would like to thnkx for the efforts you’ve put in writing this site. I am hoping the same high-grade web site post from you in the upcoming also. In fact your creative writing abilities has encouraged me to get my own site now. Really the blogging is spreading its wings rapidly. Your write up is a great example of it.
I have recently started a website, the information you provide on this website has helped me greatly. Thanks for all of your time & work.
I went over this website and I conceive you have a lot of superb info, saved to favorites (:.
Hmm is anyone else encountering problems with the images on this blog loading?
I’m trying to find out if its a problem on my end
or if it’s the blog. Any responses would be greatly appreciated.
Super-Duper blog! I am loving it!! Will come back again. I am taking your feeds also
Good write-up, I’m normal visitor of one’s blog, maintain up the nice operate, and It’s going to be a regular visitor for a lengthy time.
Genuinely enlightening information that you have said, warm regards for setting up.
It is actually near not possible to come across well-educated people on this theme, yet somehow you look like you are familiar with those things you’re posting on! Gratitude
I have been browsing online more than 3 hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all web owners and bloggers made good content as you did, the web will be a lot more useful than ever before.
I really like your writing style, fantastic information, thanks for posting : D.
Enjoyed looking through this, very good stuff, appreciate it. “It is in justice that the ordering of society is centered.” by Aristotle.
Usually I do not read post on blogs, but I would like to say that this write-up very compelled me to try and do it! Your writing style has been surprised me. Thanks, quite nice article.
It’s mostly extremely difficult to come across well-advised viewers on this area, in addition you appear like you understand exactly what you’re indicating! Regards
Pretty entertaining information that you have remarked, thanks a lot for adding.
Thank you for sharing excellent informations. Your website is so cool. I’m impressed by the details that you’ve on this blog. It reveals how nicely you understand this subject. Bookmarked this web page, will come back for more articles. You, my pal, ROCK! I found simply the information I already searched all over the place and just could not come across. What an ideal web-site.
I simply desire to tell you that I am new to blog posting and completely liked your post. Probably I am likely to bookmark your blog post . You truly have excellent article information. Truly Appreciate it for swapping with us your very own website post
Very efficiently written story. It will be beneficial to anybody who utilizes it, as well as me. Keep up the good work – looking forward to more posts.
It really is near impossible to encounter well-informed men and women on this niche, in addition you come across as like you fully grasp those things you’re indicating! Cheers
Excellent post. I was checking continuously this blog and I’m impressed! Very useful info specially the last part 🙂 I care for such information a lot. I was seeking this certain info for a long time. Thank you and best of luck.
Noticeably compelling points you have stated, thanks a lot for writing.
It is actually mostly unthinkable to encounter well-qualified readers on this issue, nonetheless you look like you fully understand those things you’re posting on! Regards
Heya i’m for the first time here. I came across this board and I find It really useful & it helped me out much. I hope to give something back and help others like you helped me.
It is actually almost unattainable to encounter well-advised users on this content, still you look like you are familiar with which you’re raving about! Excellent
Hi, Neat post. There’s an issue with your site in internet explorer, would test this¡K IE nonetheless is the marketplace chief and a huge component to people will miss your wonderful writing because of this problem.
I really appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again!
I simply wanted to thank you so much again. I do not know what I might have created without the type of tricks shown by you concerning such a area. This has been the troublesome difficulty in my opinion, nevertheless taking note of your expert fashion you treated the issue forced me to jump for fulfillment. Extremely thankful for your guidance as well as hope that you recognize what an amazing job you are always getting into teaching men and women through the use of your webpage. I know that you haven’t encountered any of us.
I just intend to show you that I am new to writing and undeniably enjoyed your webpage. Very possible I am going to remember your blog post . You really have great article content. Acknowledge it for giving out with us your own domain article
It really is mostly extremely difficult to come across well-informed parties on this matter, however you come across as like you comprehend those things you’re talking about! Cheers
Absolute stimulating data that you have mentioned, thanks so much for posting.
Thanks for sharing excellent informations. Your site is so cool. I am impressed by the details that you¡¦ve on this web site. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for extra articles. You, my pal, ROCK! I found just the information I already searched everywhere and simply could not come across. What an ideal web site.
It’s mostly extremely difficult to find well-educated readers on this issue, then again you seem like you fully understand the things you’re revealing! Appreciate It
I gotta bookmark this internet site it seems very useful invaluable
You could certainly see your enthusiasm within the paintings you write. The world hopes for even more passionate writers like you who aren’t afraid to mention how they believe. Always go after your heart.
Exceedingly enlightening suggestions you have remarked, thank you so much for putting up.
Incredibly helpful points you’ll have stated, many thanks for putting up.
I really like your writing style, superb information, thankyou for posting : D.
It is actually mostly close to impossible to come across well-updated users on this matter, yet somehow you look like you fully understand which you’re preaching about! Thanks
It truly is practically unattainable to find well-advised individuals on this subject, still you come across as like you understand what exactly you’re indicating! Bless You
I and my friends were taking note of the good ideas from your website and so suddenly came up with an awful feeling I had not thanked the web blog owner for those tips. All the young boys were definitely for that reason glad to learn all of them and already have in reality been enjoying those things. Thanks for genuinely well kind and then for going for varieties of terrific subjects most people are really needing to learn about. Our own sincere regret for not expressing appreciation to you sooner.
I merely hope to advise you that I am new to blogging and really valued your post. Most likely I am going to save your blog post . You undoubtedly have impressive article material. Love it for giving out with us your very own website document
It’s truly a great and helpful piece of information. I am glad that you simply shared this useful information with us. Please keep us informed like this. Thanks for sharing.
I have learn several good stuff here. Certainly value bookmarking for revisiting. I wonder how a lot attempt you set to make any such great informative web site.
I precisely had to thank you very much once again. I am not sure what I could possibly have used without the suggestions discussed by you relating to such a area of interest. It was actually a troublesome case in my view, but spending time with this professional strategy you resolved that made me to cry over contentment. Extremely happy for this service and thus have high hopes you find out what a powerful job that you’re accomplishing teaching many others using your webblog. Most probably you’ve never got to know all of us.
Incredibly insightful specifics you’ll have stated, warm regards for adding.
I was suggested this web site by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my trouble. You are incredible! Thanks!
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish only about gossips and net and this is actually frustrating. A good web site with exciting content, this is what I need. Thank you for keeping this web site, I will be visiting it. Do you do newsletters? Can’t find it.
Hello there, just became alert to your blog through Google, and found that it’s really informative. I am gonna watch out for brussels. I’ll be grateful if you continue this in future. A lot of people will be benefited from your writing. Cheers!
Hey very nice website!! Guy .. Beautiful .. Amazing .. I’ll bookmark your web site and take the feeds also¡KI am happy to seek out numerous helpful information right here in the submit, we want work out more strategies in this regard, thanks for sharing. . . . . .
I like the valuable information you provide in your articles. I’ll bookmark your weblog and check again here regularly. I’m quite certain I’ll learn many new stuff right here! Good luck for the next!
Needed to send you one very small word just to thank you as before for these fantastic solutions you’ve shared above. It’s certainly unbelievably open-handed of you to allow unhampered all that a lot of people would’ve sold for an e book in making some bucks for their own end, specifically considering that you might well have tried it if you ever considered necessary. The ideas in addition acted to become fantastic way to be certain that someone else have the same zeal just as my own to learn a lot more regarding this matter. I’m certain there are millions of more pleasurable times ahead for folks who discover your site.
You actually make it seem so easy with your presentation but I find this matter to be really something that I think I would never understand. It seems too complicated and extremely broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
Hello There. I found your blog using msn. This is a very well written article. I will make sure to bookmark it and come back to read more of your useful information. Thanks for the post. I will certainly comeback.
Hiya, I’m really glad I have found this information. Today bloggers publish just about gossips and internet and this is actually annoying. A good site with exciting content, this is what I need. Thanks for keeping this website, I will be visiting it. Do you do newsletters? Can not find it.
I’m very happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this greatest doc.
Good ¡V I should definitely pronounce, impressed with your site. I had no trouble navigating through all the tabs as well as related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or something, website theme . a tones way for your customer to communicate. Nice task..
You are my inhalation , I have few web logs and rarely run out from to post .
A lot of thanks for your own work on this web site. Betty takes pleasure in making time for research and it’s easy to understand why. Most people learn all about the powerful medium you produce both useful and interesting information on the web blog and even inspire participation from other ones on this area of interest then our princess is always understanding a lot. Enjoy the rest of the new year. You are conducting a very good job.
Hello there! Do you know if they make any plugins to assist with Search Engine Optimization? I’m trying to get my blog to rank for some targeted keywords but I’m not seeing very good success. If you know of any please share. Thank you!
I really appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thx again!
Good website! I truly love how it is easy on my eyes and the data are well written. I am wondering how I might be notified when a new post has been made. I have subscribed to your feed which must do the trick! Have a nice day!
Thank you for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our local library but I think I learned more from this post. I am very glad to see such fantastic information being shared freely out there.
Thanks for your whole hard work on this site. My daughter takes pleasure in setting aside time for investigation and it is obvious why. My spouse and i know all of the powerful form you create simple guides by means of this web site and encourage participation from some other people on the matter so our child is really becoming educated a great deal. Take pleasure in the rest of the new year. You’re doing a remarkable job.
Hello, you used to write fantastic, but the last several posts have been kinda boring… I miss your tremendous writings. Past few posts are just a bit out of track! come on!
Good site! I really love how it is simple on my eyes and the data are well written. I’m wondering how I might be notified whenever a new post has been made. I have subscribed to your feed which must do the trick! Have a great day!
You can certainly see your expertise in the work you write. The arena hopes for even more passionate writers such as you who aren’t afraid to say how they believe. All the time go after your heart.
you are actually a good webmaster. The web site loading speed is incredible. It seems that you are doing any distinctive trick. Moreover, The contents are masterpiece. you’ve done a magnificent process on this topic!
I like this web blog very much, Its a rattling nice spot to read and find info . “A fair exterior is a silent recommendation.” by Publilius Syrus.
Rattling nice style and design and superb articles , absolutely nothing else we want : D.
You are my aspiration , I own few web logs and infrequently run out from to brand.I conceive this website contains some rattling great info for everyone. “He who has not looked on Sorrow will never see Joy.” by Kahlil Gibran.
I in addition to my guys ended up examining the good techniques on your site and then instantly got an awful suspicion I never expressed respect to the blog owner for those tips. All of the boys ended up certainly glad to read through them and have seriously been taking pleasure in these things. I appreciate you for simply being so thoughtful and also for settling on varieties of wonderful things most people are really desperate to discover. My personal honest regret for not saying thanks to earlier.
Magnificent goods from you, man. I have understand your stuff previous to and you are just too magnificent. I really like what you have acquired here, certainly like what you’re stating and the way in which you say it. You make it entertaining and you still care for to keep it sensible. I can not wait to read far more from you. This is really a wonderful web site.
Very interesting information!Perfect just what I was looking for!
Usually I don’t learn article on blogs, however I wish to say that this write-up very pressured me to check out and do so! Your writing taste has been amazed me. Thank you, quite great article.
Whats Going down i am new to this, I stumbled upon this I have discovered It absolutely helpful and it has aided me out loads. I’m hoping to contribute & help other customers like its helped me. Great job.
Hello my loved one! I wish to say that this post is awesome, nice written and come with approximately all important infos. I would like to peer extra posts like this .
I got what you mean , regards for putting up.Woh I am thankful to find this website through google. “Do not be too timid and squeamish about your actions. All life is an experiment.” by Ralph Waldo Emerson.
you are really a good webmaster. The website loading pace is incredible. It sort of feels that you’re doing any unique trick. Also, The contents are masterpiece. you’ve performed a excellent task on this matter!
What i do not understood is in fact how you are not actually a lot more well-favored than you may be right now. You’re very intelligent. You know thus considerably in the case of this matter, made me in my view believe it from so many numerous angles. Its like men and women don’t seem to be fascinated except it’s something to do with Woman gaga! Your own stuffs excellent. Always handle it up!
Thanks a lot for sharing this with all folks you really realize what you’re speaking approximately! Bookmarked. Kindly additionally discuss with my website =). We can have a hyperlink change contract between us!
I together with my friends happened to be looking through the nice secrets and techniques located on your web site and so instantly came up with a horrible feeling I had not thanked the web site owner for those strategies. All of the women happened to be consequently joyful to study all of them and have now unquestionably been making the most of those things. Many thanks for genuinely considerably kind and then for going for such superb themes millions of individuals are really eager to be aware of. My very own honest regret for not expressing gratitude to you sooner.
Thank you a lot for providing individuals with remarkably special possiblity to read articles and blog posts from this website. It is always so pleasant plus stuffed with a great time for me and my office fellow workers to visit your blog particularly 3 times a week to find out the fresh secrets you have got. And of course, I’m also certainly contented with all the unique creative concepts you give. Some two areas in this article are in truth the most impressive we’ve ever had.
I just could not go away your web site before suggesting that I really enjoyed the usual information a person provide in your guests? Is going to be back often in order to check up on new posts.
Only a smiling visitor here to share the love (:, btw outstanding layout.
Thankyou for helping out, great information.
Very interesting information!Perfect just what I was looking for! “To be without some of the things you want is an indispensable part of happiness.” by Bertrand Russell.
I have been exploring for a little bit for any high-quality articles or blog posts on this kind of area . Exploring in Yahoo I eventually stumbled upon this site. Studying this information So i¡¦m glad to express that I’ve an incredibly just right uncanny feeling I came upon just what I needed. I most indubitably will make sure to do not put out of your mind this web site and provides it a look regularly.
I was just looking for this information for a while. After 6 hours of continuous Googleing, finally I got it in your website. I wonder what’s the lack of Google strategy that don’t rank this type of informative web sites in top of the list. Generally the top websites are full of garbage.
I cling on to listening to the news lecture about receiving boundless online grant applications so I have been looking around for the most excellent site to get one. Could you advise me please, where could i find some?
I think other website proprietors should take this web site as an model, very clean and magnificent user friendly style and design, let alone the content. You’re an expert in this topic!
Valuable information. Lucky me I found your site by accident, and I’m stunned why this twist of fate didn’t came about in advance! I bookmarked it.
Wow! This can be one particular of the most beneficial blogs We have ever arrive across on this subject. Basically Magnificent. I’m also a specialist in this topic therefore I can understand your effort.
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get bought an edginess over that you wish be delivering the following. unwell unquestionably come further formerly again as exactly the same nearly very often inside case you shield this increase.
Admiring the dedication you put into your website and in depth information you offer. It’s awesome to come across a blog every once in a while that isn’t the same out of date rehashed information. Great read! I’ve saved your site and I’m adding your RSS feeds to my Google account.
This is very interesting, You’re a very skilled blogger. I have joined your rss feed and look forward to seeking more of your fantastic post. Also, I have shared your website in my social networks!
I’ve been absent for a while, but now I remember why I used to love this website. Thanks , I will try and check back more often. How frequently you update your web site?
Hello.This post was really remarkable, especially since I was investigating for thoughts on this subject last Friday.
I would like to thnkx for the efforts you have put in writing this blog. I’m hoping the same high-grade blog post from you in the upcoming as well. Actually your creative writing skills has encouraged me to get my own site now. Really the blogging is spreading its wings fast. Your write up is a good example of it.
Very interesting details you have observed , thanks for posting . “My work is a game, a very serious game.” by M. C. Escher.
I went over this web site and I believe you have a lot of wonderful information, saved to bookmarks (:.
Wow! This could be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Magnificent. I am also an expert in this topic so I can understand your effort.
A person necessarily assist to make critically posts I would state. That is the first time I frequented your web page and so far? I amazed with the analysis you made to create this actual submit extraordinary. Great process!
Very efficiently written post. It will be supportive to everyone who utilizes it, including myself. Keep up the good work – can’r wait to read more posts.
We’re a group of volunteers and starting a new scheme in our community. Your web site provided us with valuable info to work on. You’ve done a formidable job and our entire community will be thankful to you.
I am continually browsing online for ideas that can help me. Thanks!
I simply desired to thank you very much all over again. I do not know the things I would’ve taken care of in the absence of the actual thoughts contributed by you on my situation. This was an absolute depressing scenario in my circumstances, but taking a look at a new expert way you treated that took me to weep with gladness. Now i am happier for the work and wish you really know what an amazing job that you’re undertaking instructing some other people via your web site. Most probably you haven’t come across any of us.
Hi my family member! I want to say that this post is awesome, nice written and include almost all vital infos. I would like to see extra posts like this .
I have been reading out a few of your articles and i can claim nice stuff. I will definitely bookmark your website.
You completed several good points there. I did a search on the subject and found nearly all folks will have the same opinion with your blog.
You have noted very interesting details! ps decent site.
As I website possessor I believe the content material here is rattling excellent , appreciate it for your hard work. You should keep it up forever! Good Luck.
Fantastic beat ! I would like to apprentice while you amend your site, how can i subscribe for a blog website? The account aided me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear concept
You really make it seem so easy with your presentation however I in finding this matter to be actually something which I feel I might never understand. It kind of feels too complex and extremely vast for me. I’m taking a look forward to your subsequent post, I will attempt to get the grasp of it!
I like the helpful information you provide in your articles. I’ll bookmark your weblog and check again here frequently. I am quite certain I’ll learn many new stuff right here! Best of luck for the next!
A person necessarily assist to make severely articles I’d state. This is the very first time I frequented your website page and to this point? I surprised with the analysis you made to make this particular publish extraordinary. Magnificent activity!
hello there and thank you for your information – I have certainly picked up something new from right here. I did however expertise some technical issues using this website, since I experienced to reload the site lots of times previous to I could get it to load correctly. I had been wondering if your web host is OK? Not that I’m complaining, but slow loading instances times will sometimes affect your placement in google and can damage your high-quality score if ads and marketing with Adwords. Well I’m adding this RSS to my e-mail and can look out for much more of your respective exciting content. Ensure that you update this again soon..
We are a group of volunteers and opening a new scheme in our community. Your website offered us with valuable information to work on. You’ve done an impressive job and our whole community will be thankful to you.
I was reading some of your content on this website and I believe this website is really instructive! Keep putting up.
I am continuously browsing online for ideas that can aid me. Thx!
I keep listening to the reports talk about getting boundless online grant applications so I have been looking around for the top site to get one. Could you advise me please, where could i find some?
Good information. Lucky me I came across your blog by chance (stumbleupon). I’ve bookmarked it for later!
Good – I should certainly pronounce, impressed with your website. I had no trouble navigating through all tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or something, web site theme . a tones way for your customer to communicate. Excellent task.
I¡¦ve been exploring for a little bit for any high quality articles or blog posts in this kind of house . Exploring in Yahoo I finally stumbled upon this website. Studying this information So i¡¦m satisfied to show that I’ve an incredibly just right uncanny feeling I discovered just what I needed. I most undoubtedly will make certain to do not put out of your mind this site and give it a glance regularly.
I have not checked in here for a while because I thought it was getting boring, but the last few posts are great quality so I guess I¡¦ll add you back to my everyday bloglist. You deserve it my friend 🙂
Hello.This post was extremely motivating, especially because I was browsing for thoughts on this topic last Wednesday.
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get got an shakiness over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly very often inside case you shield this increase.
Thanks for the sensible critique. Me and my neighbor were just preparing to do a little research about this. We got a grab a book from our local library but I think I learned more from this post. I’m very glad to see such wonderful info being shared freely out there.
Definitely, what a splendid website and revealing posts, I definitely will bookmark your blog.Best Regards!
You could definitely see your skills within the paintings you write. The arena hopes for even more passionate writers like you who are not afraid to say how they believe. All the time follow your heart. “A second wife is hateful to the children of the first a viper is not more hateful.” by Euripides.
I loved your blog article.Much thanks again. Much obliged.
I have been absent for a while, but now I remember why I used to love this website. Thank you, I’ll try and check back more often. How frequently you update your website?
I do trust all of the ideas you have introduced on your post. They are really convincing and will certainly work. Still, the posts are too quick for beginners. May just you please prolong them a little from subsequent time? Thank you for the post.
you’re in reality a just right webmaster. The site loading speed is amazing. It sort of feels that you’re doing any unique trick. Moreover, The contents are masterwork. you have done a wonderful process in this topic!
you’re in point of fact a good webmaster. The web site loading speed is amazing. It sort of feels that you’re doing any distinctive trick. In addition, The contents are masterwork. you’ve done a magnificent task in this matter!
I have to convey my appreciation for your kind-heartedness giving support to folks who have the need for guidance on this question. Your special commitment to getting the solution across became extremely valuable and has continually permitted most people much like me to get to their targets. Your amazing warm and friendly tutorial can mean a lot to me and far more to my office workers. Thanks a ton; from everyone of us.
Somebody essentially help to make critically articles I’d state. This is the first time I frequented your website page and thus far? I amazed with the analysis you made to make this particular submit extraordinary. Fantastic task!
I needed to write you a very little word in order to give thanks the moment again for all the unique knowledge you’ve discussed on this site. It’s simply wonderfully open-handed with you to convey openly exactly what a few people would have offered as an electronic book to help make some profit for themselves, specifically considering the fact that you might well have done it if you ever desired. The tips likewise served as the fantastic way to understand that the rest have a similar keenness the same as mine to learn a good deal more regarding this issue. I’m certain there are millions of more pleasurable instances ahead for individuals that looked at your blog.
Hello, Neat post. There’s a problem together with your website in web explorer, might check this… IE still is the marketplace chief and a huge element of other people will omit your great writing because of this problem.
In accordance with my study, after a property foreclosure home is sold at an auction, it is common for any borrower to be able to still have a remaining unpaid debt on the mortgage. There are many loan providers who try and have all costs and liens cleared by the upcoming buyer. Having said that, depending on specific programs, polices, and state laws and regulations there may be quite a few loans that aren’t easily resolved through the exchange of personal loans. Therefore, the responsibility still rests on the client that has acquired his or her property in foreclosure. Many thanks sharing your thinking on this website.
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored subject matter stylish. nonetheless, you command get got an nervousness over that you wish be delivering the following. unwell unquestionably come further formerly again as exactly the same nearly a lot often inside case you shield this hike.
Thank you for the sensible critique. Me and my neighbor were just preparing to do some research on this. We got a grab a book from our area library but I think I learned more clear from this post. I’m very glad to see such excellent information being shared freely out there.
Excellent post. I was checking constantly this blog and I’m impressed! Extremely helpful info specifically the last part 🙂 I care for such info much. I was seeking this particular info for a long time. Thank you and best of luck.
I¡¦ve learn several just right stuff here. Certainly price bookmarking for revisiting. I wonder how so much attempt you set to make any such magnificent informative web site.
Very interesting topic , regards for posting . “Nothing is more wretched than the mind of a man conscious of guilt.” by Titus Maccius Plautus.
Having read this I believed it was very informative. I appreciate you finding the time and effort to put this informative article together. I once again find myself spending a significant amount of time both reading and commenting. But so what, it was still worth it!
Thank you, I have just been looking for info about this subject for a while and yours is the greatest I have discovered till now. However, what concerning the conclusion? Are you certain about the source?
Whats Going down i’m new to this, I stumbled upon this I have found It positively helpful and it has aided me out loads. I am hoping to give a contribution & assist different customers like its helped me. Good job.
I do accept as true with all of the concepts you’ve presented for your post. They are really convincing and will definitely work. Still, the posts are very quick for novices. May you please lengthen them a little from next time? Thank you for the post.
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you can do with a few pics to drive the message home a little bit, but other than that, this is fantastic blog. A fantastic read. I will certainly be back.
Hello, i think that i saw you visited my web site so i came to “return the favor”.I am trying to find things to improve my site!I suppose its ok to use some of your ideas!!
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a little bit, but other than that, this is magnificent blog. A great read. I’ll definitely be back.
Great remarkable things here. I am very happy to look your post. Thanks so much and i am taking a look ahead to contact you. Will you please drop me a e-mail?
I love the efforts you have put in this, regards for all the great articles.
fantastic issues altogether, you simply won a new reader. What would you recommend in regards to your publish that you simply made a few days ago? Any positive?
Excellent weblog right here! Also your web site loads up fast! What web host are you using? Can I am getting your affiliate hyperlink to your host? I wish my site loaded up as fast as yours lol
I’m extremely impressed with your writing skills and also with the layout on your weblog. Is this a paid theme or did you modify it yourself? Either way keep up the nice quality writing, it’s rare to see a great blog like this one these days..
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our local library but I think I learned more from this post. I’m very glad to see such great info being shared freely out there.
Greetings, There’s no doubt that your web site could be having web browser compatibility issues. When I take a look at your site in Safari, it looks fine however, when opening in Internet Explorer, it’s got some overlapping issues. I just wanted to give you a quick heads up! Besides that, great blog!
I am continuously invstigating online for tips that can help me. Thank you!
Is it possible to copy and paste news articles for my blog or is that copyright infringement?
My brother recommended I might like this web site. He was totally right. This post truly made my day. You can not imagine just how much time I had spent for this information! Thanks!
I haven’t checked in here for some time since I thought it was getting boring, but the last few posts are great quality so I guess I’ll add you back to my everyday bloglist. You deserve it my friend 🙂
I definitely wanted to write down a brief comment to be able to say thanks to you for the magnificent instructions you are giving on this site. My time consuming internet lookup has at the end been paid with good facts to write about with my company. I would admit that most of us readers are undoubtedly fortunate to be in a wonderful site with many awesome professionals with very helpful pointers. I feel pretty grateful to have used the website page and look forward to really more thrilling minutes reading here. Thanks a lot once more for all the details.
Hey There. I found your blog using msn. This is an extremely well written article. I’ll make sure to bookmark it and come back to read more of your useful info. Thanks for the post. I will certainly comeback.
It is in reality a great and useful piece of information. I¡¦m happy that you shared this helpful info with us. Please keep us up to date like this. Thanks for sharing.
I happen to be commenting to make you be aware of what a exceptional encounter my friend’s daughter encountered reading your web page. She noticed some details, not to mention how it is like to possess a marvelous helping spirit to let others clearly fully grasp some tortuous issues. You really exceeded our own expected results. Thanks for rendering those interesting, healthy, informative and also easy thoughts on the topic to Jane.
wonderful issues altogether, you just gained a new reader. What might you recommend about your post that you just made a few days ago? Any positive?
There is noticeably a lot to identify about this. I consider you made some good points in features also.
What i do not understood is in reality how you’re not actually much more smartly-favored than you may be right now. You are very intelligent. You already know thus considerably in terms of this subject, produced me personally consider it from a lot of various angles. Its like women and men don’t seem to be involved except it is one thing to accomplish with Woman gaga! Your personal stuffs excellent. Always take care of it up!
Hello, i think that i saw you visited my weblog so i came to “return the favor”.I’m trying to find things to improve my website!I suppose its ok to use some of your ideas!!
I as well as my guys have already been examining the good things from the website while the sudden came up with an awful feeling I had not thanked the website owner for those strategies. The guys became for this reason warmed to read them and have in effect in actuality been having fun with these things. Thank you for indeed being considerably accommodating and for making a decision on some high-quality resources millions of individuals are really desirous to be aware of. My very own honest apologies for not saying thanks to earlier.
Great paintings! This is the kind of information that are meant to be shared around the internet. Shame on Google for not positioning this post higher! Come on over and discuss with my website . Thanks =)
Heya i’m for the first time here. I came across this board and I find It truly useful & it helped me out much. I hope to give something back and help others like you aided me.
Fantastic web site. A lot of useful information here. I¡¦m sending it to several pals ans additionally sharing in delicious. And naturally, thanks in your effort!
Merely wanna comment on few general things, The website pattern is perfect, the written content is rattling excellent : D.
I will right away grab your rss as I can’t in finding your email subscription link or newsletter service. Do you have any? Please let me know in order that I could subscribe. Thanks.
It’s perfect time to make some plans for the future and it is time to be happy. I have read this post and if I could I want to suggest you some interesting things or tips. Perhaps you could write next articles referring to this article. I desire to read even more things about it!
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how could we communicate?
Its like you read my mind! You seem to know so much about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a little bit, but other than that, this is excellent blog. A fantastic read. I will certainly be back.
You made some decent points there. I did a search on the topic and found most individuals will approve with your website.
excellent issues altogether, you simply won a new reader. What could you recommend in regards to your post that you simply made a few days ago? Any sure?
hello!,I like your writing very much! percentage we keep in touch extra approximately your article on AOL? I need a specialist in this area to unravel my problem. Maybe that’s you! Having a look forward to look you.
There is perceptibly a lot to know about this. I feel you made various good points in features also.
Nice read, I just passed this onto a friend who was doing some research on that. And he actually bought me lunch as I found it for him smile Therefore let me rephrase that: Thanks for lunch!
Wow! Thank you! I always wanted to write on my blog something like that. Can I include a part of your post to my site?
Fantastic goods from you, man. I have understand your stuff previous to and you’re just too magnificent. I actually like what you’ve acquired here, really like what you are saying and the way in which you say it. You make it entertaining and you still take care of to keep it wise. I can’t wait to read far more from you. This is really a wonderful web site.
I simply want to mention I am just new to blogging and site-building and honestly liked you’re page. More than likely I’m likely to bookmark your site . You really come with awesome posts. Cheers for revealing your web page.
Very efficiently written story. It will be valuable to everyone who usess it, as well as me. Keep doing what you are doing – looking forward to more posts.
Needed to create you one very small observation just to give many thanks yet again for those marvelous concepts you’ve shared in this article. It has been so generous of people like you to provide easily exactly what many individuals would’ve marketed as an ebook to earn some money for themselves, even more so seeing that you might have tried it if you ever desired. These things as well acted like the fantastic way to understand that other people online have the same zeal just like my personal own to know the truth more on the subject of this condition. I am sure there are lots of more fun sessions in the future for individuals who start reading your blog post.
Pretty nice post. I just stumbled upon your blog and wished to say that I’ve really enjoyed browsing your blog posts. After all I’ll be subscribing to your rss feed and I hope you write again soon!
Hello.This post was really fascinating, particularly because I was browsing for thoughts on this topic last week.
Good write-up, I am normal visitor of one¡¦s site, maintain up the nice operate, and It is going to be a regular visitor for a long time.
A lot of thanks for all your valuable work on this website. Gloria enjoys making time for research and it’s really easy to understand why. My partner and i know all regarding the dynamic form you deliver efficient tactics by means of your website and as well as boost participation from visitors on the matter and our own girl is without a doubt learning a whole lot. Have fun with the rest of the new year. You are always carrying out a really good job.
As I web-site possessor I believe the content material here is rattling fantastic , appreciate it for your hard work. You should keep it up forever! Best of luck.
Great ¡V I should certainly pronounce, impressed with your web site. I had no trouble navigating through all the tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Quite unusual. Is likely to appreciate it for those who add forums or something, website theme . a tones way for your client to communicate. Nice task..
It¡¦s actually a great and helpful piece of information. I am happy that you simply shared this useful info with us. Please keep us up to date like this. Thanks for sharing.
Good ¡V I should definitely pronounce, impressed with your site. I had no trouble navigating through all the tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your customer to communicate. Nice task..
Thank you for any other informative web site. Where else may I get that kind of information written in such a perfect means? I have a venture that I’m simply now running on, and I’ve been at the look out for such information.
Hi there, just became aware of your blog through Google, and found that it is truly informative. I am gonna watch out for brussels. I will appreciate if you continue this in future. Lots of people will be benefited from your writing. Cheers!
I like the helpful info you provide in your articles. I will bookmark your weblog and check again here regularly. I’m quite certain I will learn lots of new stuff right here! Best of luck for the next!
Wow! Thank you! I always needed to write on my blog something like that. Can I include a fragment of your post to my website?
Great info and right to the point. I don’t know if this is actually the best place to ask but do you folks have any ideea where to hire some professional writers? Thank you 🙂
Wow! Thank you! I constantly needed to write on my site something like that. Can I take a fragment of your post to my blog?
This is very interesting, You’re a very skilled blogger. I’ve joined your rss feed and look forward to seeking more of your great post. Also, I have shared your site in my social networks!
As soon as I found this site I went on reddit to share some of the love with them.
Today, while I was at work, my sister stole myiphone and tested to see if it can survive a30 foot drop, just so she can be a youtube sensation. My apple ipad is now destroyed and she has 83views. I know this is entirely off topic but I had to share itwith someone!
Excellent goods from you, man. I’ve understand your stuff previous to and you’re just too great. I actually like what you’ve acquired here, certainly like what you’re stating and the way in which you say it. You make it entertaining and you still care for to keep it smart. I can’t wait to read far more from you. This is really a terrific website.
I amI’m extremelyreally inspiredimpressed with yourtogether with youralong with your writing talentsskillsabilities and alsoas smartlywellneatly as with the layoutformatstructure for youron yourin yourto your blogweblog. Is thisIs that this a paid subjecttopicsubject mattertheme or did you customizemodify it yourselfyour self? Either wayAnyway staykeep up the niceexcellent qualityhigh quality writing, it’sit is rareuncommon to peerto seeto look a nicegreat blogweblog like this one these daysnowadaystoday..
Hi here, just started to be aware about your website through Search engine, and found that it is quite beneficial. I will truly appreciate should you continue on this informative article.
Pretty nice post. I just stumbled upon your blog and wanted to say that I have truly enjoyed browsing your blog posts. In any case I will be subscribing to your feed and I hope you write again soon!
I was just seeking this info for a while. After 6 hours of continuous Googleing, at last I got it in your website. I wonder what’s the lack of Google strategy that don’t rank this kind of informative web sites in top of the list. Usually the top sites are full of garbage.
It’s almost unattainable to find well-advised men and women on this content, still you seem like you fully understand exactly what you’re posting on! Gratitude
hello there and thank you for your info – I’ve certainly picked up something new from right here. I did however expertise a few technical issues using this web site, since I experienced to reload the web site lots of times previous to I could get it to load correctly. I had been wondering if your web hosting is OK? Not that I’m complaining, but sluggish loading instances times will very frequently affect your placement in google and could damage your high-quality score if ads and marketing with Adwords. Anyway I am adding this RSS to my e-mail and could look out for a lot more of your respective interesting content. Ensure that you update this again very soon..
You actually make it seem so easy with your presentation but I find this topic to be actually something that I think I would never understand. It seems too complex and very broad for me. I am looking forward for your next post, I’ll try to get the hang of it!
wonderful issues altogether, you simply received a new reader. What might you suggest in regards to your publish that you made some days ago? Any positive?
Its like you read my mind! You appear to know so much about this, like you wrote the book in it or something. I think that you can do with a few pics to drive the message home a bit, but instead of that, this is great blog. An excellent read. I will definitely be back.
I do love the manner in which you have framed this problem and it does indeed present me some fodder for thought. Nonetheless, from what I have witnessed, I simply hope as the actual opinions pack on that folks stay on point and in no way embark on a soap box regarding the news du jour. Still, thank you for this superb point and though I can not really go along with it in totality, I value the viewpoint.
I will immediately clutch your rss as I can’t to find your e-mail subscription link or e-newsletter service. Do you have any? Kindly allow me realize in order that I may subscribe. Thanks.
Simply desire to say your article is as surprising. The clarity in your post is just spectacular and i could assume you’re an expert on this subject. Well with your permission let me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please keep up the enjoyable work.
Im thankful for the post.Really looking forward to read more.
This is one awesome blog article.Really thank you! Want more.
What theme is this? Love it!
Hello my loved one! I want to say that this article is awesome, nice written and include approximately all significant infos. I would like to see more posts like this .
Fantastic beat ! I wish to apprentice while you amend your site, how can i subscribe for a weblog web site? The account aided me a applicable deal. I were a little bit acquainted of this your broadcast provided vivid transparent concept
Thanks for the auspicious writeup. It in reality used to be a entertainment account it. Glance advanced to far brought agreeable from you! By the way, how could we keep in touch?
What i do not realize is in reality how you are now not actually a lot more smartly-liked than you may be now. You are very intelligent. You realize therefore significantly on the subject of this subject, made me personally consider it from numerous various angles. Its like women and men aren’t involved except it¡¦s something to accomplish with Lady gaga! Your own stuffs excellent. At all times deal with it up!
You really make it seem really easy together with your presentation but I to find this topic to be actually one thing that I believe I might by no means understand. It kind of feels too complex and extremely huge for me. I’m taking a look ahead on your subsequent post, I¡¦ll attempt to get the hang of it!
Major thankies for the blog article.Really thank you! Awesome.
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point. You clearlydefinitelyobviously know what youre talking about, why wastethrow away your intelligence on just posting videos to your blogsiteweblog when you could be giving us something enlighteninginformative to read?
I could not refrain from commenting. Perfectly written!
Greetings! Very helpful advice in this particular post! It’s the little changes that make the most significant changes. Thanks for sharing!
I genuinely enjoy examining on this site, it holds wonderful posts . “You should pray for a sound mind in a sound body.” by Juvenal.
Good ¡V I should certainly pronounce, impressed with your web site. I had no trouble navigating through all tabs as well as related information ended up being truly simple to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, web site theme . a tones way for your client to communicate. Nice task..
wonderful put up, very informative. I ponder why the other experts of this sector do not notice this. You should continue your writing. I am sure, you’ve a huge readers’ base already!
Hello, Neat post. There’s a problem with your web site in web explorer, might test this… IE still is the marketplace leader and a good element of people will miss your great writing due to this problem.
Fantastic site. Lots of helpful information here. I’m sending it to several buddies ans additionally sharing in delicious. And of course, thank you for your effort!
Hello, Neat post. There is a problem along with your site in web explorer, might test this… IE nonetheless is the market leader and a large portion of other folks will pass over your magnificent writing due to this problem.
Thank you for sharing excellent informations. Your web-site is very cool. I’m impressed by the details that you have on this website. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for more articles. You, my pal, ROCK! I found just the info I already searched everywhere and simply couldn’t come across. What a great web site.
I gotta favorite this internet site it seems very beneficial handy
You are my intake, I own few blogs and very sporadically run out from brand :). “Follow your inclinations with due regard to the policeman round the corner.” by W. Somerset Maugham.
Thanks for sharing superb informations. Your website is so cool. I am impressed by the details that you have on this website. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for more articles. You, my pal, ROCK! I found just the information I already searched all over the place and just couldn’t come across. What a perfect website.
I know this if off topic but I’m looking into starting my own blog and was wondering what all is required to get set up? I’m assuming having a blog like yours would cost a pretty penny? I’m not very internet savvy so I’m not 100 positive. Any suggestions or advice would be greatly appreciated. Thanks
Hello, Neat post. There is a problem with your site in web explorer, would check this… IE nonetheless is the market chief and a huge part of other folks will pass over your great writing due to this problem.
I was studying some of your blog posts on this site and I think this site is very informative! Keep posting.
I am very happy to read this. This is the kind of manual that needs to be given and not the random misinformation that’s at the other blogs. Appreciate your sharing this best doc.
I am always looking online for posts that can help me. Thank you!
Its excellent as your other content : D, regards for posting . “A gift in season is a double favor to the needy.” by Publilius Syrus.
Everything is very open with a really clear clarification of the issues. It was truly informative. Your website is very helpful. Thanks for sharing!
Undeniably believe that which you stated. Your favorite justification appeared to be on the internet the simplest thing to be aware of. I say to you, I definitely get irked while people consider worries that they plainly do not know about. You managed to hit the nail upon the top and also defined out the whole thing without having side-effects , people could take a signal. Will probably be back to get more. Thanks
I like this website very much, Its a very nice position to read and obtain information. “Reason is not measured by size or height, but by principle.” by Epictetus.
Real fantastic information can be found on site . “An executive is a person who always decides sometimes he decides correctly, but he always decides.” by John H. Patterson.
You can certainly see your enthusiasm within the work you write. The arena hopes for even more passionate writers like you who aren’t afraid to mention how they believe. At all times follow your heart. “Until you’ve lost your reputation, you never realize what a burden it was.” by Margaret Mitchell.
Hi, Neat post. There’s a problem with your website in web explorer, may check this¡K IE nonetheless is the marketplace leader and a large component to folks will miss your wonderful writing because of this problem.
whoah this weblog is excellent i love studying your articles. Stay up the good work! You recognize, many people are hunting around for this info, you could help them greatly.
My spouse and i have been absolutely contented Albert could finish up his investigation out of the ideas he came across through the web site. It is now and again perplexing to just continually be releasing methods which usually many others might have been making money from. We figure out we need the writer to give thanks to for that. Most of the explanations you’ve made, the easy web site navigation, the friendships you will assist to foster – it is many great, and it is assisting our son in addition to the family feel that that content is awesome, which is unbelievably indispensable. Many thanks for all the pieces!
I appreciate you sharing this article. Awesome.
Very nice post. I just stumbled upon your blog and wished to say that I have truly enjoyed browsing your blog posts. After all I’ll be subscribing to your rss feed and I hope you write again soon!
I haven¡¦t checked in here for a while as I thought it was getting boring, but the last several posts are good quality so I guess I¡¦ll add you back to my daily bloglist. You deserve it my friend 🙂
This site definitely has all the information I wanted concerning this subject and didn’t know who to ask.
I would like to express thanks to this writer for rescuing me from such a trouble. Right after looking through the world-wide-web and getting tips that were not helpful, I believed my life was over. Existing devoid of the answers to the problems you have resolved through this write-up is a crucial case, as well as the ones which could have negatively damaged my entire career if I hadn’t discovered your blog. Your good talents and kindness in playing with all the stuff was tremendous. I don’t know what I would’ve done if I had not discovered such a solution like this. I’m able to now look forward to my future. Thanks a lot so much for this skilled and effective guide. I won’t be reluctant to propose your blog post to anyone who needs and wants recommendations on this subject.
You are my intake , I own few web logs and infrequently run out from to brand.
I have been absent for a while, but now I remember why I used to love this web site. Thanks , I¡¦ll try and check back more often. How frequently you update your website?
Some really superb info , Glad I observed this. “Now hatred is by far the longest pleasure men love in haste but they detest at leisure.” by George Gordon Byron.
Normally I do not read post on blogs, however I wish to say that this write-up very compelled me to check out and do it! Your writing style has been surprised me. Thank you, quite great article.
I like the helpful information you provide in your articles. I will bookmark your blog and check again here regularly. I am quite certain I’ll learn many new stuff right here! Best of luck for the next!
Great paintings! This is the kind of information that are meant to be shared around the internet. Disgrace on the search engines for no longer positioning this post higher! Come on over and discuss with my web site . Thanks =)
Hello, Neat post. There’s an issue together with your website in internet explorer, may test this… IE still is the market chief and a big element of folks will leave out your excellent writing because of this problem.
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You have made my day! Thx again
Definitely believe that which you said. Your favorite reason appeared to be on the internet the easiest thing to be aware of. I say to you, I definitely get irked while people consider worries that they plainly don’t know about. You managed to hit the nail upon the top and defined out the whole thing without having side effect , people could take a signal. Will likely be back to get more. Thanks
I dugg some of you post as I cerebrated they were extremely helpful very useful
You can definitely see your skills within the work you write. The sector hopes for more passionate writers such as you who are not afraid to mention how they believe. Always go after your heart. “The most profound joy has more of gravity than of gaiety in it.” by Michel de Montaigne.
Hey There. I found your blog using msn. This is a very well written article. I will make sure to bookmark it and come back to read more of your useful information. Thanks for the post. I will definitely return.
Its like you read my mind! You seem to know so much about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a bit, but other than that, this is wonderful blog. An excellent read. I will definitely be back.
I like the helpful information you provide in your articles. I will bookmark your blog and check again here regularly. I’m quite certain I’ll learn many new stuff right here! Good luck for the next!
What i do not understood is actually how you’re no longer really much more well-preferred than you may be right now. You’re so intelligent. You realize thus significantly relating to this subject, produced me for my part imagine it from a lot of numerous angles. Its like men and women aren’t interested except it is something to do with Lady gaga! Your own stuffs outstanding. At all times take care of it up!
My wife and i ended up being now thankful when Jordan could deal with his basic research through the entire ideas he got while using the weblog. It’s not at all simplistic to simply possibly be giving out hints which usually some people could have been selling. And we keep in mind we have the writer to give thanks to because of that. The entire illustrations you have made, the straightforward blog navigation, the friendships you can make it easier to foster – it is all impressive, and it is leading our son and us reason why the idea is interesting, which is exceptionally indispensable. Thank you for the whole lot!
you are truly a excellent webmaster. The website loading speed is amazing. It seems that you are doing any distinctive trick. Also, The contents are masterwork. you have done a excellent activity on this matter!
I’ll right away clutch your rss feed as I can’t to find your email subscription hyperlink or e-newsletter service. Do you have any? Kindly let me realize in order that I could subscribe. Thanks.
What i don’t understood is in reality how you’re not really a lot more well-preferred than you may be right now. You are very intelligent. You know therefore significantly in terms of this matter, produced me personally imagine it from so many varied angles. Its like men and women are not interested unless it’s one thing to do with Woman gaga! Your personal stuffs excellent. All the time handle it up!
Usually I do not read article on blogs, however I wish to say that this write-up very pressured me to try and do so! Your writing style has been surprised me. Thanks, quite great article.
I like this post, enjoyed this one appreciate it for posting .
Thank you so much for giving everyone remarkably pleasant possiblity to discover important secrets from this web site. It is usually very lovely and jam-packed with a good time for me personally and my office peers to visit your website a minimum of three times weekly to learn the new things you will have. And of course, I am also at all times satisfied with your very good information you serve. Certain 4 points in this article are absolutely the most efficient we have had.
I would like to thnkx for the efforts you have put in writing this site. I am hoping the same high-grade site post from you in the upcoming also. In fact your creative writing abilities has inspired me to get my own website now. Actually the blogging is spreading its wings quickly. Your write up is a great example of it.
I precisely had to thank you so much once again. I am not sure what I would have achieved in the absence of these pointers documented by you relating to such topic. It was actually the alarming crisis for me personally, nevertheless taking note of the specialised technique you handled it made me to weep over joy. I am grateful for your assistance and as well , believe you know what an amazing job you are undertaking training people with the aid of your web blog. I’m certain you haven’t encountered all of us.
Attractive section of content. I just stumbled upon your site and in accession capital to assert that I acquire actually enjoyed account your blog posts. Any way I will be subscribing to your feeds and even I achievement you access consistently quickly.
But a smiling visitor here to share the love (:, btw great layout.
I dugg some of you post as I cerebrated they were very helpful very helpful
you are truly a good webmaster. The web site loading pace is incredible. It kind of feels that you’re doing any unique trick. Also, The contents are masterpiece. you have done a fantastic task in this topic!
You really make it seem so easy with your presentation but I find this topic to be really something which I think I would never understand. It seems too complicated and extremely broad for me. I’m looking forward for your next post, I will try to get the hang of it!
You really make it seem so easy with your presentation but I find this matter to be actually something which I think I would never understand. It seems too complex and very broad for me. I’m looking forward for your next post, I’ll try to get the hang of it!
I simply wanted to say thanks yet again. I am not sure the things I would have followed in the absence of the actual information provided by you on this theme. It seemed to be the depressing circumstance for me personally, however , taking a look at a expert fashion you resolved it made me to cry over joy. Now i am happy for the support and even wish you recognize what a powerful job you are always accomplishing educating people today through the use of a site. I’m certain you have never encountered all of us.
It truly is almost close to impossible to encounter well-qualified people on this matter, then again you seem like you fully grasp what you’re revealing! Thanks A Lot
F*ckin’ tremendous things here. I’m very glad to see your post. Thanks a lot and i’m having a look forward to contact you. Will you please drop me a e-mail?
As soon as I noticed this web site I went on reddit to share some of the love with them.
I love the efforts you have put in this, regards for all the great articles.
I have recently started a site, the information you provide on this website has helped me tremendously. Thank you for all of your time & work.
I dugg some of you post as I cerebrated they were invaluable invaluable
You have noted very interesting points ! ps nice site. “Sutton lost 13 games in a row without winning a ballgame.” by Ralph Kiner.
Wow, incredible blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is fantastic, let alone the content!
magnificent points altogether, you simply gained a brand new reader. What might you suggest in regards to your publish that you just made a few days in the past? Any positive?
I believe that avoiding ready-made foods may be the first step so that you can lose weight. They will taste excellent, but ready-made foods have very little vitamins and minerals, making you take in more in order to have enough strength to get through the day. If you’re constantly consuming these foods, switching to cereals and other complex carbohydrates will let you have more energy while consuming less. Thanks alot : ) for your blog post.
Hi, i think that i saw you visited my site thus i came to “return the favor”.I’m trying to find things to improve my website!I suppose its ok to use some of your ideas!!
Say, you got a nice post.Really thank you! Keep writing.
Great blog here! Also your website loads up very fast! What web host are you using? Can I get your affiliate link to your host? I wish my site loaded up as fast as yours lol
I wanted to put you the bit of word just to thank you very much over again on the lovely views you have provided on this page. It is simply surprisingly open-handed of people like you to grant easily what a lot of people would’ve distributed as an e book to earn some profit for themselves, principally seeing that you could have done it in case you desired. The principles additionally worked to become good way to fully grasp that some people have similar fervor the same as my personal own to realize more and more with regards to this issue. Certainly there are lots of more pleasurable instances up front for folks who read carefully your blog post.
I just wanted to write a comment in order to express gratitude to you for the great solutions you are giving at this site. My extensive internet research has finally been honored with reputable insight to share with my company. I ‘d tell you that we website visitors are very endowed to dwell in a magnificent network with very many lovely people with valuable tips and hints. I feel extremely grateful to have discovered your entire website and look forward to so many more fun times reading here. Thanks once again for all the details.
fantastic post, very informative. I wonder why the other experts of this sector don’t notice this. You must continue your writing. I am confident, you have a great readers’ base already!
One thing I’d prefer to say is the fact before buying more computer memory, have a look at the machine in which it could be installed. If your machine is usually running Windows XP, for instance, a memory ceiling is 3.25GB. Installing over this would simply constitute some sort of waste. Be sure that one’s motherboard can handle the actual upgrade quantity, as well. Interesting blog post.
I discovered more new stuff on this losing weight issue. One issue is that good nutrition is tremendously vital if dieting. A tremendous reduction in junk food, sugary food, fried foods, sugary foods, pork, and whitened flour products could possibly be necessary. Holding wastes harmful bacteria, and harmful toxins may prevent targets for losing belly fat. While specified drugs temporarily solve the challenge, the bad side effects usually are not worth it, and so they never supply more than a non permanent solution. It can be a known incontrovertible fact that 95 of fad diet plans fail. Many thanks for sharing your opinions on this website.
Thanks for sharing excellent informations. Your web-site is very cool. I am impressed by the details that you’ve on this blog. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found just the information I already searched everywhere and just could not come across. What an ideal web-site.
Your house is valueble for me. Thanks!…
Thanks for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our area library but I think I learned more from this post. I am very glad to see such magnificent info being shared freely out there.
hi!,I like your writing so much! share we communicate more about your post on AOL? I need a specialist on this area to solve my problem. May be that’s you! Looking forward to see you.
I like what you guys are up too. Such clever work and reporting! Keep up the superb works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my site 🙂
Hey! Someone in my Facebook group shared this site with us so I came to give it a look. I’m definitely enjoying the information. I’m book-marking and will be tweeting this to my followers! Terrific blog and amazing style and design.
Thank you, I’ve recently been looking for info about this subject for ages and yours is the greatest I’ve discovered till now. But, what about the bottom line? Are you sure about the source?
I have learn a few excellent stuff here. Certainly value bookmarking for revisiting. I surprise how so much attempt you put to create one of these wonderful informative website.
I think this is a real great blog post.Much thanks again.
As I web-site possessor I believe the content material here is rattling magnificent , appreciate it for your efforts. You should keep it up forever! Best of luck.
Major thanks for the blog. Really Cool.
Anyone else having issues viewing this on mobile device?
Pretty nice post. I just stumbled upon your weblog and wished to say that I have really enjoyed browsing your blog posts. After all I’ll be subscribing to your rss feed and I hope you write again soon!
Very nice article and right to the point. I don’t know if this is actually the best place to ask but do you guys have any thoughts on where to get some professional writers? Thanks in advance 🙂
Good write-up, I am normal visitor of one¡¦s site, maintain up the nice operate, and It’s going to be a regular visitor for a long time.
Great ¡V I should certainly pronounce, impressed with your website. I had no trouble navigating through all tabs as well as related info ended up being truly simple to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your customer to communicate. Excellent task..
It’s an extremely amazing powerful resource that you’re offering and you just provide it away cost-free!! I that can compare with discovering websites ones understand the particular in providing you with fantastic learning resource for zero cost. We truly dearly loved examining this blog. Have fun here!
Howdy, would you mind letting me know which web host you’re utilizing? I’ve loaded your blog in 3 completely different web browsers, and I must say this blog loads a lot quicker then most. Can you suggest a good internet hosting provider at a reasonable price?
hey there and thank you for your information – I have definitely picked up anything new from right here. I did however expertise a few technical points using this site, since I experienced to reload the site lots of times previous to I could get it to load correctly. I had been wondering if your hosting is OK? Not that I’m complaining, but slow loading instances times will often affect your placement in google and can damage your quality score if advertising and marketing with Adwords. Anyway I’m adding this RSS to my email and can look out for a lot more of your respective interesting content. Make sure you update this again very soon..
I¡¦ve been exploring for a bit for any high quality articles or blog posts in this sort of space . Exploring in Yahoo I eventually stumbled upon this site. Studying this info So i am happy to show that I have an incredibly just right uncanny feeling I found out exactly what I needed. I such a lot definitely will make certain to do not put out of your mind this website and give it a look on a constant basis.
You are a very bright individual!
Its like you read my mind! You appear to know so much about this, like you wrote the book in it or something. I think that you can do with a few pics to drive the message home a bit, but other than that, this is fantastic blog. A fantastic read. I’ll definitely be back.
Hello there, just became alert to your blog through Google, and found that it is really informative. I am going to watch out for brussels. I will appreciate if you continue this in future. Many people will be benefited from your writing. Cheers!
hello!,I love your writing very much! proportion we be in contact more about your post on AOL? I require a specialist on this area to resolve my problem. Maybe that’s you! Looking forward to look you.
Magnificent goods from you, man. I have understand your stuff previous to and you’re just extremely wonderful. I really like what you have acquired here, really like what you are stating and the way in which you say it. You make it enjoyable and you still take care of to keep it wise. I cant wait to read far more from you. This is actually a terrific web site.
I will immediately grasp your rss feed as I can’t find your e-mail subscription link or newsletter service. Do you’ve any? Please allow me recognize so that I may just subscribe. Thanks.
great issues altogether, you simply gained a emblem new reader. What would you recommend in regards to your put up that you simply made some days in the past? Any positive?
Excellent goods from you, man. I’ve understand your stuff previous to and you’re just extremely wonderful. I really like what you have acquired here, certainly like what you are stating and the way in which you say it. You make it entertaining and you still care for to keep it smart. I cant wait to read much more from you. This is actually a tremendous site.
You actually make it seem really easy with your presentation but I in finding this topic to be really something that I believe I would by no means understand. It kind of feels too complicated and extremely vast for me. I’m having a look ahead to your next publish, I¡¦ll attempt to get the hang of it!
hey there and thank you for your information – I have certainly picked up something new from right here. I did however expertise a few technical points using this web site, since I experienced to reload the site lots of times previous to I could get it to load correctly. I had been wondering if your hosting is OK? Not that I am complaining, but slow loading instances times will sometimes affect your placement in google and can damage your high quality score if ads and marketing with Adwords. Anyway I am adding this RSS to my email and could look out for much more of your respective fascinating content. Make sure you update this again very soon..
Usually I don’t learn article on blogs, however I wish to say that this write-up very pressured me to take a look at and do so! Your writing taste has been amazed me. Thank you, very nice article.
great put up, very informative. I wonder why the opposite specialists of this sector do not understand this. You must proceed your writing. I am sure, you have a great readers’ base already!
I needed to compose you one very little word to help thank you very much the moment again regarding the pleasing concepts you’ve featured on this website. It is simply tremendously open-handed with people like you in giving openly precisely what a few people might have marketed for an e-book to generate some money for themselves, notably considering the fact that you could possibly have tried it if you ever desired. Those tactics additionally acted to become fantastic way to fully grasp other people have the same keenness like my personal own to realize good deal more around this issue. I know there are numerous more fun times ahead for those who read carefully your blog.
Thank you for making the honest attempt to discuss this. I feel very strong about it and would like to learn more. If it’s OK, as you gain extra in depth knowledge, might you mind adding more articles very similar to this one with more information? It would be extraordinarily useful and useful for me and my friends.
Thank you for sharing superb informations. Your web site is very cool. I’m impressed by the details that you have on this web site. It reveals how nicely you understand this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found just the information I already searched everywhere and simply could not come across. What an ideal website.
Normally I don’t read an article on blogs, however, I would like to say that this write-up on this worth-sharing article very pressured me to try and do so!
Good writing skills here, I like it 🙂
I believe there are many more pleasurable opportunities ahead for individuals that looked at your site.
Woah this is just an insane amount of information, must of taken ages to compile so thanx so much for just sharing it with all of us. If your ever in any need of related information, perhaps a bit of coaching, seduction techniques or just general tips, just check out my own site!
I would like toI mustI’d like toI have to thank you for the efforts you haveyou’ve put in writing thispenning this blogwebsitesite. I am hopingI’m hopingI really hope to seeto viewto check out the same high-grade blog postscontent from youby you in the futurelater on as well. In factIn truth, your creative writing abilities has inspiredmotivatedencouraged me to get my ownmy very ownmy own, personal blogwebsitesite now 😉
I cling on to listening to the news bulletin talk about receiving free online grant applications so I have been looking around for the top site to get one. Could you tell me please, where could i get some?
It’s a shamepity you don’t have a donate button! I’d most certainlywithout a doubtcertainlydefinitely donate to this superbbrilliantfantasticexcellentoutstanding blog! I supposeguess for now i’ll settle for book-markingbookmarking and adding your RSS feed to my Google account. I look forward to freshbrand newnew updates and will talk aboutshare this blogsitewebsite with my Facebook group. ChatTalk soon!
Here is a superb Blog You might Find Interesting that we Encourage You
Nice post. Thank you!
Hello to every one, the contents present at this website are in fact awesome for people knowledge, well, keep up the good work fellows.|
Hey! This information is amazing <3 I will recommend it to my son and any person that could be interested in this topic. Great work girls 🙂
I wanted to thank you for this excellent read!! I definitely loved every little bit of it. I have you bookmarked your site to check out the new stuff you post.
I do agree with all of the concepts you’ve presented on your post. They are really convincing and can definitely work. Still, the posts are too short for newbies. May you please prolong them a little from next time? Thank you for the post.
I wanted to thank you for this excellent read!! I definitely loved every little bit of it. I have you bookmarked your site to check out the new stuff you post.
I like this website very much, Its a very nice post to read and get information. “Reason is not measured by size or height, but by principle.” by Epictetus.
I think that thanks for the valuabe information and insights you have so provided here.
Way cool! Some veryextremely valid points! I appreciate you writing thispenning this articlepostwrite-up and theand also theplus the rest of the site iswebsite is also veryextremelyveryalso reallyreally good.
You actually did greater than people’ expectations. Thank you for rendering these helpful, trusted, edifying and also trendy thoughts on the topic to Kate.
I truly adore the theme/design of your website. Do you ever run into any browser compatibility problems? A small number of my website audience have whined about my website not functioning properly in Explorer but looks great in Safari. Have you got any suggestions to help fix this problem?
That I ‘d mention that nearly all of us people are endowed to exist at a fantastic place with quite many wonderful individuals with quite helpful things.
Thanks for all of the labor on this web site. Debby really likes doing research and it is easy to understand why. All of us notice all relating to the dynamic medium you convey very useful thoughts by means of this website and as well cause response from other people on this area so our own daughter is without a doubt being taught a whole lot. Take advantage of the rest of the year. You’re carrying out a fantastic job.
I merely desire to inform you that I am new to putting up a blog and totally adored your write-up. Quite possibly I am going to store your blog post . You undoubtedly have extraordinary article information. Get Pleasure From it for swapping with us your main site page
Have you ever thought about creating an e-book or guest authoring on other blogs? I have a blog centered on the same topics you discuss and would really like to have you share some stories/information. I know my audience would value your work. If you’re even remotely interested, feel free to shoot me an e mail.
I’ve bookmarked your site, and I am adding your RSS feeds to my Google account. {
Needed to compose you a very little word to thank you yet again regarding the nice suggestions you’ve contributed here.
that’s why I bookmarked this page for get news feed with perfectly information in the next coming post ,
I found so many interesting stuff in your blog especially its discussion. From the tons of comments on your articles, I guess I am not the only one having all the enjoyment here! keep up the good work..
I would like toI mustI’d like toI have to thank you for the efforts you haveyou’ve put in writing thispenning this blogwebsitesite. I am hopingI’m hopingI really hope to seeto viewto check out the same high-grade blog postscontent from youby you in the futurelater on as well. In factIn truth, your creative writing abilities has inspiredmotivatedencouraged me to get my ownmy very ownmy own, personal blogwebsitesite now 😉